On April 26, 2022, cybersecurity researchers reported about an ongoing phishing cyber-attack on Ukraine spreading GraphSteel and GrimPlant malware strains according to the latest CERT-UA warning. The malicious activity is attributed to the behavior patterns of the hacking collective tracked as UAC-0056, a nefarious cyber espionage group also dubbed SaintBear, UNC258, or TA471. The targeted attack involves sending a phishing email with a lure attachment related to COVID-19 and containing a malicious macro, which triggers an infection chain.
Phishing Cyber-Attack Using GraphSteel and GrimPlant Malware: Overview and Analysis
Cyber-attacks of the infamous UAC-0056 hacking group targeting Ukrainian state bodies and organizations were also detected a couple of months ago. The activity of this cyber espionage group is also linked to the destructive WhisperGate attack that at the turn of 2022 took down the online assets of the Ukrainian government. After the beginning of Russia’s invasion of Ukraine and the spread of full-scale cyber-war, the UAC-0056 group was observed targeting Ukrainian state bodies in a spear-phishing campaign distributing GraphSteel and GrimPlant malicious strains also leveraged in this latest April’s cyber-attack.
Particularly, in March 2022, CERT-UA alerted about several malicious operations aimed at attacking Ukrainian state bodies. The first phishing attack masqueraded as a notification from Ukrainian officials that urged victims to introduce a system update via a link included in a fraudulent email. If opened, two files were dropped to the targeted machine: the Cobalt Strike Beacon and a dropper to download and execute GraphSteel and GrimPlant backdoors. Also, Discord was used as a hosting server for the additional malware to download.
In a couple of days, security researchers from SentinelOne revealed another two GraphSteel and GrimPlant samples. Both were written in Go and dropped by an executable hidden within a translation app. Then, at the end of March, CERT-UA reported another phishing attack disseminating malicious XLS files. The nefarious emails came with a malicious file attachment. After opening the file and enabling a macro, a file called Base-Update.exe was created to download GraphSteel and GrimPlant samples.
Finally, on April 26, 2022, CERT-UA identified the latest case of GraphSteel and GrimPlant attack against Ukrainian officials. This time, adversaries crafted phishing emails with the COVID-19 lure to trick victims into downloading a macro-laced XLS file. If opened, a macro decoded a payload located within a hidden XLS sheet and launched a Go-downloader. Further, GraphSteel and GrimPlant malware samples were uploaded and executed on the targeted machine. Notably, the phishing emails were delivered from a compromised account owned by an employee of the Ukrainian government institution.
GraphSteel and GrimPlant (aka Elephant)
According to the inquiry by Intezer, the Elephant malware framework typically consists of four main components. The first one is a Dropper that doesn’t have an embedded payload but triggers the next stage of attack involving the Downloader. This Downloader is written in Go and used to maintain persistence as well as to deploy the backdoor payloads.
The GrimPlant payload (Elephant Implant) is used to steal the system information and communicate it to the command-and-control (C&C) server in order to proceed with the attack. Then, the last payload of GrimPlant (Elephant Client) is triggered to act as a data stealer and collect sensitive data from the compromised system. Additionally, GrimPlant attempts to dump credentials manager data as well as browser, email, Filezilla, and other creds alongside the Wi-Fi information and Putty connections.
Sigma Behavior-Based Content to Detect GraphSteel and GrimPlant Malware Spread by UAC-0056
To proactively defend against spear-phishing attacks of the UAC-0056 hacking collective spreading GraphSteel and GrimPlant malware, security practitioners can leverage the following detection stack provided by the SOC Prime Team:
Sigma rules to detect GraphSteel and GrimPlant malware spread by UAC-0056 group
All the above-referenced detections are available for registered users of the SOC Prime’s Detection as Code platform and can be found using the custom tag #UAC-0056 associated with the relevant hacking collective.
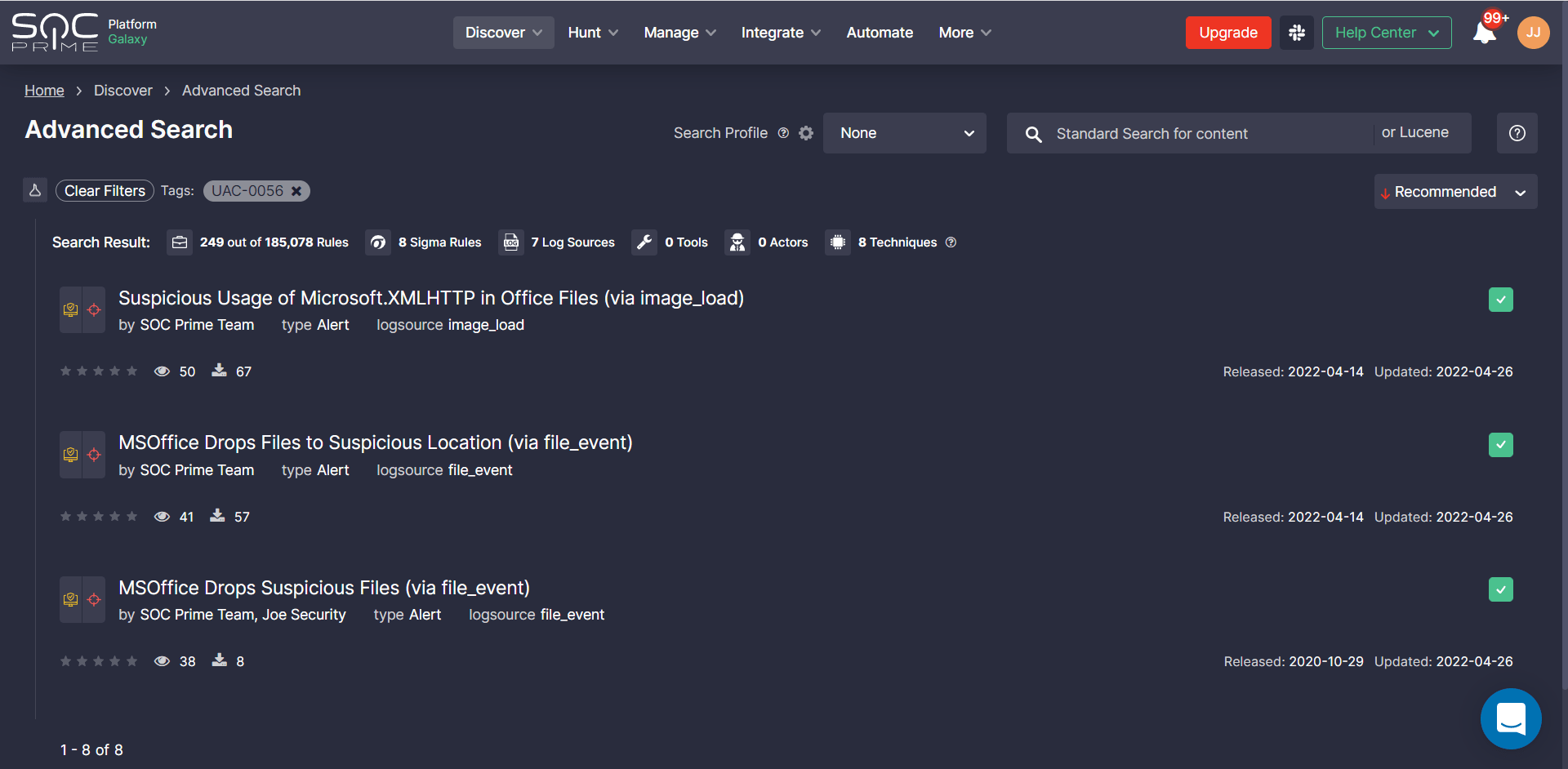
Teams can also apply this Sigma-based detection stack to instantly hunt for threats related to the UAC-0056 threat actors leveraging SOC Prime’s Quick Hunt module.
MITRE ATT&CK® Context
To dive into the context of the latest phishing attack of the UAC-0056 group distributing GrimPlant and GraphSteel backdoors, all above-mentioned Sigma-based detection content is aligned with the MITRE ATT&CK framework addressing relevant tactics and techniques:




