Collaborative Cyber Defense: Fueling the Fight to Combat Threats of Any Scale
As we all now know, on February 24, 2022, the Russian Federation started an offensive invasion of Ukraine by land, air, and sea. The hostilities have now been ongoing for almost a week with Russian tanks rolling into Ukrainian territory and its missiles striking both military and civil targets across the country. The attacks have led to numerous casualties and the destruction of infrastructure and historical treasure.
Multiple cyber-attacks have also been launched by Russian adversaries designed to cripple Ukrainian IT infrastructure. State-sponsored attacks are also expected against the extensive list of global supporters of Ukraine since many nations, global organizations, and individuals stand united with Ukraine as it combats unprovoked Russian aggression.
Russian Cyber War Chronology
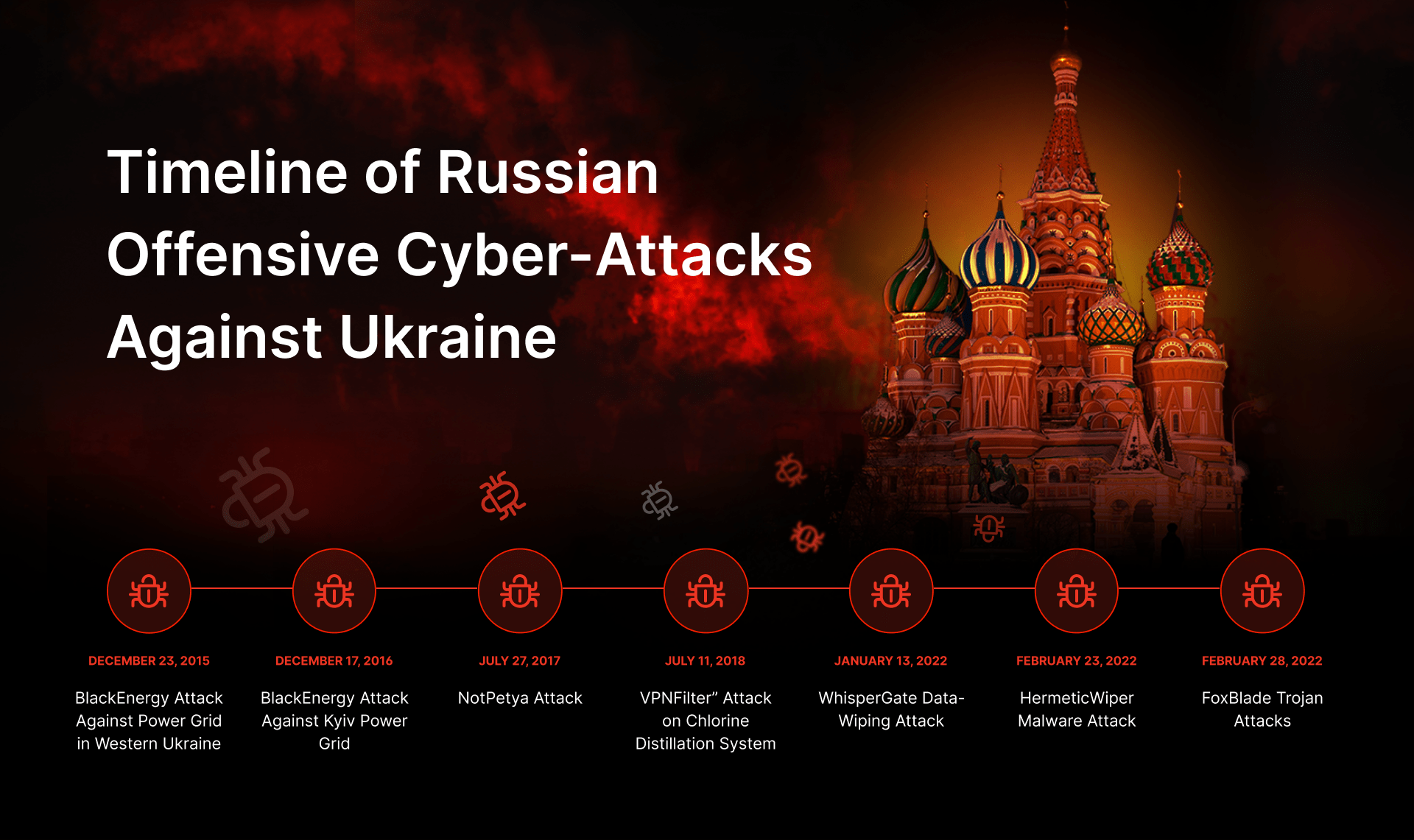
While the ground offensive by Russian troops and missiles has been unexpected, the cyber war against Ukraine has been going on for almost a decade.
Escalating Offensive Cyber-Attacks Against Ukrainian Infrastructure
In 2015-2016, the Ukrainian cyber grid was repeatedly attacked by the Russia-affiliated Sandworm APT group using the infamous BlackEnergy malware. The attacks resulted in massive blackouts throughout the country, illustrating the first case of a cyber threat causing significant damages to critical infrastructure resources and physical plant operational assets.
In 2017, the notorious NotPetya malware was used again by the Sandworm APT group targeting the Ukrainian financial sector. This attack eventually ended up creating a global cyber crisis with millions of systems infected and billions of dollars in damage.
In 2018, Russia tested another destructive sample against Ukrainian critical infrastructure. In particular, VPNFilter malware was used to attack the Auly Chlorine Distillation Station that supplied liquid chlorine to water and wastewater treatment facilities in Ukraine, Moldova, and Belarus. Again, the aim was to disrupt critical infrastructure assets, but the attack methodology can be also used to target many other global systems and operations.
The escalation of political tensions between Ukraine and Russia peaked in 2021-2022 as the offensive cyber operations against Ukrainian infrastructure gained momentum. In the months and weeks preceding the February full-scale invasion, many Ukrainian websites were defaced and pushed offline while multiple government infrastructure assets were compromised by data-wiping malware. These Russian-backed cyber-attacks were aimed at Ukraine to undermine the stability of its systems and created havoc among the civilian population.
WhisperGate Data-Wiping Attack
The full-fledged February invasion of Ukraine was first launched on the cyber front. Russian aggression actually began on January 13, 2022 when a destructive cyber-attack hit Ukraine, taking down the online infrastructure of the country’s government. By January 17, 2021, up to 70 websites experienced temporary performance issues due to the intrusion, including the Cabinet, seven ministries, the Treasury, the National Emergency Service, and the state services. Moreover, multiple non-profit organizations and major Ukrainian IT firms also fell victim to the attack.
The expert analysis by Microsoft revealed that an unnamed APT group used the novel WhisperGate wiper malware to cause extensive damage to the cyber infrastructure. Although initially, attribution was unclear, the investigation by US CISA and the UK NCSC, confirmed that WhisperGate was most likely to have been developed and deployed by Russian government-backed hacking collectives. The investigation by SOC Prime experts supports the suggested attribution and further has identified that many TTPs overlap between WhisperGate maintainers and the Russian nation-backed group Sandworm (KillDisk). Moreover, SOC Prime researchers observed WhisperGate patterns that resembled the malicious behavior of the infamous NotPetya malware first used to destroy Ukrainian infrastructure in 2017.
HermeticWiper Attack
On February 23, a day before the beginning of a full-fledged European war, Microsoft’s Threat Intelligence Center (MSTIC) detected a Russia-linked cyber-attack on Ukraine’s digital infrastructure. A HermeticWiper malware attack heavily hit key Ukrainian organizations. Current data indicates that financial institutions and government contractors in Latvia and Lithuania were also affected. The malware, dubbed HermeticWiper, was built to permanently erase or distort data stored on targeted machines and networks and render an infected device unbootable. Research data proves that the samples were compiled back in December 2021, signaling that this attack was strategic and long-planned.
FoxBlade Trojan Attacks
A Microsoft Security Intelligence advisory identified a novel FoxBlade trojan that swept through Ukraine on February 28, 2022. The Russian-backed attack targeted Ukrainian civilians as well as organizations and firms in banking, agriculture, energy, emergency response services, and humanitarian operations. The malware stealthily utilized breached systems to launch distributed denial-of-service (DDoS) attacks and also download and run other malicious applications. FoxBlade cyber assaults aim at compromising critical assets and data. Unlike the notorious NotPetya attacks, this malware package was used to take down vital infrastructure segments.
Timeline of Russian Offensive Cyber-Attacks Against Ukrainian Infrastructure
Security experts have started to theorize that Ukraine is a giant testing lab for Russian nation-state hackers to experiment with destructive malware samples and malicious techniques, which might be leveraged to launch further attacks against other nations. Given the indications of rapid spread of Russian aggression, the prospect of cyber war targeting critical infrastructure of other countries may be a matter of not “if” but “when”.
Global Response to Critical Threats
It is also worth mentioning the response from other well-known hacker collectives such as Anonymous and NB65. These organizations have claimed to strike hard in cyberspace to stop the war against Ukraine. Their actions thus far:
- Disabled the Control Center of the Russian Space Agency “Roscosmos”
- Knocked offline more than 1,500 Russian and Belarusian governmental websites, state media outlets, banks, and companies
- Leaked data of Russia-linked Conti ransomware gang
- Breached the database of the Russian Ministry of Defense
- Hacked the websites of Russian propaganda news media TASS, Izvestia, Fontanka, RBC, and Kommersant
The invasion of Ukraine has sparked an immediate and impressive response from the global cyber community. Ukraine’s Deputy Prime Minister and Minister of Digital Transformation, Mykhailo Fedorov, launched a volunteer cyber collective that includes 175,000+ subscribers and forms what can be considered as a critical part of the IT Army of Ukraine. Contributors have engaged in denial-of-service cyber-attacks targeting the websites of Russian government, banks, and energy companies. Starting from February 27, the IT Army also targeted websites registered in Belarus that supported Russia in the cyber war.
Anti-war cyber engagement combating Russian aggression is increasing every day. It seems that everyone now with a device turns it into a DDoS weapon.
While Ukrainian troops resist at the front of the Russian invasion, they need all the support they can get right now. More individuals can unite to help. Below are the links to official charity organizations that help Ukrainian Armed Forces, civilians living in war zones, and injured people.
- NBU special account to raise funds for Ukraine’s Armed Forces
- Come Back Alive NGO Organization
- List of 30+ charities to support Ukraine
Current and accurate information on the war in Ukraine is available from the trusted sources below:
- English: https://t.me/ukrainenowenglish
- German: https://t.me/UkraineNowGerman
- French: https://t.me/UkraineNowFrench
- Italian: https://t.me/UkraineNowItalian
- Spanish: https://t.me/UkraineNowSpanish
- Polish: https://t.me/UkraineNowPoland
- Czech: https://t.me/ukrainenowczech
- Turkish: https://t.me/UkraineNowTurkish
The Power of Collaborative Cyber Defense
In these turbulent times, the power of crowdsourcing and global collaboration offers competitive advantage over attackers. No individual company is capable of marshaling an equal resource pool of talent capable of withstanding cyber-attacks of such scale. Together, backed by our crowdsourcing initiatives and the open source Sigma standard, organizations can accelerate cyber defense by delivering detection content to identify new and innovative attacks like those deployed by Russia. Only together can we hope to succeed in combating evil on all fronts.
SOC Prime unlocks access to the full list of free Sigma-based detections to defend your infrastructure against Russian-backed digital attacks. To reach the dedicated detection content, sign up or log in to the SOC Prime Platform and instantly search for threats in your environment using the Quick Hunt module:
Free threat hunting queries to proactively defend against Russian-backed cyber-attacks
Join the SOC Prime Platform to become part of the world’s largest community of cyber defenders and help us transform threat detection worldwide. Cybersecurity researchers and content contributors across the globe are highly welcome to contribute to collaborative cyber defense by creating detection content to join the fight in combating current and evolving threats.