Loading legitimate system drivers from illegitimate or suspicious directories is a known tactic for persistence, evasion, or execution by adversaries. One high-value target in this category is clfs.sys — a legitimate Windows driver tied to the Common Log File System.
To detect this activity, Microsoft Defender for Endpoint supports advanced KQL-based detection logic. But to truly operationalize these queries, analysts need visibility into how they work. That’s exactly what Uncoder AI’s AI-generated Decision Tree delivers.
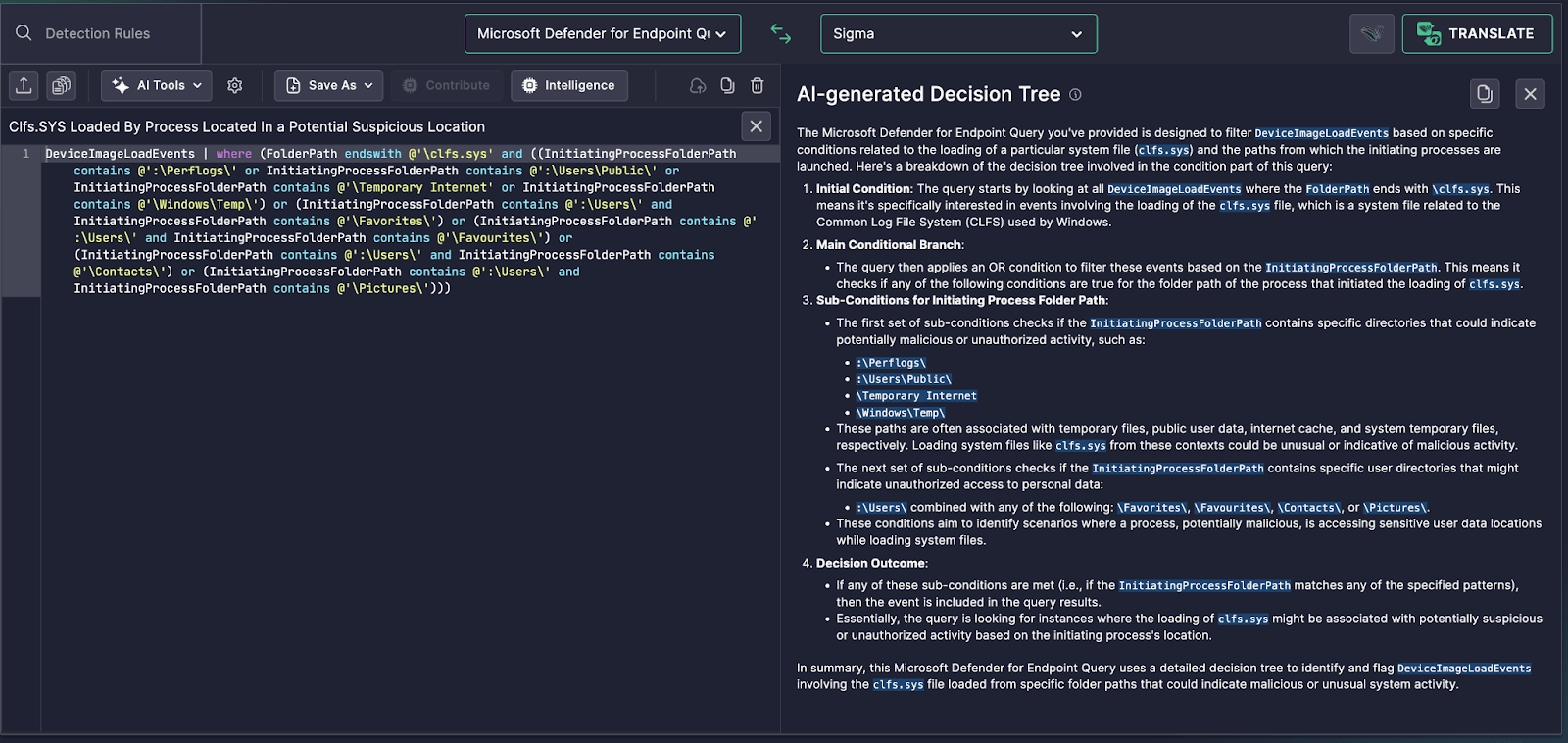
Use Case: clfs.sys Loaded From User or Temp Paths
This query identifies when clfs.sys is loaded from non-standard or user-controlled directories, which may include:
\Users\Public\\Temporary Internet\\Windows\Temp\- Subfolders under
\Users\such as\Pictures\,\Contacts\, or\Favourites\
These paths are rarely expected to host or initiate the loading of system-level drivers, making such activity highly suspicious.
How the Decision Tree Breaks It Down
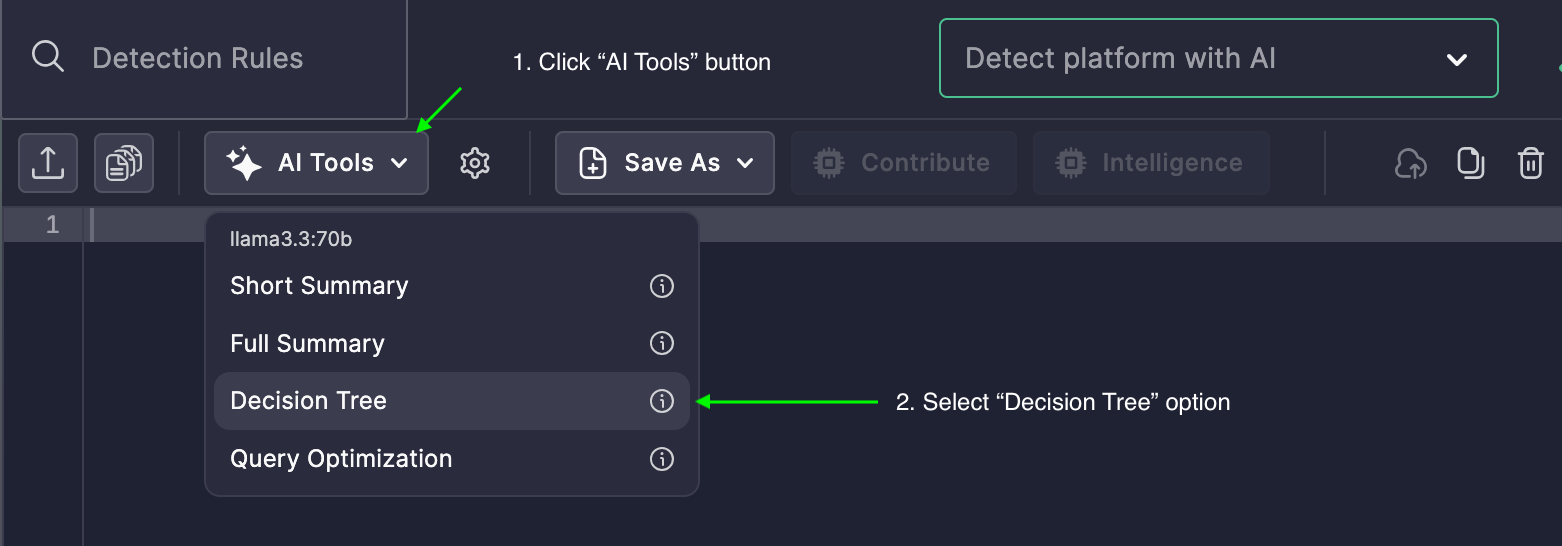
Uncoder AI automatically transforms this detection logic into a human-readable decision tree structure, showing:
-
Query Scope:
It filters fromDeviceImageLoadEventswhere the folder path ends withclfs.sys. -
Folder Path Conditions:
The decision tree checks whether the initiating process’s folder path contains any unusual user or temporary storage locations. -
Branching Conditions:
Sub-branches clarify which paths are considered:- Generic temp or cache folders
- User-specific locations that imply personal data access
- Combined conditions like
\Users\+\Favourites\or\Pictures\
- Outcome:
If any one of these conditions is met, the event is marked as relevant—flagging a potential misuse ofclfs.sysfrom suspicious origin paths.
Why This Matters
- Elevated Context: Analysts no longer need to decipher layered OR conditions to understand risk coverage.
- Faster Triage: You can see in seconds whether the rule catches temp path misuse, user folder abuse, or both.
- Audit-Ready Logic: The tree-style breakdown supports easier documentation and SOC training efforts.
Ultimately, loading clfs.sys from outside its expected system directories may represent driver abuse, living-off-the-land tactics, or malware masquerading as legitimate processes.
From Folder Flags to Threat Defense
Uncoder AI’s Decision Tree takes verbose KQL and turns it into an intuitive, SOC-friendly format. Whether you’re tuning this rule, hunting for anomalies, or explaining detection logic to leadership—this feature makes it actionable.