Step-by-Step Guidelines
SOC Prime continuously evolves partnership with Chronicle to provide Threat Detection Marketplace users leveraging Google Cloud’s security analytics platform with curated YARA-L 2.0 detections tailored to hunt out threats at Google speed. Currently, our Detection as Code platform offers 500+ Community YARA-L rules written by the SOC Prime Team. Also, Chronicle customers can access these free detections at Chronicle GitHub repository powered by the Chronicle Detect rules engine.
To assist you in deploying the existing detection content to your environment and streamline the process of rule creation, we are expanding the list of online educational resources available for free in our Cyber Library. This write-out gives a short overview and some useful tips for the Chronicle rule creation process. To reach the full Chronicle rule creation guide, log in to your Cyber Library account, choose Google Chronicle from the suggested list of platforms, and switch to the Rule tab.
YARA-L Rule Format
Google Chronicle is a cloud-based security analytics platform that works with the YARA-L language. This language is used to create rules for threat detection through enterprise environments. The most relevant thing about YARA-L and Chronicle is that it allows you to search for threats across a very large volume of data. It is worth noting that YARA-L and YARA are two different things. The first one was created in order to work with Chronicle and the second one (created by Virus Total) was crafted for data querying and “malware classification.”
Google Chronicle Rule Creation
Getting Started
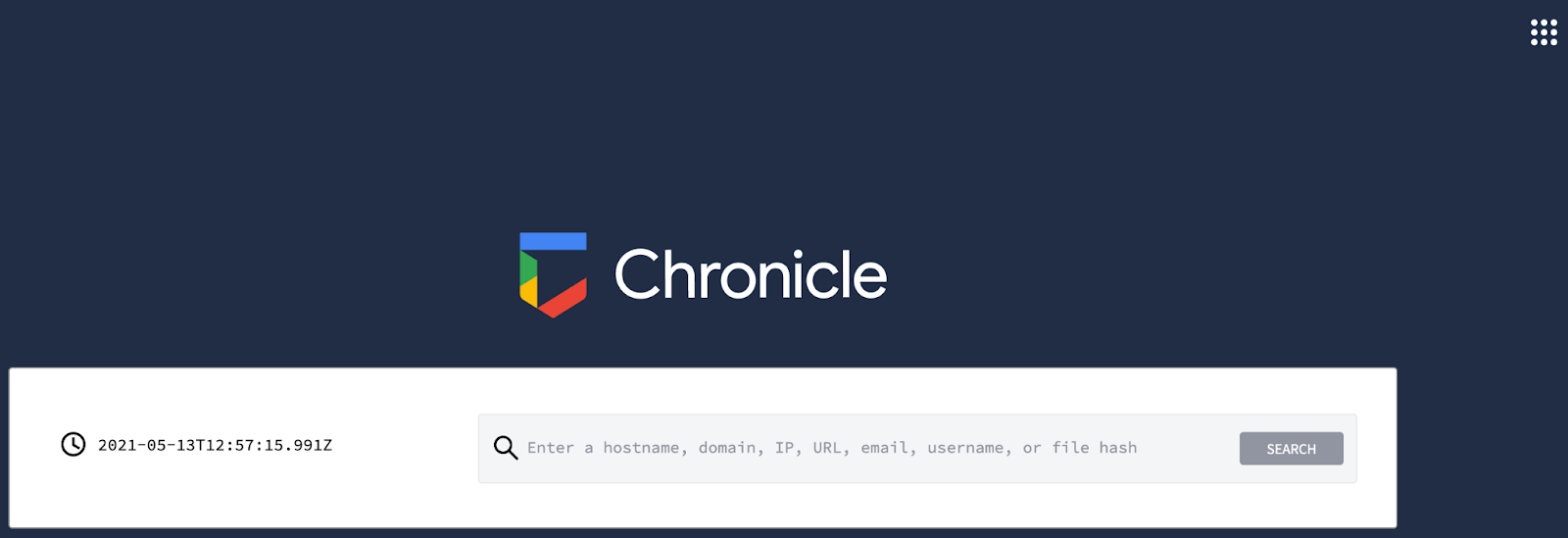
To start creating your own Google Chronicle rules, first, you need to log in to the Chronicle instance. After logging in, you’ll see this screen:
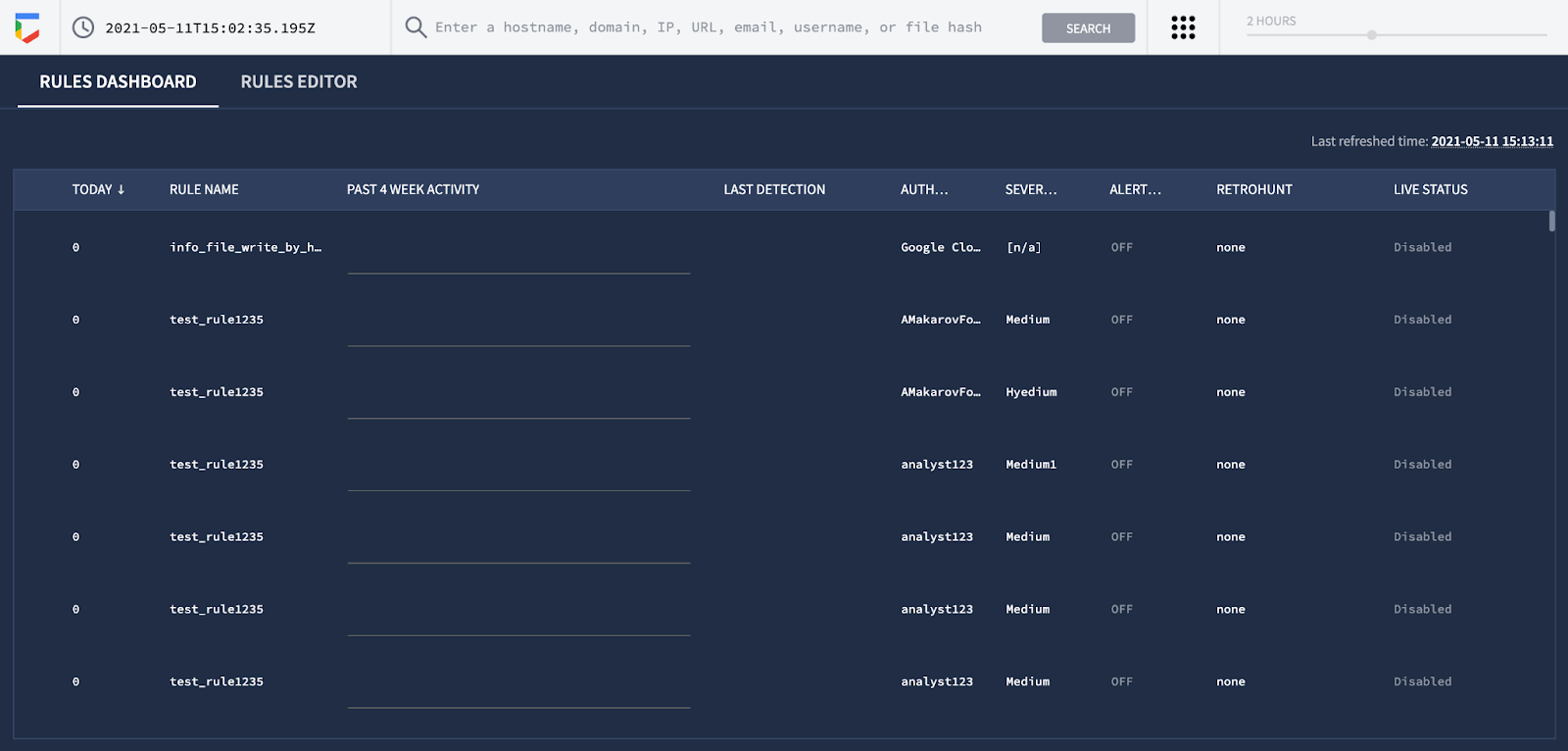
Then, move to the top-right corner of the screen and select View Rules from the action menu:
Next, select the Rules Editor tab:
After switching to the Rules Editor tab, click the New button.
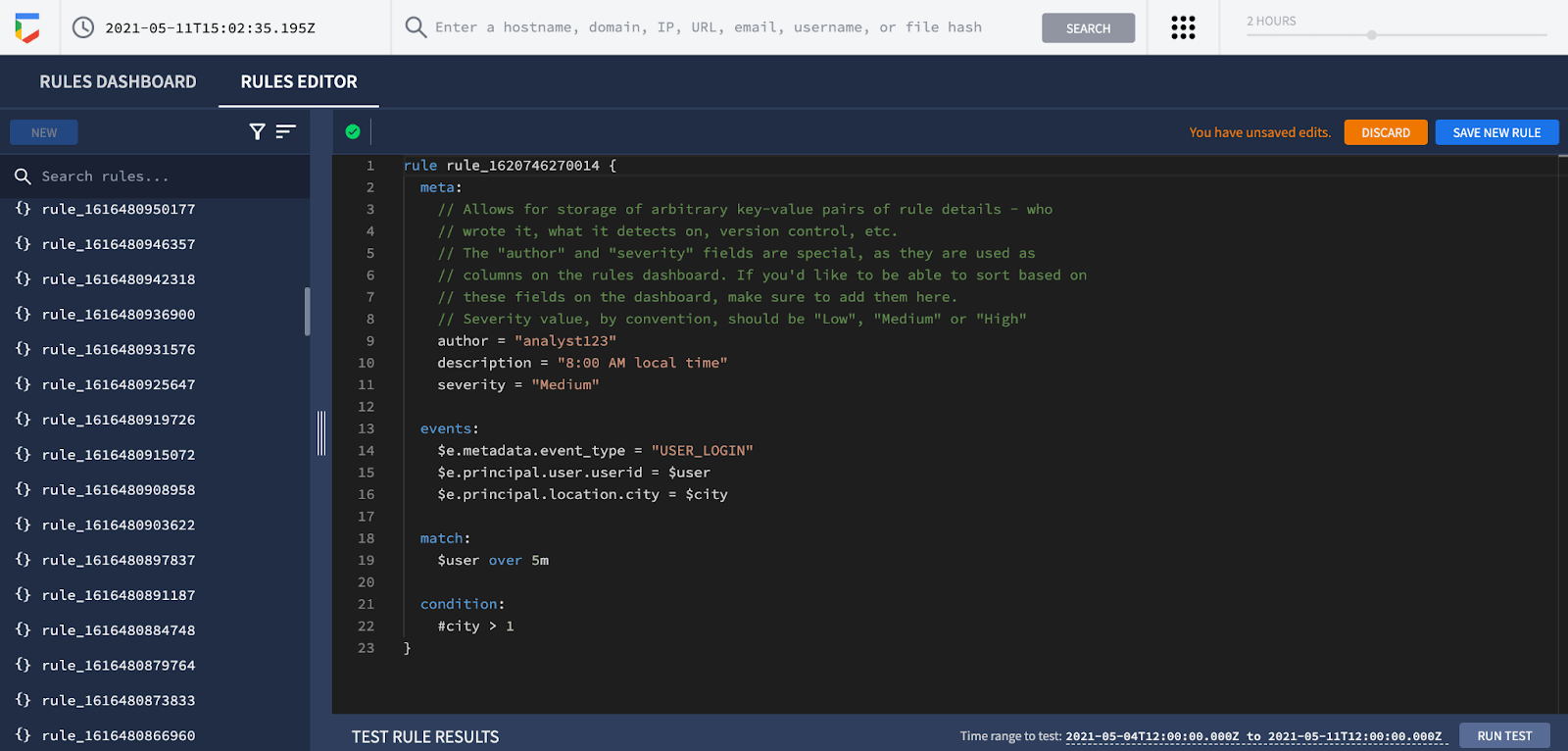
That’s it, you’re in the Google Chronicle rule wizard and can start building your own rule.
Parameters for Creating Google Chronicle Rules
To create a Google Chronicle correlation rule (or a YARA-L-based rule), you need to provide the following rule parameters as a basic starting point:
- Rule
- Meta
- Events
- Match (optional)
- Condition
Rule
The Rule section is the first interaction with our future and potential rule. Here you need to provide a descriptive rule name to streamline your search for it across the list of other detections.

Meta
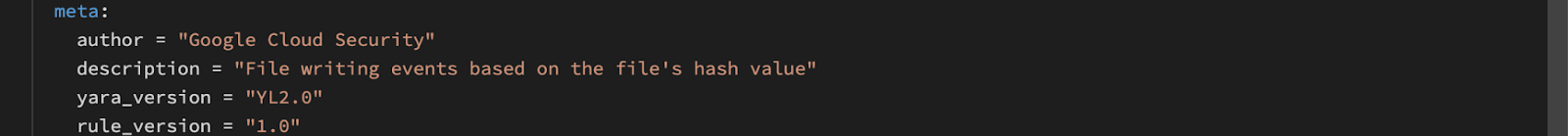
The Meta section contains rule specifications. Here you can provide the following details as the corresponding key-value pairs:
- Author of the rule
- Rule creation date
- Brief rule description
- Product information (e.g., Windows)
Events
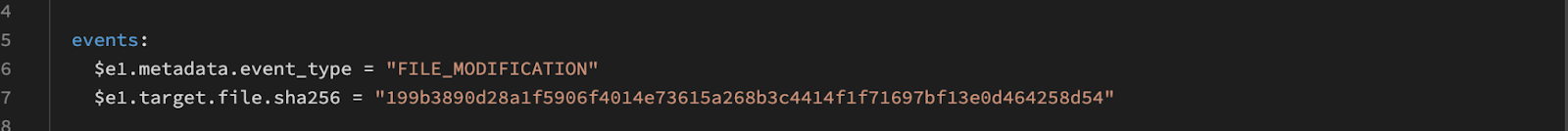
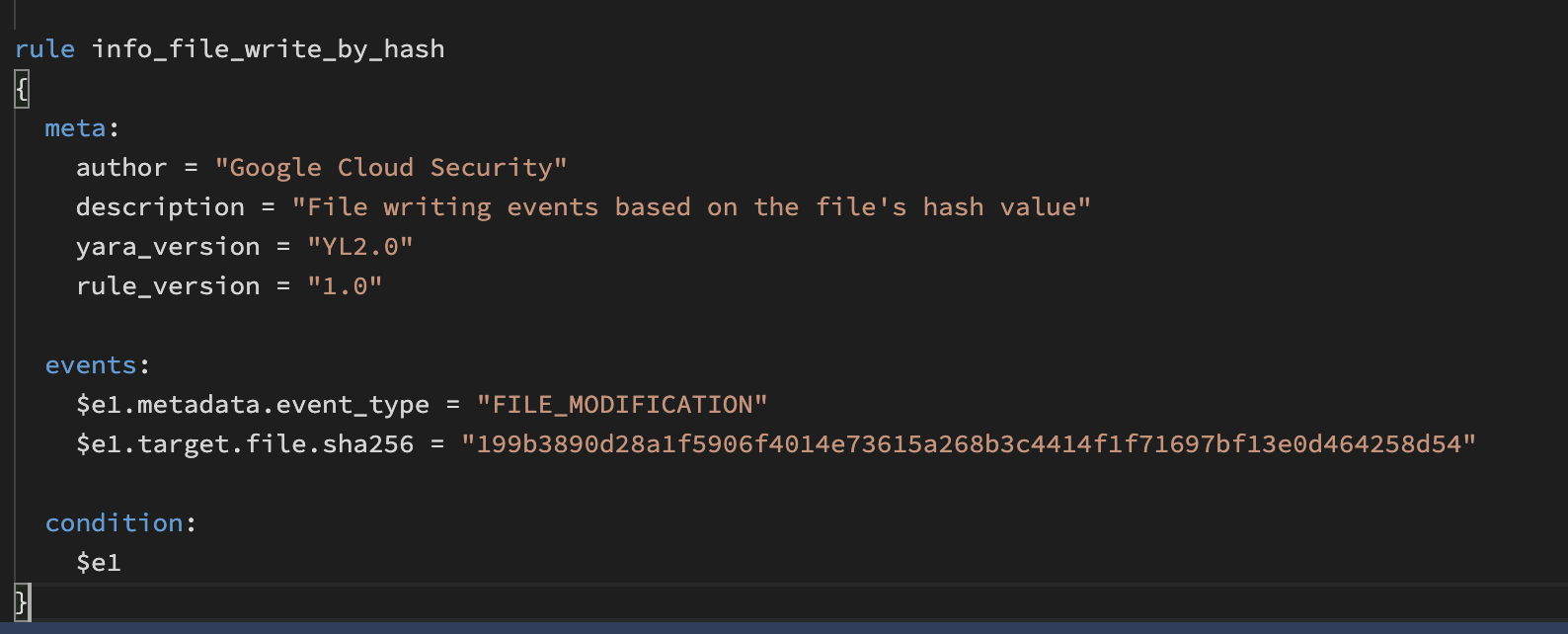
The Events section contains the information about the specific Google Chronicle alerts that the rule is searching for. Explicitly, here you need to specify the logic of what you want to detect with this particular rule. This section normally includes a significant number of different conditions and variables. For example, if you want to search for a File Modification situation (e.g., a malicious filename, or extension related to a threat), you’ll use this kind of logic:
events:
$e1.metadata.event_type = “FILE_MODIFICATION”
$e1.target.file.sha256 = “any hash”
In this case, the FILE_MODIFICATION value is related to the specific action that this rule is searching for. For example, a legitimate file modified by a threat actor:
Match
The Match section returns values when the relevant matches are found. This section is useful when you want to search for events in a specific time period. For example:
$value1, $value2 over 2m
First of all, $value1 and $value2 need to be declared in the Events section. Then, these variables should have values that occur in the chosen time period, so the rule can exclude the rest of the events. In other words, the Match section helps you purge events and be more specific.

Condition
In the Condition section, you can specify the match condition over events and variables defined in the Events section. Here you can join all the predicates using “and” / “or” operators. For example:
$e1 and $value1

Rule
As a result, you’ll get the following rule created by means of the Chronicle Detect rules engine with the corresponding parameters:
Recommendations
To delve deeper into the YARA-L language and the Google Chronicle rule creation process, read the corresponding documentation on the Chronicle Detect rules engine. To hone your detection skills, start playing with some rules and compare their structure with the source code available in the Chronicle’s GitHub Repo. Also, you can find 500+ YARA-L rules developed by the SOC Prime Team in Threat Detection Marketplace.
References
- https://github.com/chronicle/detection-rules
- https://go.chronicle.security/hubfs/YARA-L%20Overview%20White%20Paper.pdf
- https://socprime.com/news/boost-your-google-chronicle-platform-with-soc-prime-detection-rules/
- https://chroniclesec.medium.com/new-soc-prime-detection-rules-available-in-chronicle-434605aa0287
- https://cloud.google.com/blog/products/identity-security/introducing-chronicle-detect-from-google-cloud
Explore Threat Detection Marketplace to reach an extensive collection of SIEM and EDR algorithms tailored to the organization’s environment and threat profile, including 500+ YARA-L 2.0 detections for your Chronicle instance. Striving to master your threat hunting skills? Join our Cyber Library to get direct access to cybersecurity knowledge with insightful how-to guides for various SIEM, EDR, and NTDR solutions and deep dive online webinars.