Instantly Explore the Executable Binary References Linked to Sigma Rules for More Insightful Contextual Information
SOC Prime has recently released integration for its cyber threats search engine with EchoTrail.io database. Now, SOC Prime users can streamline threat investigation with the comprehensive information about executable binaries (filenames or hashes) launched on Windows, accessible right from our search engine interface. EchoTrail.io serves as the executable behavioral analytics enabling Security Analysts, Threat Hunters, and other InfoSec practitioners to browse the extensive database of filenames and hashes and explore how Windows processes behave in the wild.
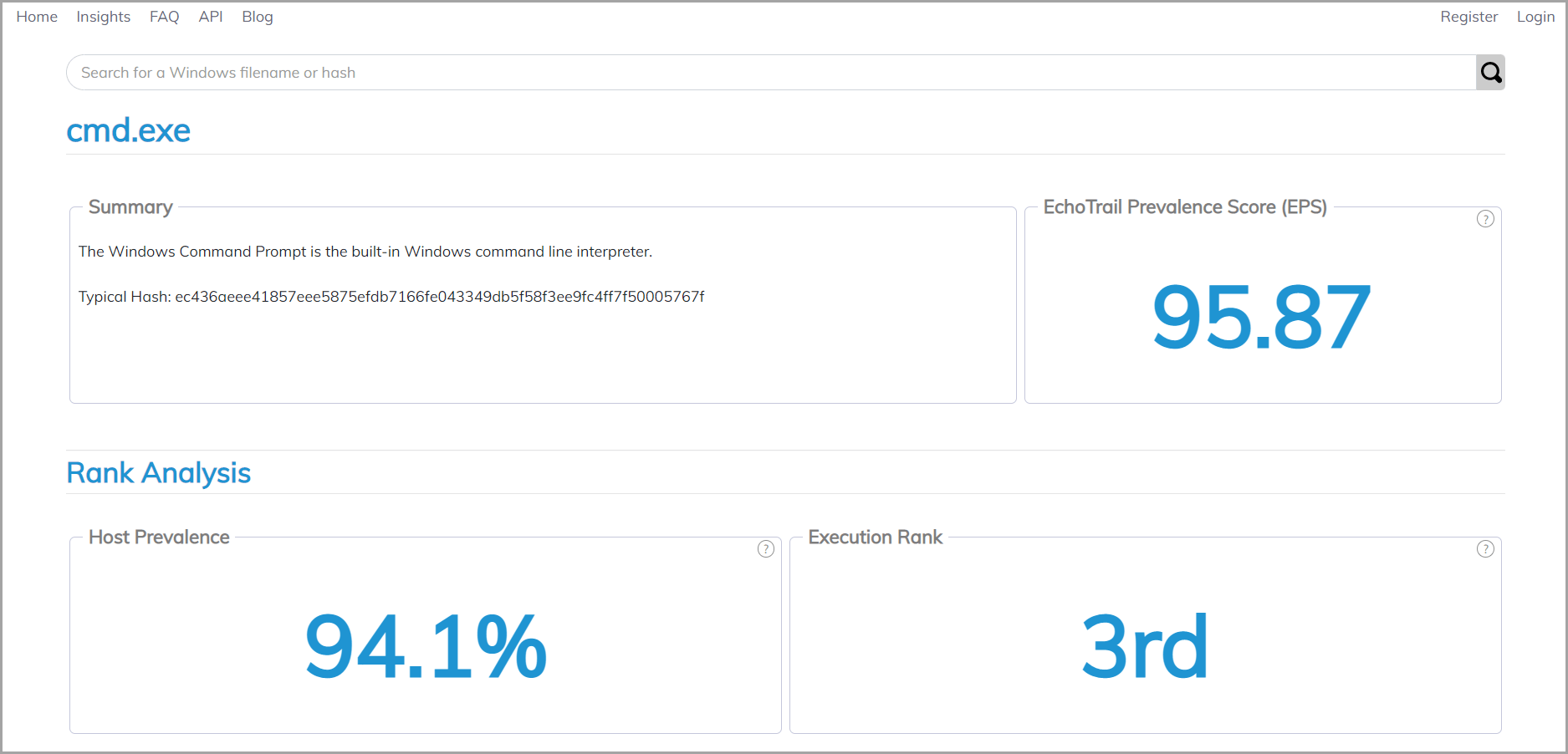
EchoTrail.io database provides the description of the executable binaries, their typical hashes, as well as an insightful behavioral analysis illustrating top hashes, paths, and network ports. In addition, cybersecurity professionals can also delve into the ancestry analysis and explore typical parents and children paths of the selected binary, as well as check out the security analysis for more thorough investigation. Leveraging information from the EchoTrail.io database, cybersecurity practitioners can track suspicious behaviors in their system based on the data insights provided for each binary.
Drill Down to Binary Details Directly From SOC Prime’s Cyber Threats Search Engine
Powered by the EchoTrail.io integration, SOC Prime’s cyber threats search engine delivers a list of relevant Windows filenames or hashes associated with the Sigma rule matching particular search criteria. Cybersecurity practitioners can now instantly reach relevant contextual information for the selected binary, like powershell.exe or cmd.exe, by clicking the corresponding item.
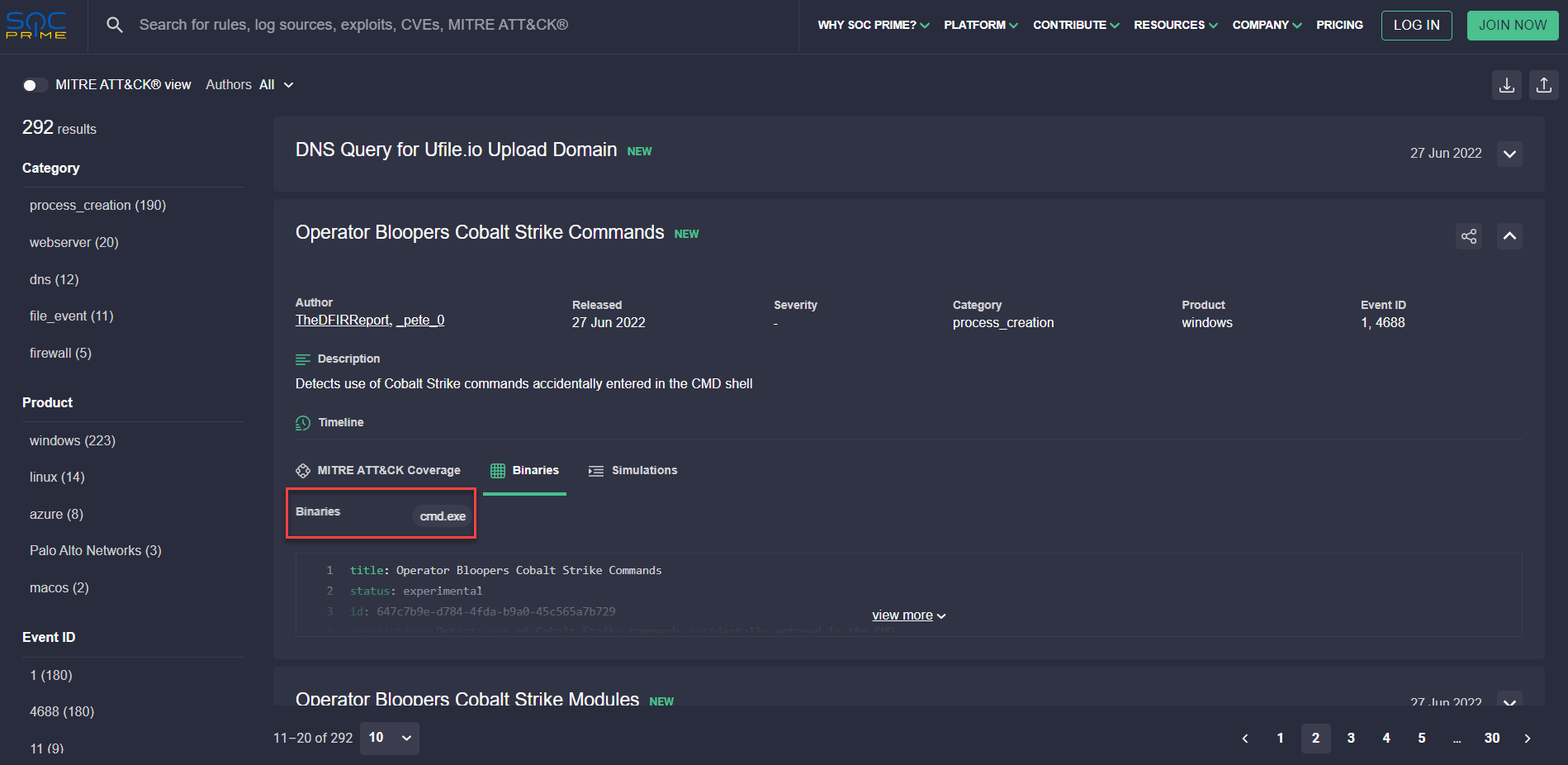
Once clicked, the corresponding pop-up retrieves a summary of binary details where this information is available powered by the EchoTrail.io API, including a brief binary description, top paths and network ports, as as well as top parents and children paths of a relevant filename or hash.
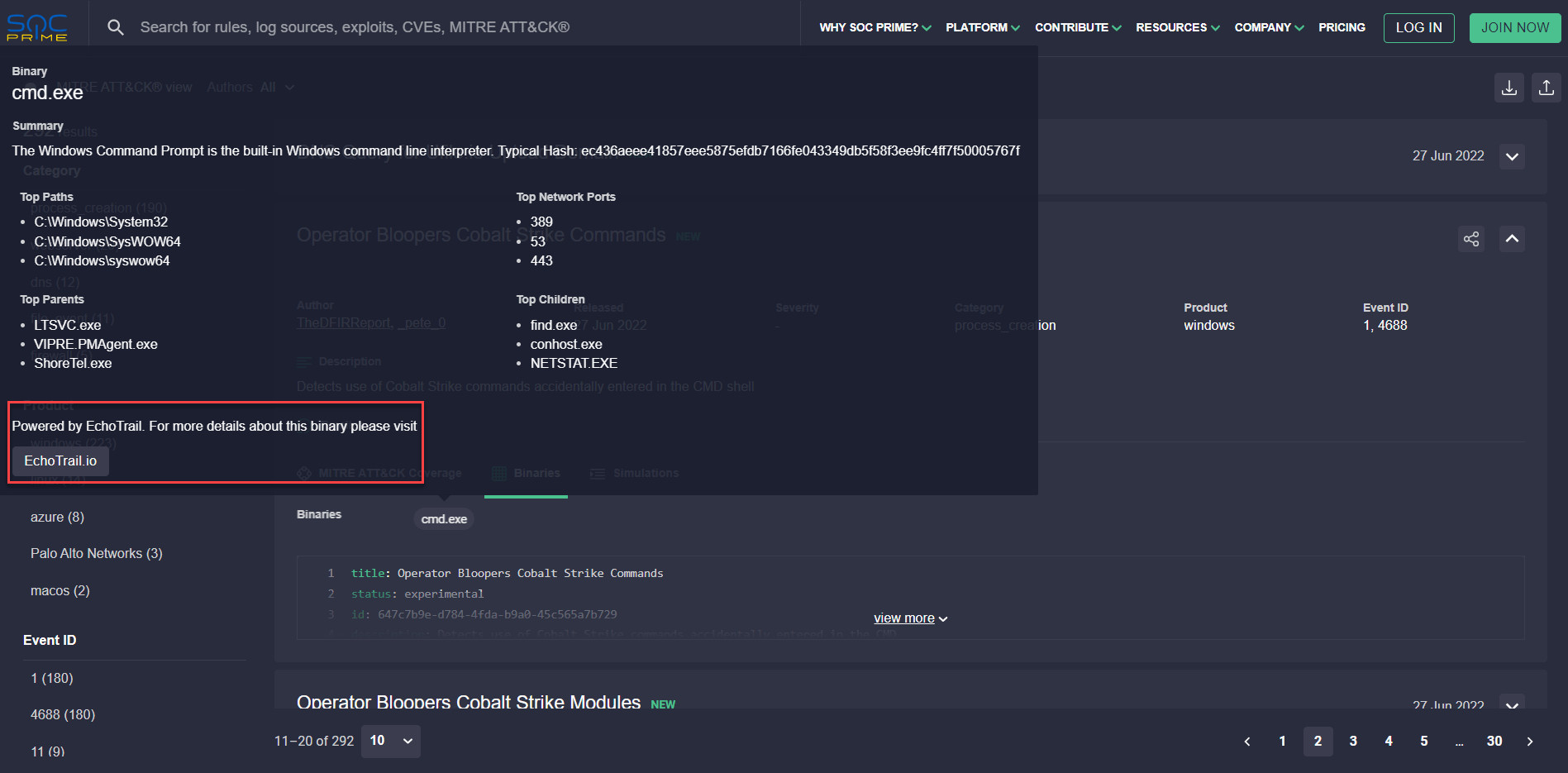
To dive into comprehensive binary analytics, teams can instantly drill down to the EchoTrail.io database by clicking the corresponding button on the pop-up.
Browse the industry-first search engine for Threat Hunting, Threat Detection, and Cyber Threat Intelligence to streamline threat investigation by instantly exploring the latest trends in the cyber threat landscape and reaching comprehensive metadata on curated Detection-as-Code content from SOC Prime’s platform compatible with 25+ SIEM, EDR, and XDR solutions.