To enhance global collaborative cyber defense by enabling Detection as Code practices, SOC Prime continuously broadens the support for open-source cybersecurity solutions. We are thrilled to announce a new integration with OpenCTI, an open-source modular Cyber Threat Intelligence platform that aggregates and visualizes information on cyber threats. Through contribution to this CTI platform, SOC Prime enriches the collective expertise with comprehensive contextual information aggregated from multiple sources. Cybersecurity professionals from across the globe can seamlessly share indicators of compromise (IoCs) and deep dive into the most relevant cyber threat context.
How It Works
To enable integration, we developed the OpenCTI SOC Prime Connector, which pushes Sigma rules from the specific content list right into the OpenCTI database powered by SOC Prime’s Continuous Content Management (CCM) API capabilities*. The connector collects data using the following parameters:
- api_key — the corresponding API key
- content_list_name — the name of the specific content list, from which Sigma rules will be retrieved to the OpenCTI platform
- interval_sec — the specific input interval in seconds
- siem-type (optional) — the particular SIEM, EDR, or XDR platform format, for which external links will be generated
*Please note that to take advantage of the OpenCTI integration, SOC Prime users should have the CCM API access enabled.
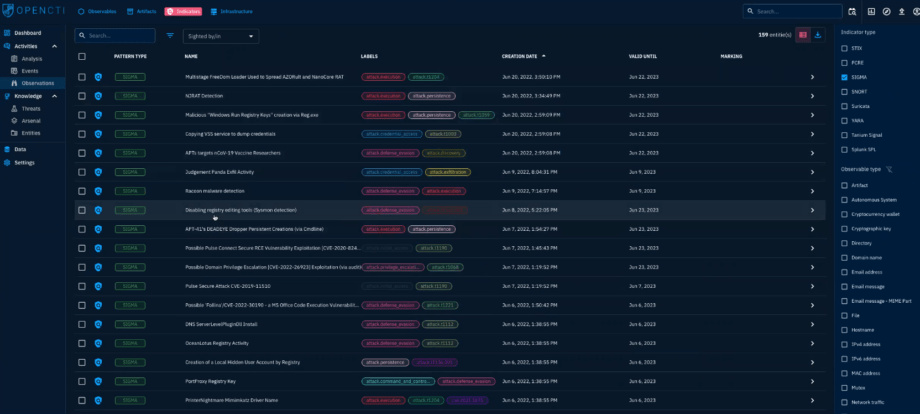
Explore IoCs Retrieved from Sigma Rules From the OpenCTI UI
After pushing Sigma rules from the selected content list via CCM API, cybersecurity experts can explore the collection of relevant IoCs from the OpenCTI platform by clicking Observations > Indicators tab.
To drill down into the rule details, click the corresponding Sigma detection from the list of items. Cybersecurity practitioners can check out the following contextual information automatically retrieved from SOC Prime:
- The Sigma ID
- Content author
- List of relevant tags, including APTs, malware samples, or CVEs for simplified rule search
- Date of rule creation
- Relationships based on ATT&CK techniques, threat actors, and tools
- External references, including CTI links and MITRE ATT&CK links, CVE descriptions, and more relevant metadata
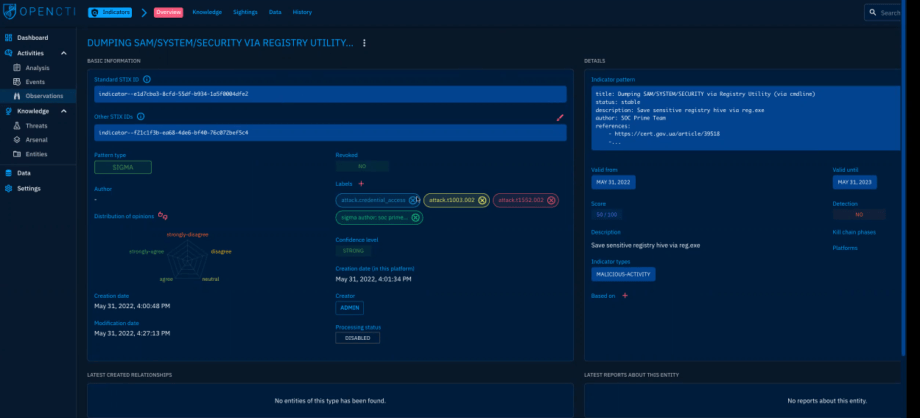
Cybersecurity practitioners can also instantly drill down to the corresponding Sigma rule available in the Detection as Code platform and SOC Prime’s cyber threats search engine. When indicating the specific language format using the siem-type parameter, like ala for Microsoft Sentinel Query, OpenCTI users will be able to instantly drill down to the Sigma rule in the SOC Prime’s platform already converted to the corresponding SIEM-native format. 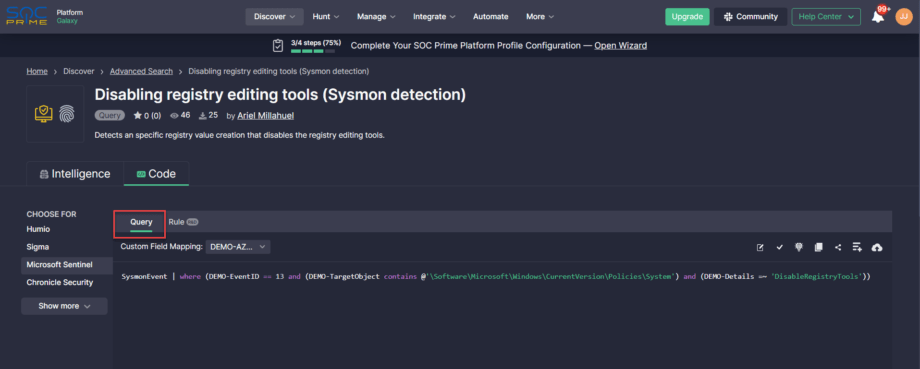
Join SOC Prime’s platform for collaborative cyber defense to keep abreast of emerging threats of any scale and sophistication with curated Detection-as-Code content delivered in under 24 hours after threat discovery. Looking for more ways to streamline threat investigation available within a single tool? Explore the industry-first cyber threats search engine to keep up with the latest trends in the cyber threat arena and instantly reach insightful contextual information accompanied with relevant Sigma rules from SOC Prime’s Detection as Code platform ready-to-use across 25+ SIEM, EDR, and XDR solutions.