We continue to draw your attention to rules whose capabilities are beyond the more common detection content analyzing Sysmon logs. Today in our digest there are two rules for detecting attacks on Web Servers, a continuation of a series of rules (1, 2) for discovering traces of Outlaw hacking group attacks, and detection content that uncovers GRIFFON backdoor and Qulab Trojan.
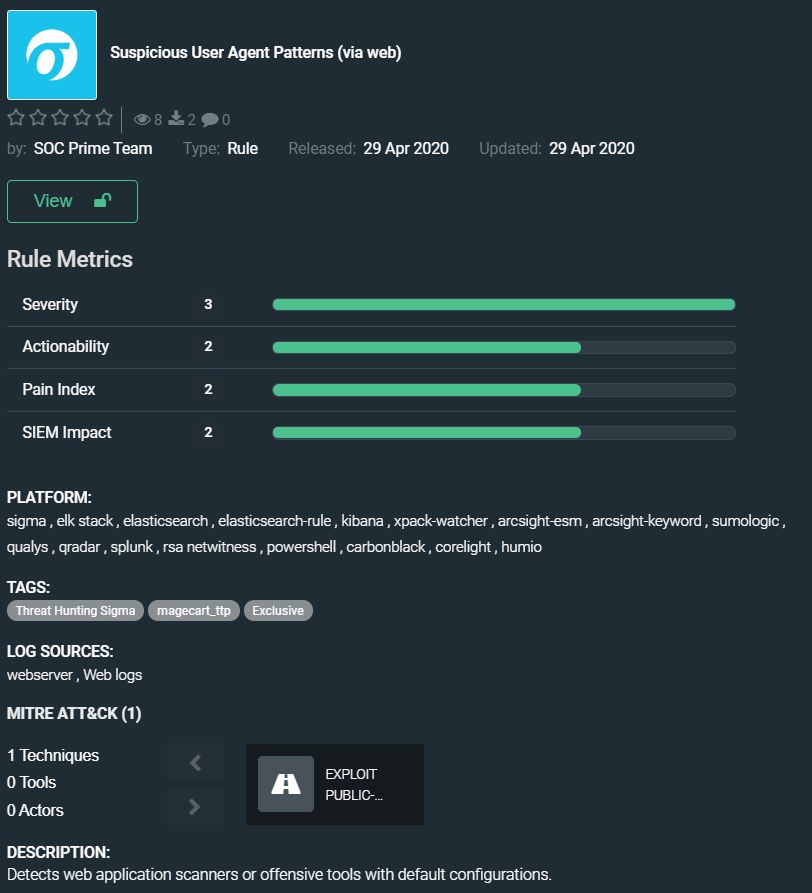
Suspicious User Agent Patterns (via web) by SOC Prime Team
https://tdm.socprime.com/tdm/info/sPx0vvd77u3g/GuZ7OnEBv8lhbg_iHiB9/?p=1
This rule helps your security solution to find suspicious User-Agents in web logs and detect web application scanners or offensive tools with default configurations.
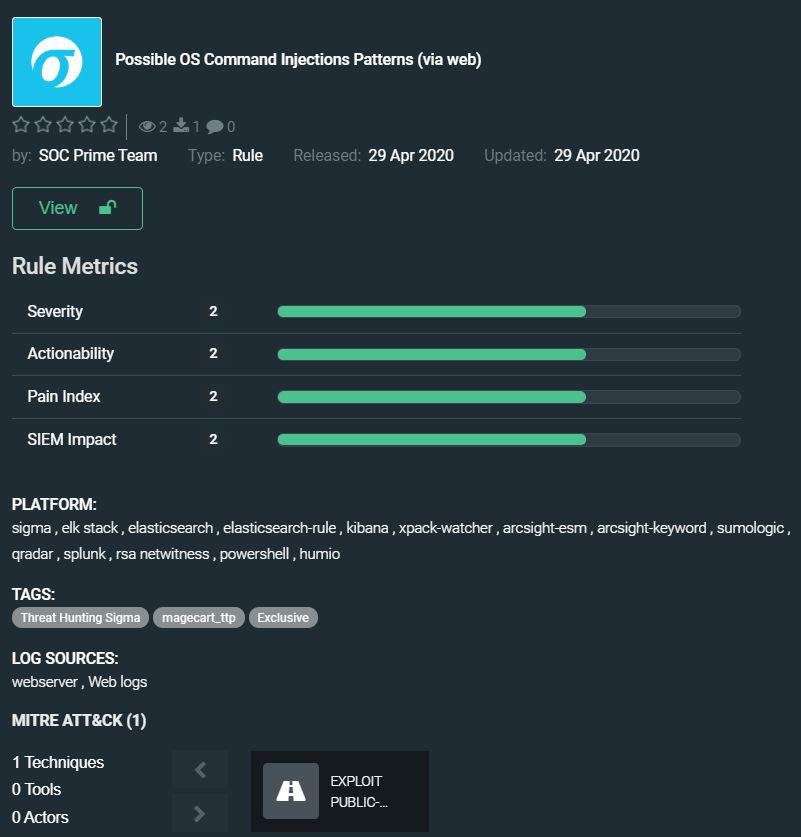
Possible OS Command Injections Patterns (via web) by SOC Prime Team
https://tdm.socprime.com/tdm/info/NCkwfXD408mF/_QlaxnEBAq_xcQY4Ne4e/?p=1
This rule helps protect your web server from a threat far greater than malicious bots. With it, you can detect shell injection which can allow adversaries to execute arbitrary operating system commands on your web server. Shell injection can lead to the compromising of other parts of the hosting infrastructure and lateral movement to other systems within your organization’s network.
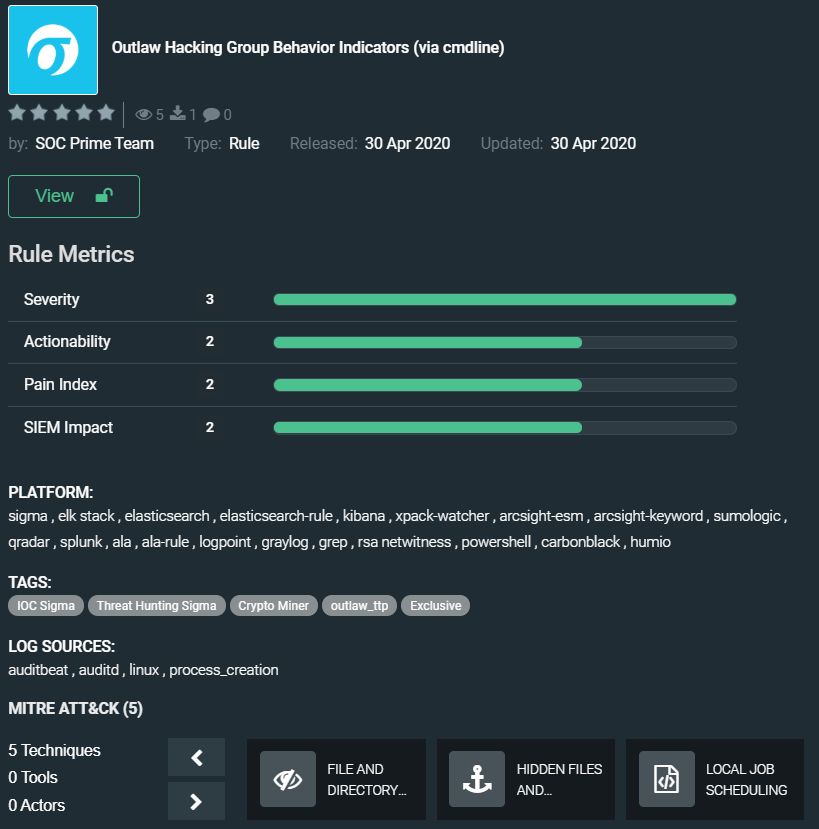
Outlaw Hacking Group Behavior Indicators (via cmdline) by SOC Prime Team
https://tdm.socprime.com/tdm/info/O5ZiqqZ4DzqR/-CHjy3EBjwDfaYjK9Evp/?p=1
We wrote about this group in detail in a post on the community Sigma rule. The Outlaw Hacking Group Behavior Indicators rule helps detect malicious actions that go unnoticed by other rules. This content has also been translated to more platforms than the universal threat hunting Sigma.
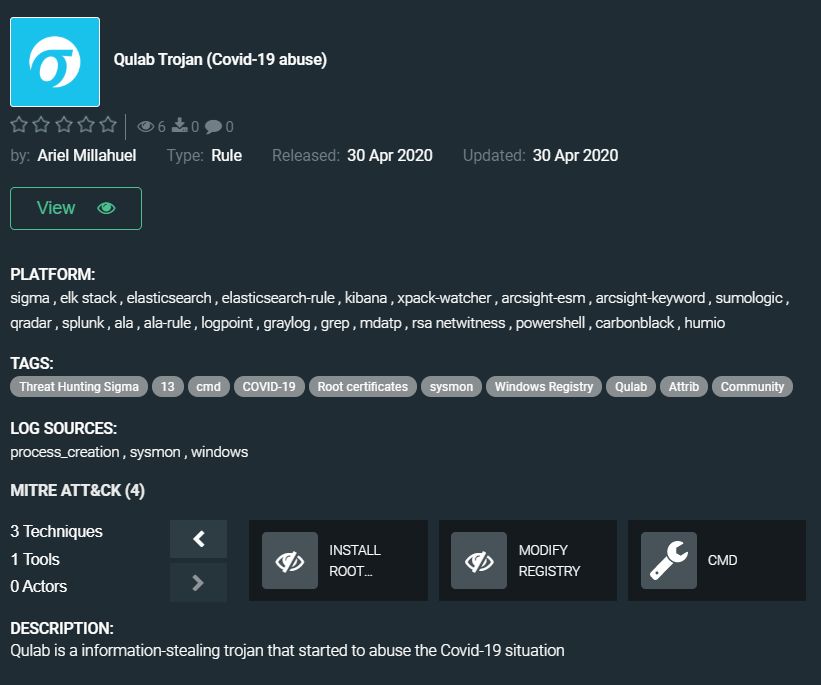
Qulab Trojan (Covid-19 abuse) by Ariel Millahuel
https://tdm.socprime.com/tdm/info/OfeYx3G0RNhn/YiGwynEBjwDfaYjKfkqA/?p=1
Ariel’s new rule helps to detect the Qulab Clipper Trojan that is used to monitor the infected computer’s clipboard and replace information associated with digital currency transactions. Trojan also can gather and exfiltrate private data from the attacked machine. The Qulab Clipper is being distributed on hacking forums, and researchers spotted new versions of the malware that appeared in the midst of the COVID-19 pandemic
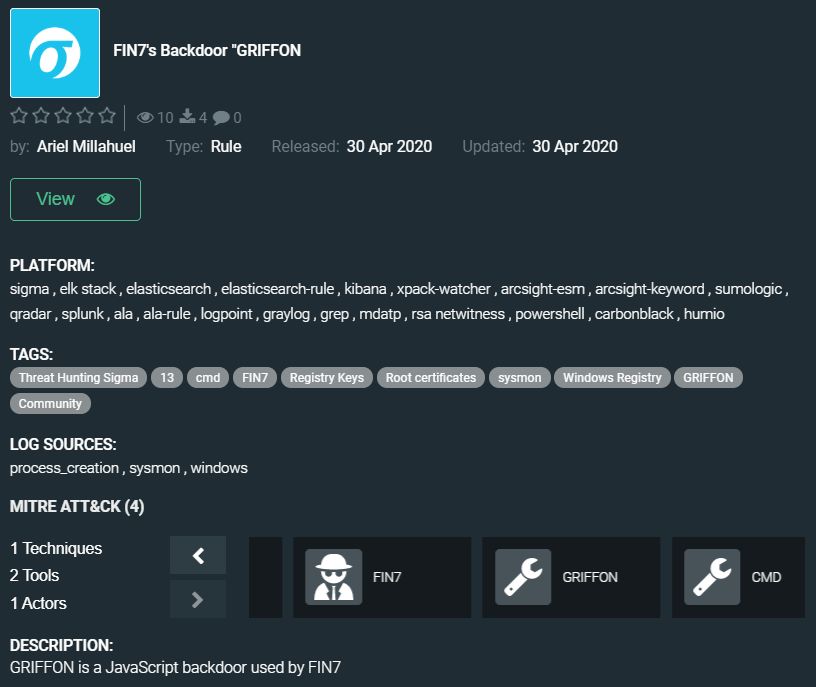
FIN7’s Backdoor “GRIFFON by Ariel Millahuel
https://tdm.socprime.com/tdm/info/BlYPRF42TjGl/Wgm3ynEBAq_xcQY4h_IZ/?p=1
The FIN7 group doesn’t need a special introduction, they attack financial institutions worldwide for 6+ years, and the arrest of their leaders did not lead to the breakup of the group. GRIFFON javascript delivery backdoor was spotted in their recent attacks, cybercriminals abuse the ActiveX control to execute the malicious macro automatically following an enable of the Document content. Community threat hunting Sigma rule by Ariel Millahuel spots characteristics of GRIFFON backdoor which is used for gathering information and downloading other tools used by the group.
The rules from this collection have translations for the following platforms:
SIEM: Azure Sentinel, ArcSight, QRadar, Splunk, Graylog, Sumo Logic, ELK Stack, RSA NetWitness, Logpoint, Humio, RSA NetWitness
EDR: Windows Defender ATP, Carbon Black, CrowdStrike, Elastic Endpoint
NTA: Corelight
MITRE ATT&CK:
Tactics: Initial Access, Execution, Persistence, Defense Evasion
Techniques: Exploit Public-Facing Application (T1190), Command-Line Interface (T1059), File and Directory Permissions Modification (T1222), Hidden Files and Directories (T1158), Local Job Scheduling (T1168), Scripting (T1064), Install Root Certificate (T1130), Modify Registry (T1112)
Join our Threat Bounty program, write and publish useful detection content, and maybe next week your rule will appear in the digest and your interview will be published on our blog.
Learn more about the program: https://my.socprime.com/en/tdm-developers
Read interviews with our top developers: https://socprime.com/en/tag/interview/