Simplify Threat Investigation with a Single UI for All Threat Hunters, Right Within Your Browser
The Prime Hunt is an open-source browser extension that acts as the industry-first platform-agnostic UI for all threat hunters, no matter what SIEM or EDR they use. The tool enables security engineers to quickly convert, apply, and customize detection code across the widest stack of SIEM and EDR — directly within their Chrome, Firefox, or Edge browser. A wide variety of security toolkits makes it harder to collaborate for threat hunters who speak different query languages and work in diverse environments with their specific interfaces. With The Prime Hunt, teams can concentrate on the hunt itself by breaking through UI and language limitations.
The Prime Hunt is an open-source Lesser General Public License (LGPL) browser add-on that extends the success of Sigma and Roota open-source languages for threat hunting into a single UI solution. With this add-on, users can easily see which accounts and assets are affected by the suspicious activity detected by the query, single-click to filter query results by any field values that their SIEM or EDR provides, or look for all discovered events. Drill down to CTI or any other external sources that can contribute to your research, like VirusTotal, Anomali, EchoTrail, OpenCTI, or Ultimate IT Security to gain a holistic cyber threat context and proactive visibility into cyber defense gaps. The Prime Hunt integration with AbuseIPDB allows cyber defenders to report abusive IP addresses linked to suspicious cyber activities, improving the safety of online operations, while integration with the Shodan search engine allows mapping and collecting data about internet-connected devices and systems. The Prime Hunt also supports a range of projects powered by abuse.ch, providing community-driven threat intelligence on cyber threats to enhance protection against malware and botnets.
Leveraging the Prime Hunt, security engineers can start crafting detection code directly from their browsers and then rely on Uncoder AI to tweak the code and automatically translate it to multiple query languages. The refined detections can then be immediately deployed to a chosen SIEM, stored in a custom repository on the SOC Prime Platform via SOC Prime API integration, or saved in a private GitHub repo to keep all detection code in sync. This allows cyber defenders to eliminate the burden of manual security operations while speeding up the entire CI/CD workflow and accelerating the use case management lifecycle.
As the world stands on the brink of a global cyber war, defenders should fight together to combat emerging threats successfully. Inspired by the power of collective cyber defense, we created The Prime Hunt, a technology-agnostic UI for all Blue Teamers that enables scalable threat hunting processes across the rapidly growing environment. A free, open-source-based add-on, available right within your browser. Create pull requests to contribute via GitHub to develop the extension further and make The Prime Hunt capable of everything the defenders need. Let’s build the future of threat hunting and detection, together.
Andrii Bezverkhyi, Founder, CEO and Chairman at SOC Prime
Each SIEM or EDR interface is different, it applies a unique query language, and it’s not always user-friendly. For hard-battled cybersecurity experts who have been in the industry for many years, speaking multiple query languages is not a big deal. However, it might be a stumbling block for newcomers to threat hunting. Still, we need to enable them to hone their skills and contribute to collective cyber defense. The Prime Hunt bridges the gap between multiple tools and query languages. Simpler and faster than going into every tool, this is the future of threat hunting and threat detection. Another advantage is that aspiring threat hunters can learn Sigma & Roota on GitHub and work in the UI to generate some specific language gradually mastering KQL and SPL skills to bolster their skills and join the ranks of cyber defenders.
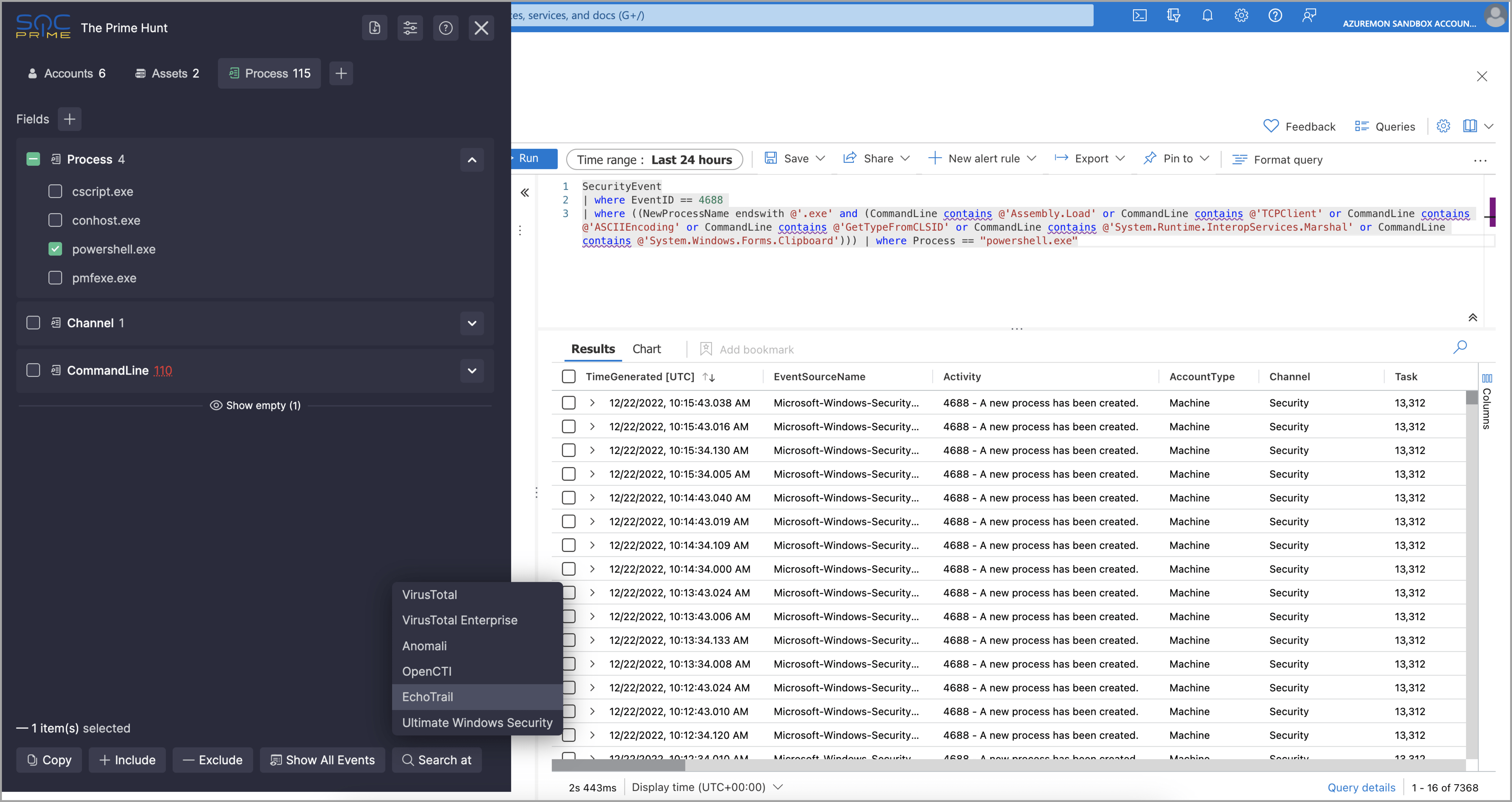
The Prime Hunt currently supports Microsoft Sentinel, Microsoft Defender for Endpoint, Splunk, Elastic, IBM QRadar, ArcSight, Falcon Logscale, Amazon Athena, Amazon OpenSearch, and Chronicle Security. This means you can now paste Sigma rule translations from Uncoder or any toolkit you’re using while analyzing hits and matches with the same UI across these supported platforms. We’re continuously expanding the list of integrations to make your threat hunting experience faster and simpler than ever before, regardless of the tool you use. To stay on top of the latest updates and enhancements, check out a dedicated GitHub for the latest releases.
The Prime Hunt currently supports the ability to track custom fields and customize the field grouping for an even more streamlined threat investigation. For more convenience, we’ve also improved the user experience by adding an ability to show or hide fields without values and introduced hotkeys to shave seconds off your hunts.
The add-on is built-in in your browser, all the code runs in your browser, and all your data belongs to you — actually, we do not have any of your data as The Prime Hunt does not send anything anywhere. You should verify this by inspecting the add-on source code at our GitHub repo.
As an open-source project, we believe that peer-driven contribution shapes the future of collective cyber defense. Anyone can contribute with a pull request at GitHub to express their voice and enrich the collective industry expertise.
Striving to gain more from collective cyber defense? Rely on SOC Prime´s product suite for Advanced Detection Engineering, Automated Threat Hunting & Detection Stack Validation to equip your team with the best tooling to combat cyber threats before they escalate. Join our Threat Bounty crowdsourcing initiative to polish your cybersecurity skills and receive financial benefits for contributing to the collective good. Tap into our open-source projects, like Uncoder IO, Roota, and The Prime Hunt to take cyber defense to the next level.