September ‘22 Publications
In September, members of the Threat Bounty Community submitted 441 rules for review by the SOC Prime team via the Developer Portal and Sigma rules Slack Bot. However, only 183 rules have successfully passed the verification and were approved for publication on the SOC Prime Platform. When creating new rules and submitting them for review, the content authors should mind the acceptance criteria outlined in the Program Terms, and follow the instructions suggested by the automated Sigma rules check tool.
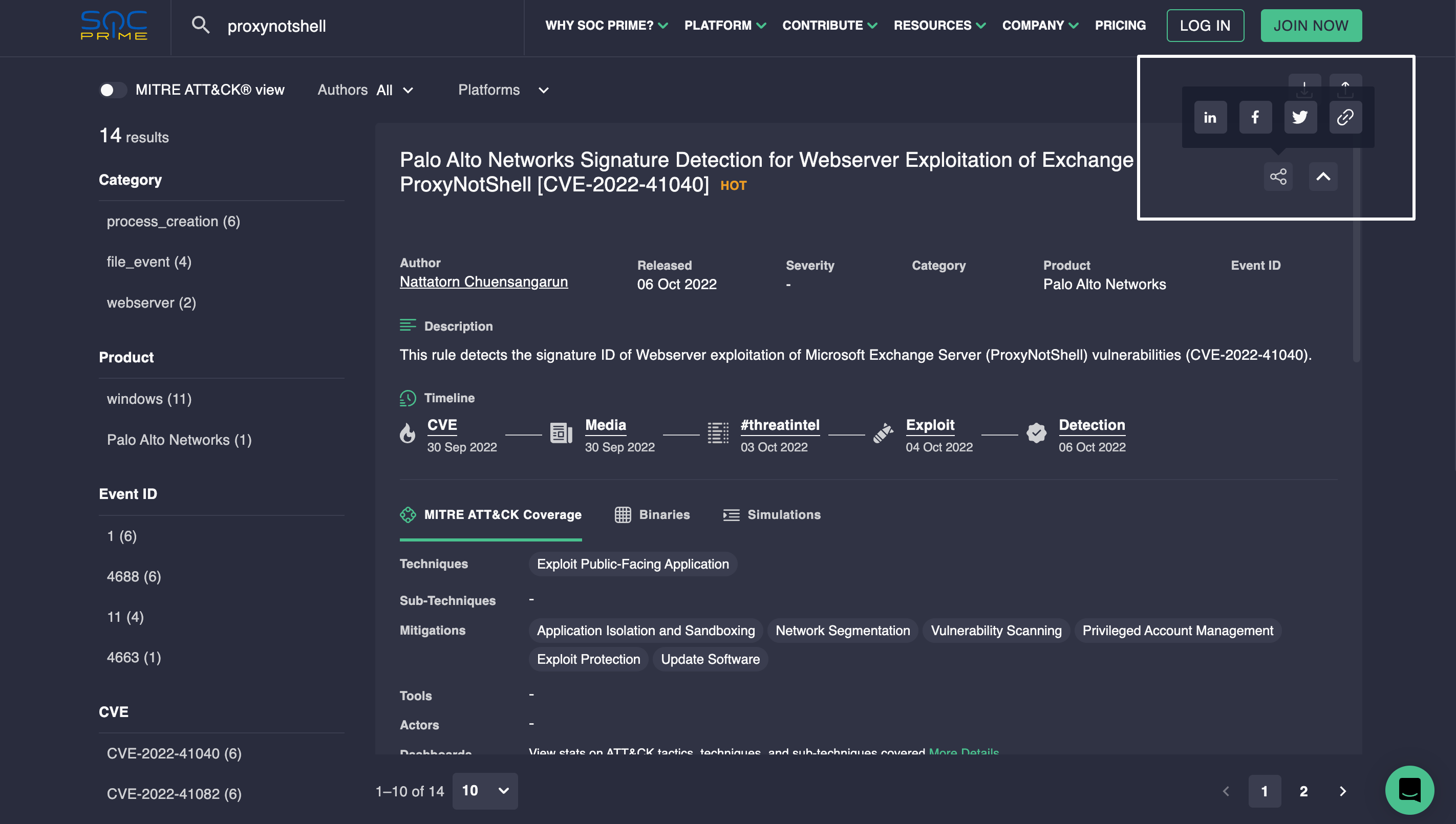
Sigma rules submitted by Threat Bounty authors are also searchable via SOC Prime’s Cyber Threats Search Engine and are regularly included in the publications on SOC Prime Blog.
Threat Bounty content authors can share their achievements with their peers on LinkedIn, Facebook, and Twitter, or send the direct link to their rule directly from the Sigma page:
Top Authors
The author’s rating depends on the interest of SOC Prime Platform users in their detection rules published via Threat Bounty. In September, the following authors were the leaders according to the Threat Bounty rating and received top bounty rewards:
Top-Rated Content
Possible detection of HYPERSCRAPE tool used by Iranian APT treat hunting Sigma rule by Zaw Min Htun (ZETA) detects HYPERSCRAPE which is used to steal user data.
Possible PowerShell Fileless Execution by Query Malicious Commands from Multiple DNS TXT Record and Join Them for Execution (via cmdline) threat hunting Sigma rule by Wirapong Petshagun detects the PowerShell command used to query malicious commands from multiple DNS TXT records and joins them for execution.
Highly Suspicious Scheduled Task Creation Of Lazarus APT Group Activity (MagicRAT detection via process_creation) threat hunting Sigma rules by Emir Erdogan detects scheduled task creation by the MagicRAT.
Possible Deployment of the AIRDRY.V2 Backdoor Through a Trojanized Instance of The PuTTY (UNC4034) by Detection of Associated Commands (via cmdline) threat hunting Sigma rule by Wirapong Petshagun detect execution commands used by UNC4034 that send a fake job offering as malicious ISO package via WhatsApp lead to the deployment of the AIRDRY.V2 backdoor through a trojanized instance of the PuTTY utility.
New BianLian Ransomware[CVE-2021-34473] Behavior by Detection of Associated Processes (via process_creation) threat hunting Sigma rule by Aytek Aytemur detects suspicious processes associated with BianLian Ransomware group.
All the Sigma rules provided via Threat Bounty Program are mapped to the MITRE ATT&CK® framework and have references to the metadata providing a broader context to the detected malicious activity. Moreover, all the detections submitted by Threat Bounty content authors for monetization on the Platform undergo automatic checks and verification by the SOC Prime team.
Don’t hesitate to join the Threat Bounty Program, earn cash on your detection engineering skills, and create a portfolio demonstrating your expertise with SOC Prime!




