Overview and Analysis, Top Data Sources, and Relevant Sigma Rules to Detect Execution
SOC Prime’s Detection as Code platform provides access to a constantly growing library of 180,000+ context-enriched detection and response algorithms aligned with the MITRE ATT&CK® framework v.10. The newly released On Demand subscription tiers for SOC Prime’s platform provide curated Sigma rules addressing the Execution tactic (TA0002) as per the MITRE ATT&CK framework allowing teams to obtain the most up-to-date detections matching the organization’s threat profile.
This blog article provides an overview and analysis of the Execution tactic along with top log sources and relevant Sigma rules available in the SOC Prime’s platform.
Explore Platform Book a Meeting
What is Execution (TA0002)?
Execution tactic is the execution of code for malicious purposes. This can be an exe or dll code execution or the latter made through a feature that runs arbitrary code (like scripts, Java applications, etc). Adversaries often rely on the ability to execute code, especially on non-cloud based applications, such as employee workstations and servers.
Execution Detection Rules
When it comes to MITRE ATT&CK tactics and techniques, there is no “one rule to rule them all”. Detecting execution requires an extensive set of rules and a process that accounts for new techniques, tools, and implementations once they arise.
Sigma is considered a de-facto standard for expressing threat hunting queries that can be used across multiple SIEM, EDR, and XDR solutions depending on the organization’s technology stack in use. To learn more about the Sigma standard, please refer here. Also, explore the Sigma repository on GitHub for more details.
Security practitioners are welcome to join SOC Prime’s Detection as Code platform to explore the broad collection of Sigma rules with translations available for 25+ SIEM, EDR, and XDR language formats. Alternatively, teams can leverage the Uncoder.IO online Sigma translation engine to instantly convert the detection source code to the security solution in use or leverage the Sigma Converter, the SIGMAC tool, via a command-line interface.
Please find below the following recommended Sigma rules to detect execution:
Behavior Rule: Suspicious PowerShell Download
This Sigma rule identifies PowerShell downloader patterns. It is common for early-stage malware (office droppers for instance) to leverage PowerShell to download additional malicious code.
Exploit Rule: CVE-2021-26857 Exchange Exploitation
This rule identifies potential CVE-2021-26857 exploitation by identifying unusual child processes of an exchange executable.
Tool Rule: Malicious PowerShell Commandlets
This rule identifies common malicious PowerShell frameworks by their commandlet names.
Cloud Rule: AWS EC2 Startup Shell Script Change
This rule identifies the creation or modification of startup scripts within Amazon AWS’s EC2 virtual compute instances (Linux / Windows Virtual Machines, etc.).
Explore Platform Book a Meeting
Execution Detection: Most Common Log Sources
Sigma detection rules are based on log sources that exist in the organization-specific environment. Here are five common log sources generally required to detect execution.
Process Creation
It goes almost without saying that process creation is the most obvious data source someone can gather for execution. Largely execution requires a host process. However, process creation is not an execution panacea. There are often times when new processes are not required (process injection, shell code execution, etc).
Here are some common process creation log sources:
- Windows Security Logs
- 4688, validate that command line details are included
- Sysmon for Windows and Sysmon for Linux
- Event Id 1
- Linux Auditd Logs
- execve event type
- Endpoint Detection & Response (EDR) | eXtended Detection and Response (XDR)
- Some EDR services do not provide passive or enriched process creation events.
Service Creation and Scheduled Task Creation Data Sources
It is common for threat actors to create services and tasks for execution. Below are listed the most common service and scheduled tasks creation log sources:
- Windows Security Logs
- 7045
- 4698
- Endpoint Detection & Response (EDR) | eXtended Detection and Response (XDR)
- Some EDR services do not provide passive or enriched scheduled task / service creation events
PowerShell Logs
PowerShell is commonly abused, however, it also has the best native logging out of any programming language that can execute arbitrary code at runtime (scripting languages, Java, etc).
Below are some of the most common service and scheduled tasks creation log sources:
- Windows PowerShell Logs
- 4104 – Operational Log
- 4103 – Operational Log
- 500- Legacy PowerShell Log
- Endpoint Detection & Response (EDR) | eXtended Detection and Response (XDR)
- Some EDR services do not provide passive or enriched scheduled task / service creation events
AntiVirus Logs
AntiVirus logs are among the most overlooked high-value data sources. If a malicious executable ends up on one of your systems, and an end-user hasn’t directly placed it there (via email, browser download, thumb drive), then you know that there has been some kind of execution.
SOC Prime’s Detection as Code platform provides detection content powered by collaborative expertise of the world’s largest cybersecurity community that produces a monolithic body of knowledge giving any security team a significant advantage in their fight against adversaries. Here are top authors who contribute to the SOC Prime’s platform through the delivery of curated content for detecting execution:
- SOC Prime Team
- Ariel Millahuel
- Threat Bounty Program developers Emir Erdogan and Osman Demir
Explore Platform Book a Meeting
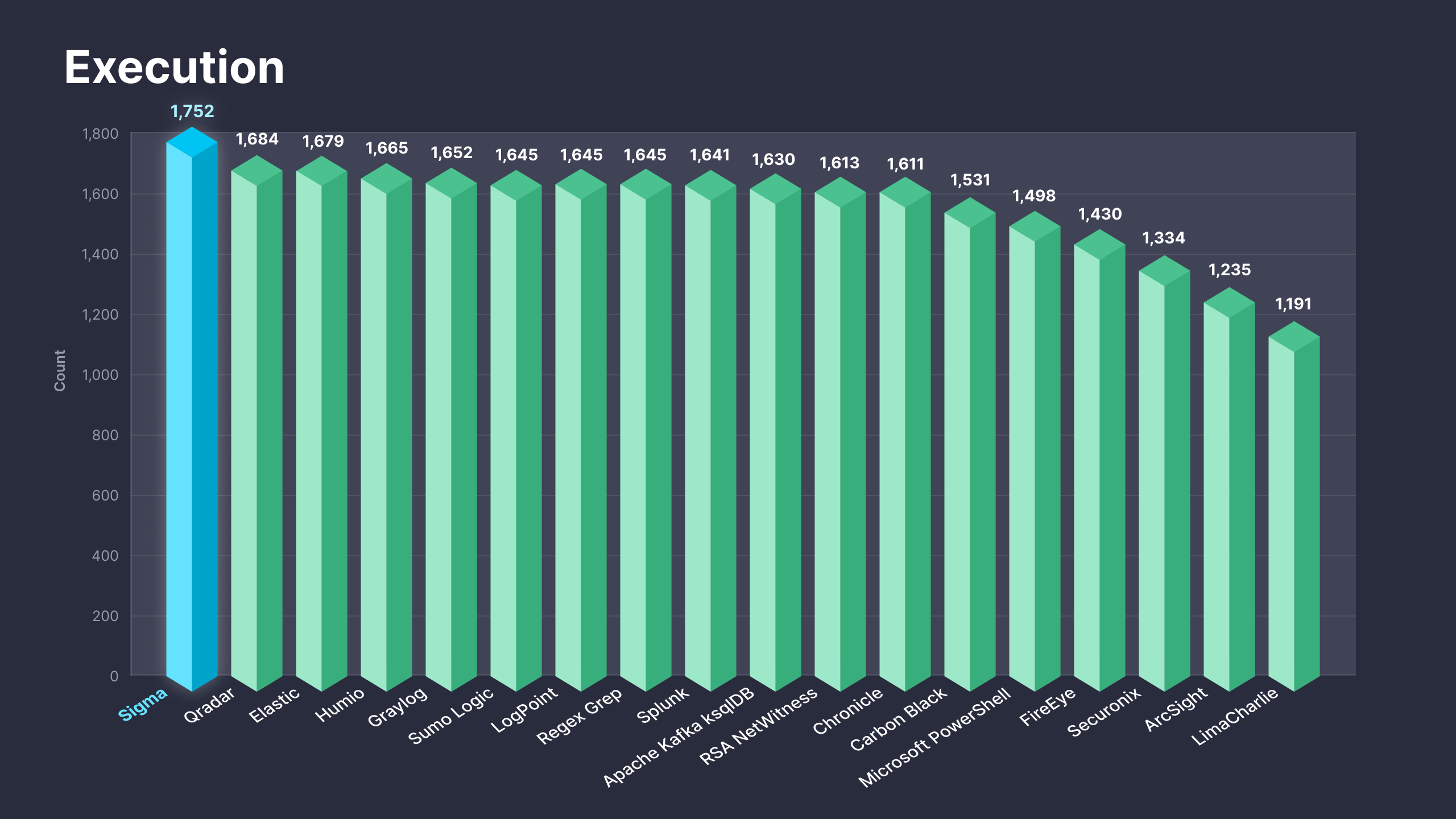
Fig. 1. Sigma rules addressing the Execution tactic (TA0002) along with translations to 25+ supported platforms
The recently released On Demand subscriptions are intended to help teams drive immediate value from SOC Prime’s Detection as Code platform by offering instant access to detection content matching the organization’s threat profile. These subscriptions deliver 1,700+ curated Sigma-based detections addressing the Execution tactic along with translations to 25+ SIEM, EDR, and XDR formats. For more details on the On Demand subscription tiers, please refer to https://my.socprime.com/pricing/.