 11 min read
SOC Prime Platform
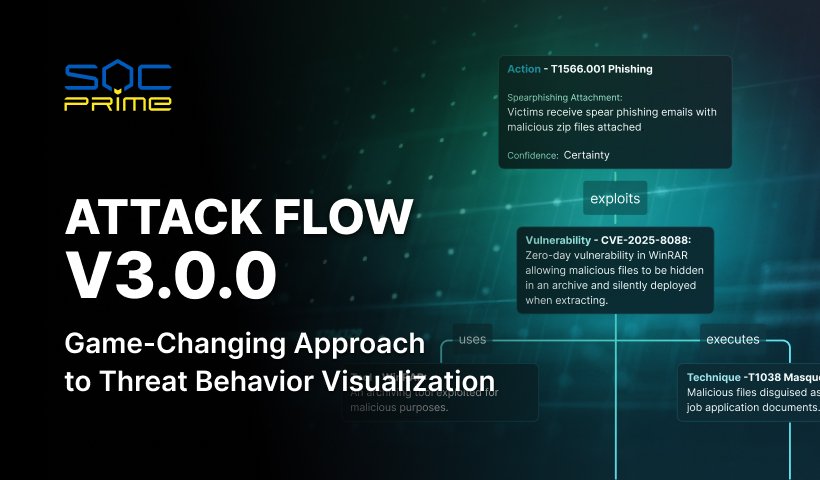
MITRE Attack Flow v3.0.0
11 min read
SOC Prime Platform
MITRE Attack Flow v3.0.0
 2 min read
SOC Prime Platform
Save Detection Code & Metadata to Custom Repositories
2 min read
SOC Prime Platform
Save Detection Code & Metadata to Custom Repositories
 2 min read
SOC Prime Platform
Convenient Detection Code Editor for Uncoder AI
2 min read
SOC Prime Platform
Convenient Detection Code Editor for Uncoder AI
 2 min read
SOC Prime Platform
Supercharge Detection Content into Roota Format with AI
2 min read
SOC Prime Platform
Supercharge Detection Content into Roota Format with AI
 2 min read
SOC Prime Platform
Uncoder AI Automates MITRE ATT&CK Tagging in Sigma Rules
2 min read
SOC Prime Platform
Uncoder AI Automates MITRE ATT&CK Tagging in Sigma Rules
 2 min read
SOC Prime to Present at 2025 MITRE ATT&CK® Community Workshop
2 min read
SOC Prime to Present at 2025 MITRE ATT&CK® Community Workshop
 2 min read
SOC PRIME TO PRESENT AT THE TWELFTH EU MITRE ATT&CK® COMMUNITY WORKSHOP
2 min read
SOC PRIME TO PRESENT AT THE TWELFTH EU MITRE ATT&CK® COMMUNITY WORKSHOP
 3 min read
SOC Prime Platform Now Supports the MITRE ATT&CK® Framework v14.1
3 min read
SOC Prime Platform Now Supports the MITRE ATT&CK® Framework v14.1
 4 min read
SOC Prime Becomes a Benefactor of MITRE ATT&CK®
4 min read
SOC Prime Becomes a Benefactor of MITRE ATT&CK®
 7 min read
Interview
Driving Business Growth in Turbulent Times from the Perspective of SOC Prime’s CEO: Part II
7 min read
Interview
Driving Business Growth in Turbulent Times from the Perspective of SOC Prime’s CEO: Part II