At SOC Prime, we are continuously broadening the support for cloud-native solutions to be in line with the current shift of security operations (SecOps) teams towards integrated and cross-tool environments. And now, we are delighted to announce our partnership with Securonix to deliver curated content for this cloud-native next-gen SIEM.
The Securonix software-as-a-service (SaaS) platform provides users with an entity analytics-driven SIEM, SOAR, and NTA to ensure a cutting-edge threat hunting experience for security practitioners. By enriching rules with translations to a new Securonix format, Threat Detection Marketplace makes an important step forward to match each organization’s XDR stack.
Deploying Securonix Queries to Your Instance
As of June 2021, Threat Detection Marketplace aggregates almost 2,000 Securonix Queries mapped to the MITRE ATT&CK® framework v.9 and ready for seamless deployment to users’ instances. Security practitioners leveraging Securonix SIEM can reach qualified and curated SOC content developed by SOC Prime’s community of cybersecurity experts to strengthen the cyber defense against emerging threats.
Searching for Queries
To find detections matching your request, you can easily filter all SOC content available in Threat Detection Marketplace by the Securonix platform on the Content page.
Deploying Queries
Once filtered, you can choose a relevant rule from the filtered list and see at once the Securonix Query tab selected with the source code converted to this language format. Security performers can copy the query source code to their Securonix instance to shave seconds off content deployment. Also, Threat Detection Marketplace users can easily edit the rule to fit all requirements right from the content item page by clicking the Edit button on the action panel.
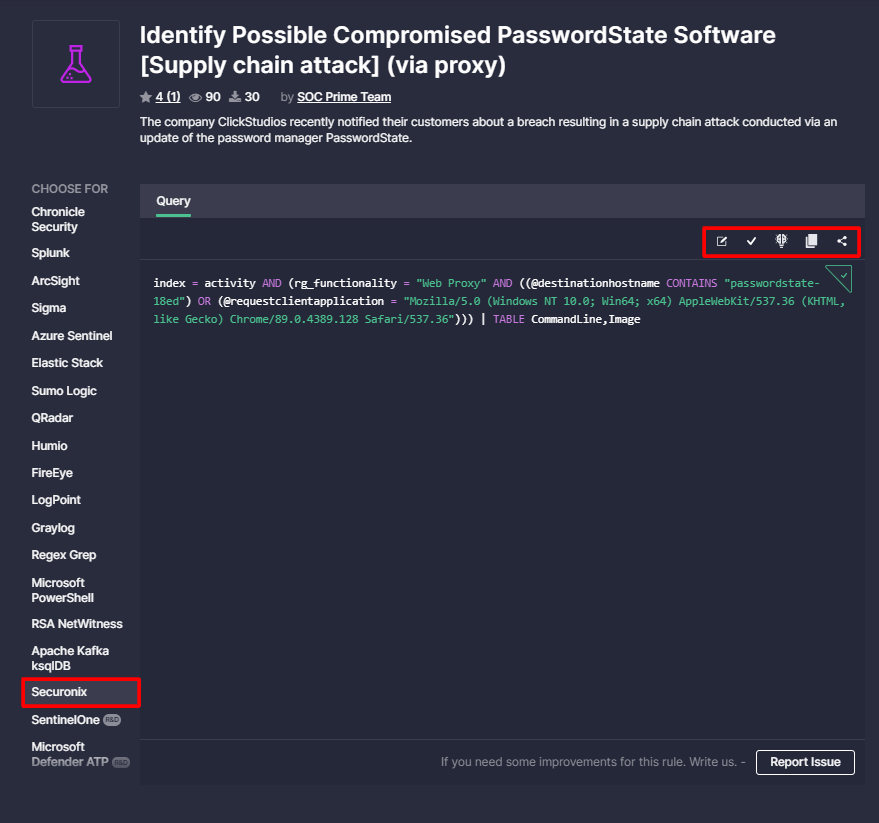
Additionally, you can apply Custom Field Mapping to customize Securonix translations and enable seamless on-the-fly conversion scalable to the appropriate language format without parsing errors.
Securonix Queries Overview
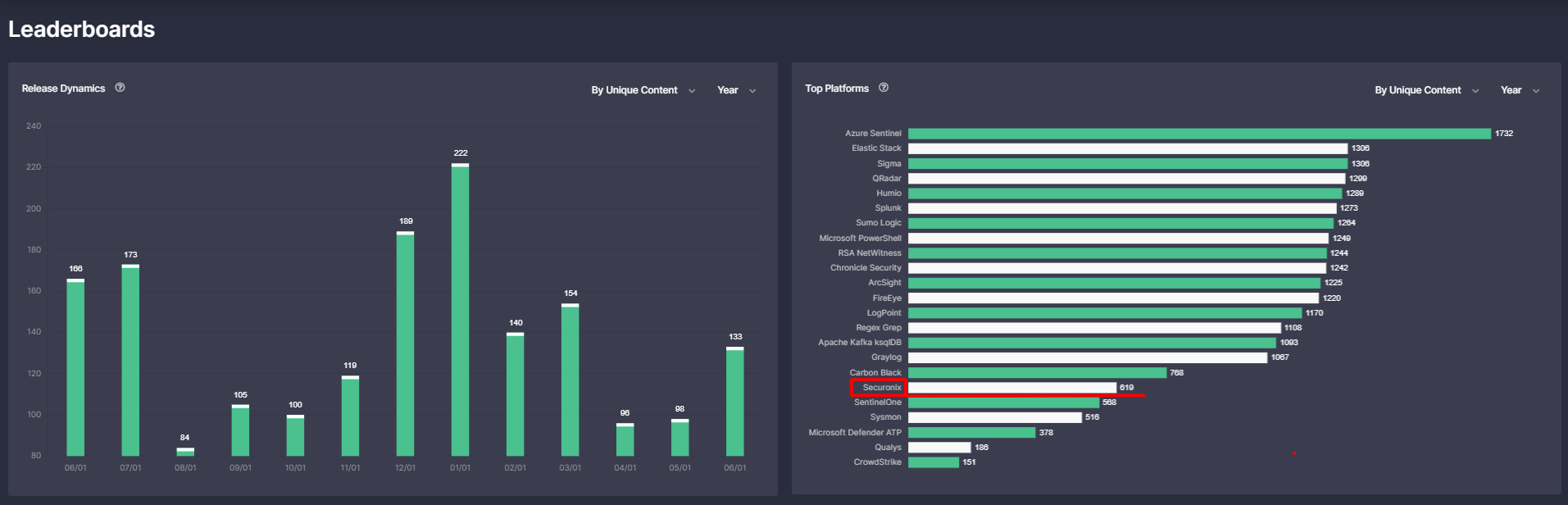
To track the stats on available Secunonix Queries over the selected time period, go to Leaderboards page and check the Top Platforms bar chart.
On-the-Fly Translations to Securonix
Helping SecOps team members to break the limits of a single technology, SOC Prime ensures seamless translations from the generic Sigma language to other languages formats using the Uncoder.IO. You can use our online translation tool to easily convert detection rules of interest into Securonix Query format.
To get the translation, paste a required Sigma rule into the left text box. Further, choose Securonix as an output language from the drop-down menu list of supported platforms on the top right. Finally, you can press the Translate button and copy the relevant Securonix Query from the text box on the right.
To help security practitioners streamline their threat hunting activities, we are continuously broadening Threat Detection Marketplace support for various cybersecurity solutions. Currently, users can reach over 100K qualified, cross-vendor, and cross-tool SOC content items tailored to 20+ market-leading SIEM, EDR, NTDR, and XDR technologies. Enthusiastic to participate in threat hunting activities and enrich our library with new Sigma rules? Join our Threat Bounty Program for a safer future!