Potentially Unwanted Applications (PUAs) like NimScan.exe can silently operate within enterprise environments, probing internal systems or facilitating lateral movement. Detecting these tools early is critical to prevent network-wide compromise.
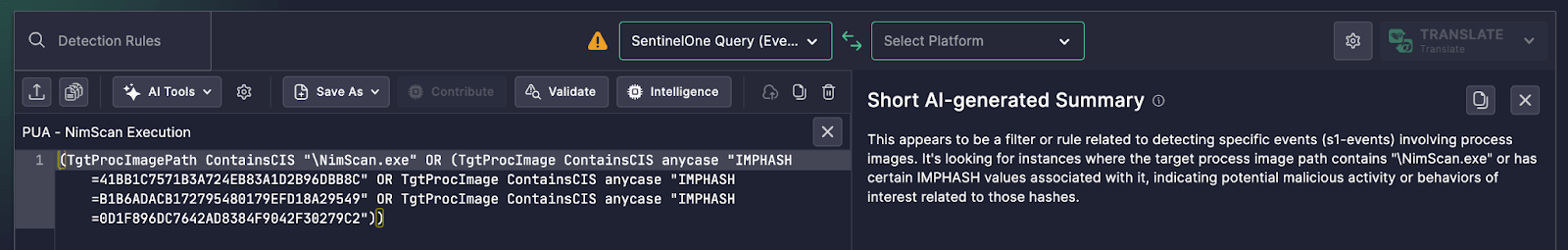
A SentinelOne detection rule recently analyzed in SOC Prime’s Uncoder AI platform highlights this threat by identifying events where the target process path or IMPhash signature indicates the presence of NimScan.
Detection Logic Overview
This SentinelOne query is designed to trigger when:
- The target process image path contains
\NimScan.exe, - OR the process image has one of several known IMPhash values linked to NimScan variants.
These values map to known samples of the PUA and allow for detection even if the executable is renamed or moved.
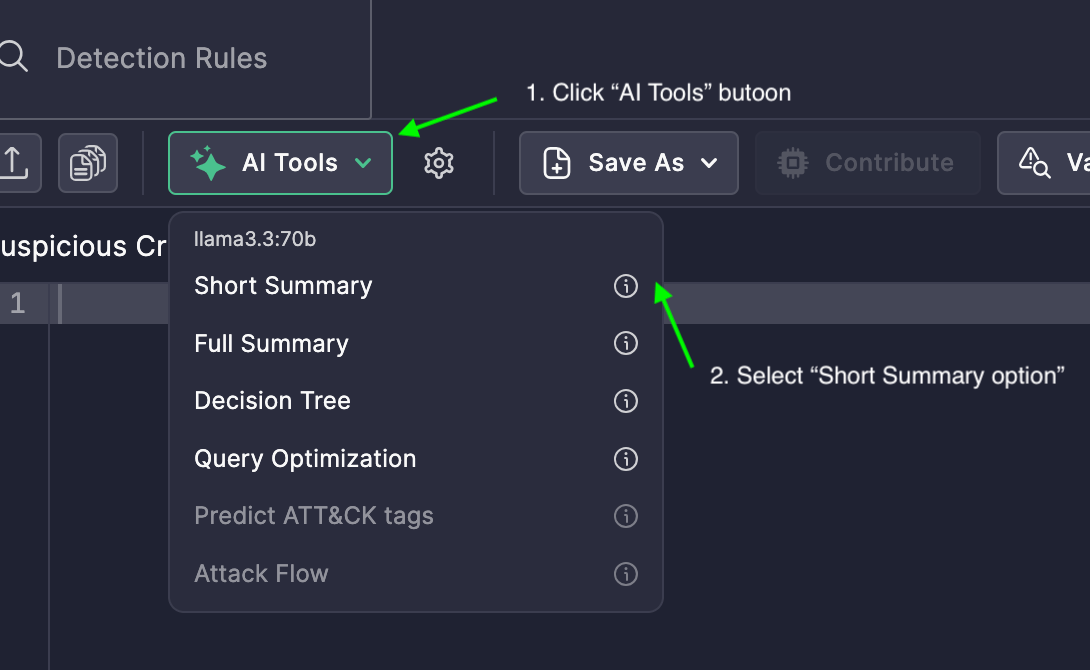
What Uncoder AI’s Summary Delivered
Uncoder AI’s Short AI-generated Summary translated the rule into a human-readable explanation
This AI-generated context helps security teams understand that the rule detects either:
- A direct match on the file name (NimScan.exe), or
- A hash match on known malicious binaries associated with NimScan.
Why This Matters
- Early PUA Detection: Identifying NimScan early helps stop its use in lateral movement or internal scanning.
- Hash-Based Matching: Even obfuscated or renamed versions of the tool are caught through IMPhash detection.
- Faster Rule Understanding: Analysts no longer need to manually interpret matching conditions—Uncoder AI delivers immediate clarity.
From SentinelOne Syntax to Actionable Insight
Without Uncoder AI, understanding SentinelOne’s rule structure—especially those involving compound hash conditions—requires deep product familiarity. With the Short Summary feature, the detection logic becomes instantly actionable, enabling teams to triage alerts faster and with higher confidence.