July turned out to be fruitful for disclosed critical vulnerabilities: CVE-2020-5903 (F5 BIG-IP), CVE-2020-8193 (Citrix ADC / Netscaler), CVE-2020-2034 (Palo Alto PAN-OS), CVE-2020-6287 (SAP Netweaver), CVE-2020-3330 (Cisco VPN / Firewalls), and CVE-2020-1350 (aka SIGRed, the vulnerability in Microsoft Windows DNS Server). Last week, Threat Bounty Program contributors and the SOC Prime team published a series of rules to detect one of the most serious vulnerabilities of this year – CVE-2020-1350, and they continue to release new rules.
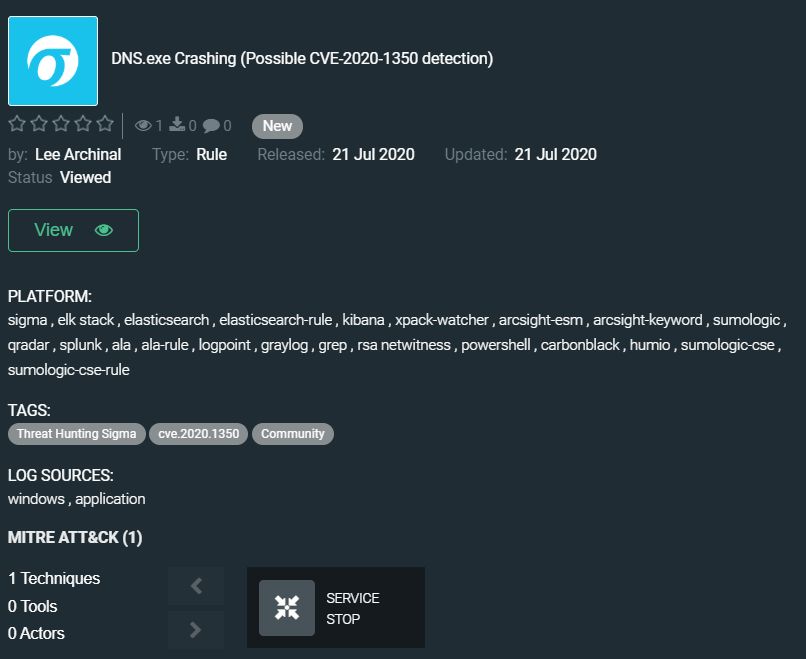
Today, in the Threat Hunting Content section, we would like to draw your attention to the community rule by Lee Archinal, which helps to detect when dns.exe crashes and could uncover attempted CVE-2020-1350 exploitation: https://tdm.socprime.com/tdm/info/juvemAPHz2Co/hsDlcHMBQAH5UgbBe0ro/?p=1
This rule can be paired with other CVE-2020-1350 detections to receive a better picture of the surrounding activity. Yes, dns.exe crashing could be due to configuration errors or other administrative tasks but could also be a sign of something malicious.
The rule has translations for the following platforms:
SIEM: Azure Sentinel, ArcSight, QRadar, Splunk, Graylog, Sumo Logic, ELK Stack, RSA NetWitness, Logpoint, Humio
EDR: Carbon Black, Elastic Endpoint
MITRE ATT&CK:
Tactics: Impact
Techniques: Service Stop (T1489)
Ready to try out SOC Prime TDM? Sign up for free. Or join Threat Bounty Program to craft your own content and share it with the TDM community.