On June 24, 2022, CERT-UA warned about a new malicious campaign targeting telecommunication providers in Ukraine. According to the investigation, russia-linked adversaries launched a massive phishing campaign delivering DarkCrystal remote access Trojan (RAT), able to perform reconnaissance, data theft, and code execution on the affected instances. The malicious activity is tracked as UAC-0113, which with a medium level of confidence is attributed to the russian hacking collective Sandworm earlier observed in multiple cyber-attacks aimed at Ukrainian entities.
Detect DarkCrystal RAT Leveraged in the Latest Campaign by SandWorm Group aka UAC-0113
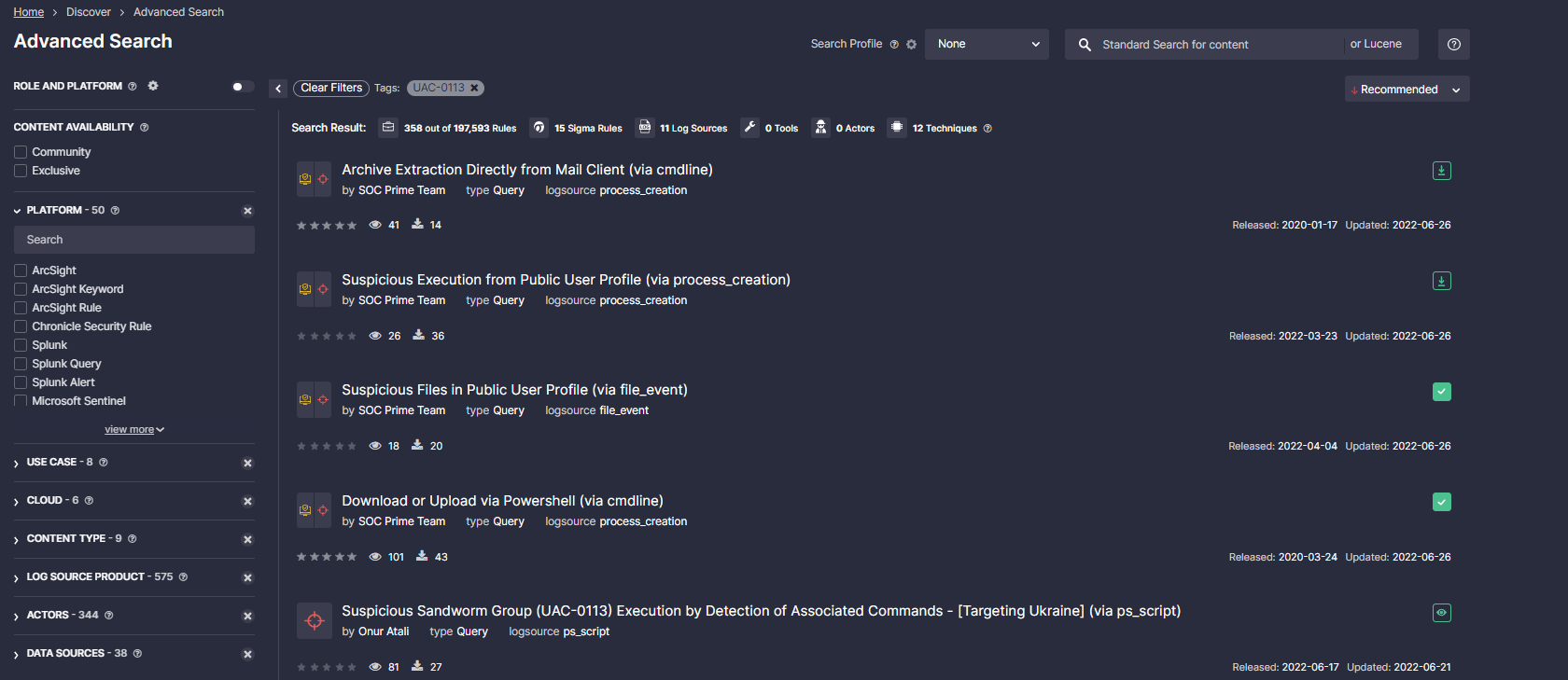
To boost threat detection capabilities and timely identify the malicious activity of Sandworm APT, including DarkCrystal RAT infections, explore a batch of curated Sigma rules developed by SOC Prime Team and Threat Bounty Program content contributors:
Sigma rules to detect the malicious activity of the Sandworm APT group (UAC-0113)
All Sigma rules above are aligned with the MITRE ATT&CK® framework for the enhanced threat visibility and are compatible with the 25+ SIEM, EDR, and XDR solutions. To streamline your content search, cybersecurity professionals can browse the Threat Detection Marketplace content library by #UAC-0113 tag associated with the malicious activity described above.
Additionally, cybersecurity practitioners can leverage a set of associated IOCs provided by CERT-UA to detect DarkCrystal RAT infections. Using SOC Prime’s Uncoder CTI tool, threat hunters and detection engineers can generate custom IOC queries on the fly, having them ready to run in the chosen SIEM or XDR environment.
Registered users of the SOC Prime platform can instantly reach the full list of detection content associated with Sandworm APT by hitting the Detect & Hunt button. Eager to learn about the latest trends in the cyber threat arena and corresponding detection rules to address the emerging challenges? Reach SOC Prime’s Cyber Threat Search Engine to search for a specific exploit, CVE, or malware accompanied by relevant Sigma rules and comprehensive metadata.
Detect & Hunt Explore Threat Context
DarkCrystal RAT Analysis: The Latest Attack Against Ukrainian Telecom Organizations by Sandworm (UAC-0113)
DarkCrystal RAT, aka DCRat, first sprang into action in 2018. The RAT is a commercial backdoor, primarily distributed via Russian hacker forums. Today it has earned a reputation as one of the most affordable RATs, with its advertised price never exceeding $9.
In the recent attacks targeting telecommunication operators in Ukraine, adversaries distributed emails, luring targets with war-related bogus legal aid promises, CERT-UA reports. The malspam campaign featured the distribution of the malicious RAR file that can be used to sneak DarkCrystal RAT onto compromised devices.
The assumption regarding the telecom organizations of Ukraine being the primary target of this malspam campaign is based on the data extracted from victim profiles and the DarkCrystal RAT’s control domain. Worth mentioning that one of the latest attacks on the cyber front at the beginning of June was launched on Ukrainian media organizations and was attributed to the Sandworm APT group.
MITRE ATT&CK® Context
To improve threat visibility and perform a thorough analysis of the threat actor behavior patterns, all Sigma rules to spot the malicious activity of the UAC-0113 hacking collective are aligned with MITRE ATT&CK, addressing the corresponding tactics and techniques:
Tactics | Techniques | Sigma Rule |
Initial Access | Phishing (T1566) | |
Exploit Public-Facing Application (T1190) | ||
Defense Evasion | Signed Binary Proxy Execution (T1218) | |
Hide Artifacts (T1564) | ||
Template Injection (T1221) | ||
Masquerading (T1036) | ||
Execution | Command and Scripting Interpreter (T1059) | |
Command and Control | Ingress Tool Transfer (T1105) | |
Persistence | Create or Modify System Process (T1543) |