On October 1, the Cybersecurity and Infrastructure Security Agency published a joint CISA and FBI cybersecurity advisory on the Chinese Ministry of State Security-affiliated threat activity, issued as the Alert AA20-275A.
This alert was sent to resonate with the heightened tensions between the United States and China, which followed accusations of insufficient control measures taken by China due to the coronavirus outbreak, as well as charges with human rights violations, espionage, and intellectual property theft.
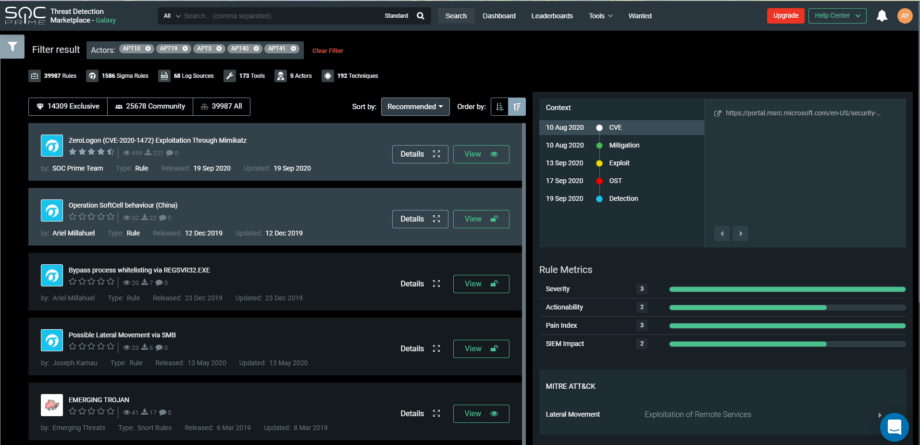
SOC Prime as a pioneer and an industry-leading organization for Detection as a Code, is always keeping a finger on the pulse of the emerging threats to help security practitioners proactively defend against them. As a response to the Alert AA20-275A, we feel our responsibility for providing the critical infrastructures with threat severity information and mitigation instructions using Threat Detection Marketplace capabilities. Here you can find information on the most targeted detection content that addresses commonly implemented tools and frameworks often used by the Chinese threat actors, as well as key vulnerabilities exploited by APT groups.
Threat Actors
A variety of US industries have fallen prey to the targeted cybercrimes attributed to the Chinese state-sponsored APT groups. In their malicious activities, the notorious threat actors mentioned in the Alert AA20-275A hit on critical manufacturing facilities, financial and governmental institutions, defense industrial assets, healthcare organizations, and education establishments.
| Chinese threat actors | Detection content |
| APT3 | Content to detect APT3 attacks |
| APT10 | Content to detect APT10 attacks |
| APT19 | Content to detect APT19 attacks |
| APT40 (also known as Leviathan) | Content to detect APT40 attacks |
| APT41 | Content to detect APT41 attacks |
Tools & Frameworks
Below, we provide links to the detection content on Hacktools commonly used by the Chinese threat actors associated with the orchestrated TTP attacks targeting enterprise networks and mentioned in the Alert AA20-275A.
| Tools used by the Chinese threat actors | Actionable content on Threat Detection Marketplace |
| Cobalt Strike | Content against Cobalt Strike |
| Mimikatz | Content to detect Mimikatz |
| PoisonIvy | Content to detect PoisonIvy |
| PowerShell Empire | Content to detect PowerShell Empire |
| China Chopper Web Shell | Content to detect China Chopper Web Shell |
CVE Vulnerabilities
In order to protect critical enterprise networks, it is vital to adopt technical recommendations on patching known vulnerabilities. To reduce the overall infrastructure’s vulnerability, organizations need to maintain a patching cycle. Threat Detection Marketplace delivers actionable content to spot malicious activities connected with the exploitation of vulnerabilities listed in the Alert AA20-275A.
| Vulnerability | Content to detect malicious activity |
| CVE-2012-0158 | Content to detect CVE-2012-0158 |
| CVE-2020-5902 | Content to detect CVE-2020-5902 |
| CVE-2019-19781 | Content to detect CVE-2019-19781 |
| CVE-2019-11510 | Content to detect CVE-2019-11510 |
| CVE-2020-10189 | Content to detect CVE-2020-10189 |
Ready to try out SOC Prime Threat Detection to boost your security solutions? Sign up for free. Or join Threat Bounty Program to develop your own content and share it with the Threat Detection Marketplace community.