Detection intelligence Turbocharged with AI
Enable line-speed detection of cyber attacks by equipping your team with AI, trained on 11 years of Detection Intelligence. Elevate your daily work from SIEM min-maxing to Detection Orchestration across Data Pipelines, AIDR, EDR, Data Lake and SIEM.
Platform modules
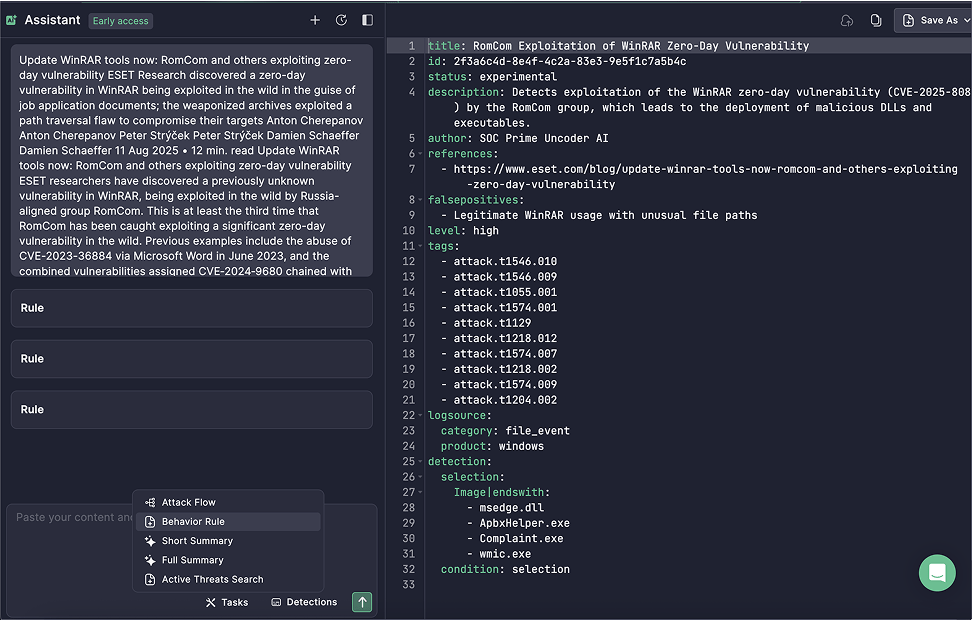
Uncoder Al
“Talk” to your SOC environments and orchestrate pipelines in a natural language
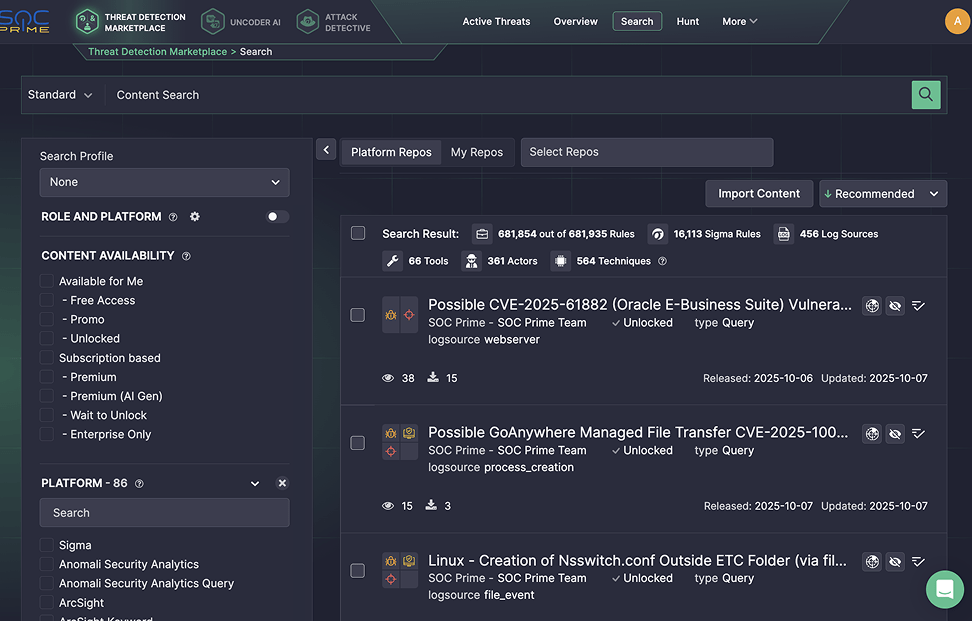
Threat Detection Marketplace
Source detection content from the largest and up-to-date repository
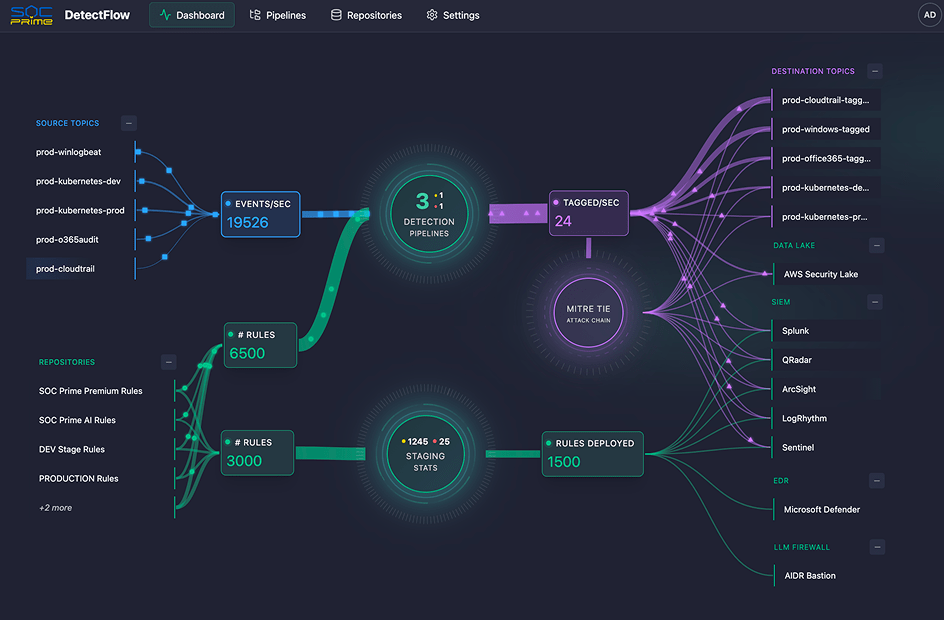
DetectFlow
Run detections on your data pipelines without volume limits
“If you manage a SIEM, you need SOC Prime”
Industry veterans
- Founded the Detection-as-Code industry in 2015
- Partnered with Fortune 100 + global MDRs
Al-ready for detection engineering
- World’s largest dataset of threat detections
- Full workflow: intelligence -> generation -> deployment
One engine for every detection, everywhere
- Run 12k+ detections per pipeline before SIEM ingestion
- On-prem / cloud / air-gapped
Countries
155
Organizations
11,000+
Users
60,000+
Trusted by Enterprise SOC Teams