Simple integration helps search for malicious processes
Greetings Everyone! Let’s continue to turn Splunk into a multipurpose tool that can quickly detect any threat. My last article described how to create correlation events using Alerts. Now I’ll tell you how to make a simple integration with Virus Total base.
Many of us use Sysmon in the environment to monitor network connections, process creations and any changes in time of file creation. This system driver provides monitoring and logging of system activity to the Event Log. One of the most required Sysmon features is calculation and recording of running processes’ hashes. Thus, we can use this data, Splunk and Virus Total base to detect malicious processes that possibly run in your environment.
So let’s start
- Collect Sysmon logs to Splunk.
To setup collecting Sysmon logs from Windows systems, we need to install Add-on for Microsoft Sysmon on Splunk. You can find the description of this process on https://splunkbase.splunk.com/app/1914/.
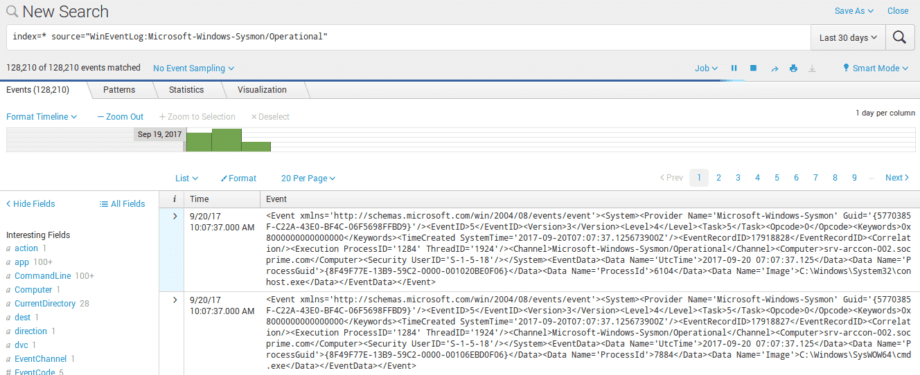
- At this point we have already installed Add-on for Microsoft Sysmon and logs are collecting into our Splunk:
- So now we need to make search and create a table with processes that run on our test server.
Sysmon event with ID 1:
index=* source=”WinEventLog:Microsoft-Windows-Sysmon/Operational” EventCode=1
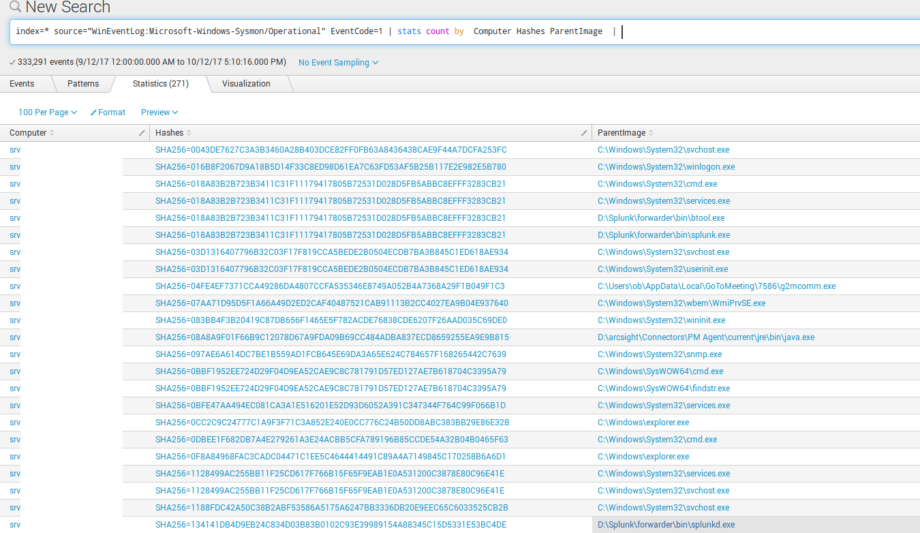
Building of statistics table:
index=* source=”WinEventLog:Microsoft-Windows-Sysmon/Operational” EventCode=1 | stats count by Computer Hashes Image
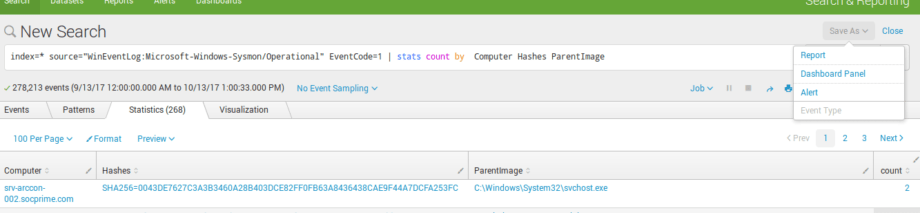
- Then we save this search as dashboard panel:
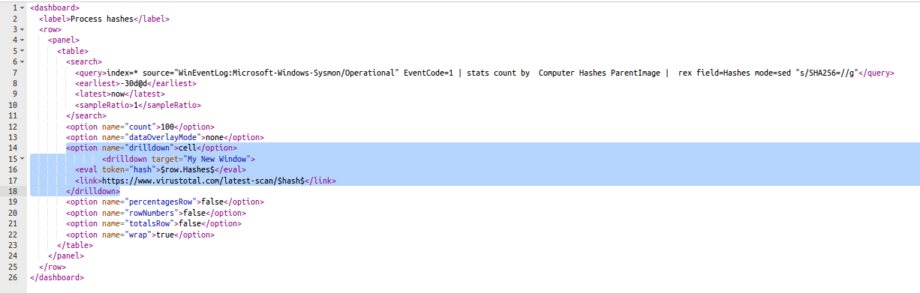
- Now for the saved panel, we need to create a drilldown on the VirusTotal page to check the hash from the table. To do this, we open Edit Source panel, add drilldown option and tag:
<option name=”drilldown”>cell</option>
<drilldown target=”My New Window”>
<eval token=”hash”>$row.Hashes$</eval>
<link>https://www.virustotal.com/latest-scan/$hash$</link>
</drilldown>
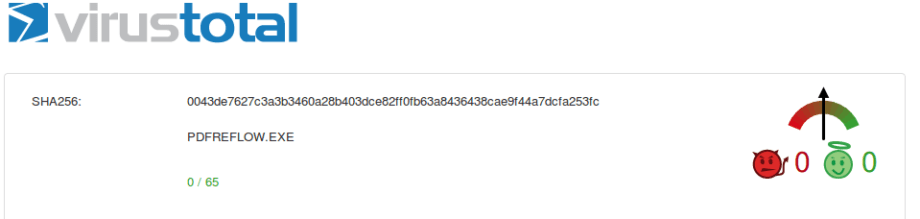
- After saving the dashboard, we will be able to click on the Hashes cell to check the hash on the Virus Total page with this drilldown:
In this article, I showed a simple way to make integration using drilldown. You can leverage this method to integrate a lot of different and convenient checks on external web resources. With a single click, you will get the information you need. You can also use Sysmon Framework by SOC Prime for detection and deeper analysis of malicious activities. My next article will be about leveraging of depends panels, the tool that helps make dashboards more informative.