And again, we are pleased to present our Rule Digest, which this time shows the detection content of not only the participants in the Threat Bounty Program but also the SOC Prime Team. Today we will tell you a little about Valak and HanaLoader malware, detection of data dump and MSBuild abuse, and commandline argument hijacking.
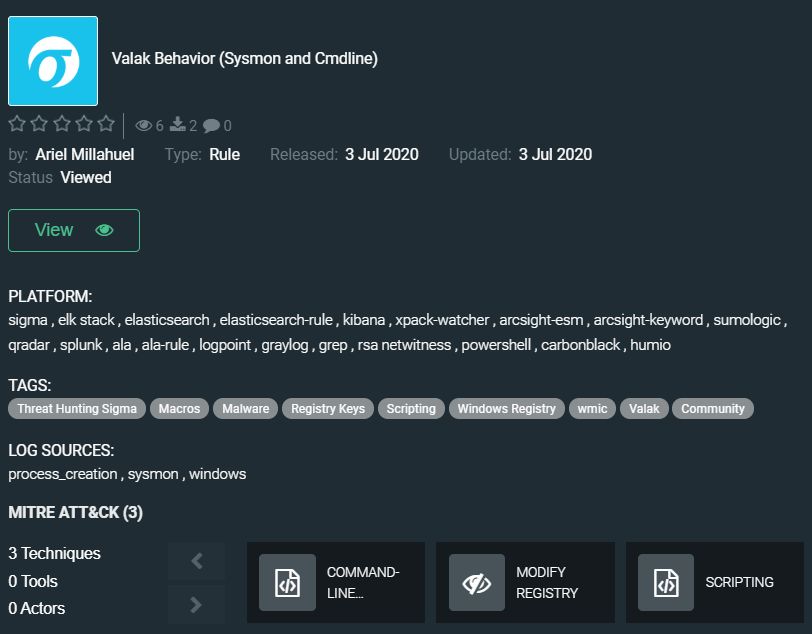
Valak malware is a sophisticated malware with a rich modular architecture that was first observed at the end of 2019. The researchers observed a series of dramatic changes in this malware and discovered over 30 different versions in less than six months. The Valak malware was first used as a loader for other tools but recently discovered versions can also be used as an information stealer to target Microsoft Exchange servers to collect and exfiltrate enterprise mailing information and passwords along with the enterprise certificate. The latest discovered campaigns spreading this malware were targeted at enterprises in the US and Germany. Valak uses advanced evasive techniques like ADS and hiding components in the registry. In addition, over time the developers of Valak chose to abandon using PowerShell, which can be detected and prevented by modern security products.
The community rule by Ariel Millahuel is based on a recently published investigation that covers the behavior of this malware that evolves constantly increasing its power: https://tdm.socprime.com/tdm/info/NLQWAy1Y6vK2/u4eGFHMBQAH5UgbB7WXX/?p=1
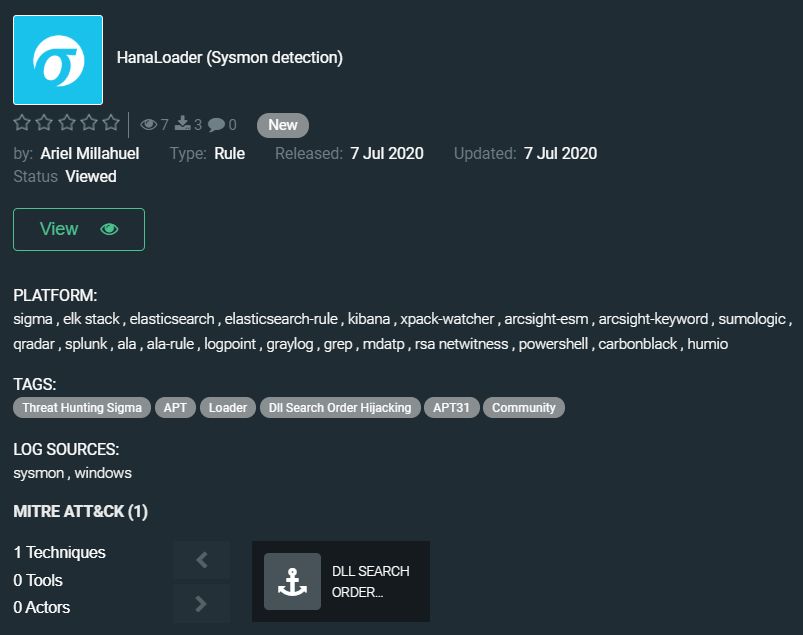
Ariel’s second rule in this digest helps detect HanaLoader malware, which was used by the APT31 group in cyber espionage campaigns to deliver DropboxAES trojan (Blog post about detection content to uncover this trojan’s activity you can find here).
Adversaries often misuse signed legitimate executable files from multiple software producers to load malicious code. In the observed campaigns, they used DLL search-order hijacking to run HanaLoader malware. It was used to download and launch an additional payload from a remote resource over HTTPS. The second-stage payload overwrites HanaLoader using process hollowing and continues to run in memory. The community rule is available on Threat Detection Marketplace: https://tdm.socprime.com/tdm/info/hfms4q3PeHd7/cbshKXMBPeJ4_8xciH_4/?p=1
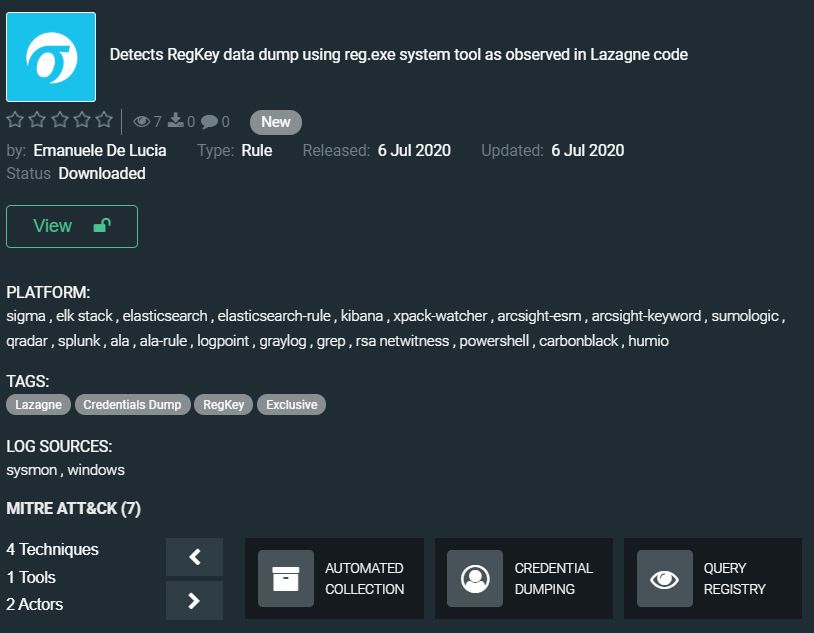
Further in our digest Emanuele De Lucia will debut with the exclusive rule “Detects RegKey data dump using reg.exe system tool as observed in Lazagne code”: https://tdm.socprime.com/tdm/info/5mYFV8usgpx7/DISbFHMBSh4W_EKGIURC/?p=1
The LaZagne project is an open-source application used to retrieve passwords stored on a local system. Each software saves passwords using various techniques (plain text, APIs, proprietary algorithms, databases, etc.), and the LaZagne was created to find these passwords for the most commonly used software. Emanuele De Lucia’s rule, based on hid our own research and Lazagne source code, enables security solutions to detect RegKey data dump. The method used by the mentioned above application to extract passwords can be used in various variations of infostealers to discreetly extract credentials.
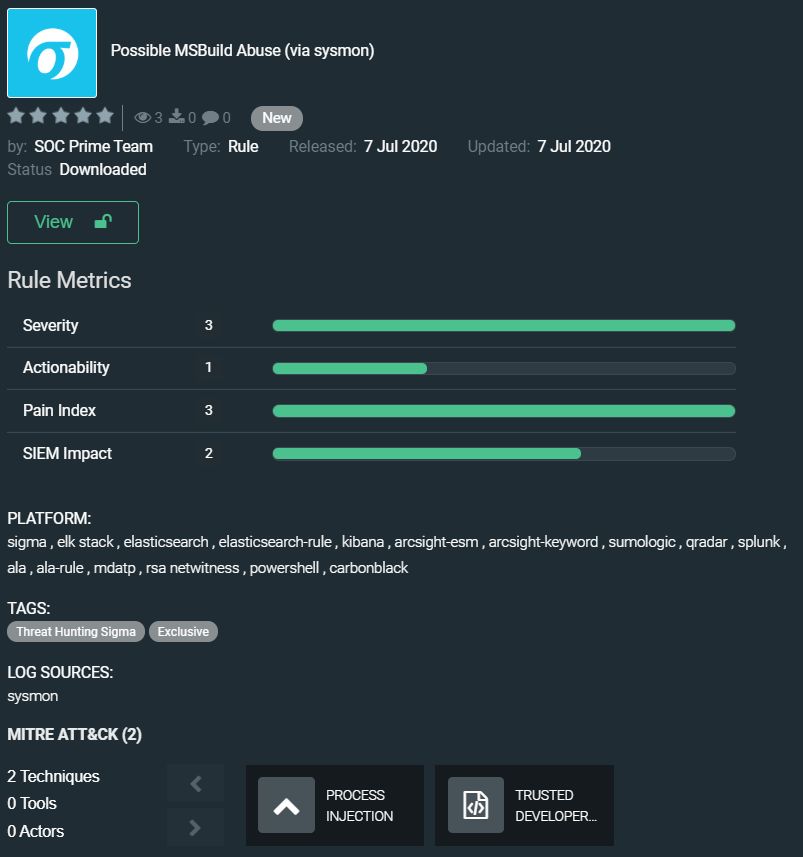
We continue our digest with the rule from SOC Prime Team – Possible MSBuild Abuse (via sysmon): https://tdm.socprime.com/tdm/info/gUVLhJkxnxH7/XJTYKXMBQAH5UgbB54V8/?p=1
MSBuild is a trusted Windows binary that is part of Microsoft .NET framework and can be utilized to build applications in environments where Visual Studio is not installed. The capability of this binary to execute code that is stored on a system locally can lead to evasion of existing security controls (Group Policy, Application whitelisting etc.) that prevent PowerShell or another similar tooling that relies on PowerShell. Adversaries can use the technique that doesn’t leave any artifacts since it doesn’t touch the disk and the code is injected into a legitimate Windows process Internet Explorer. The rule developed by SOC Prime Team helps to discover possible MSBuild abuse and stop advanced threat actors at the early stages of the cyberattack.
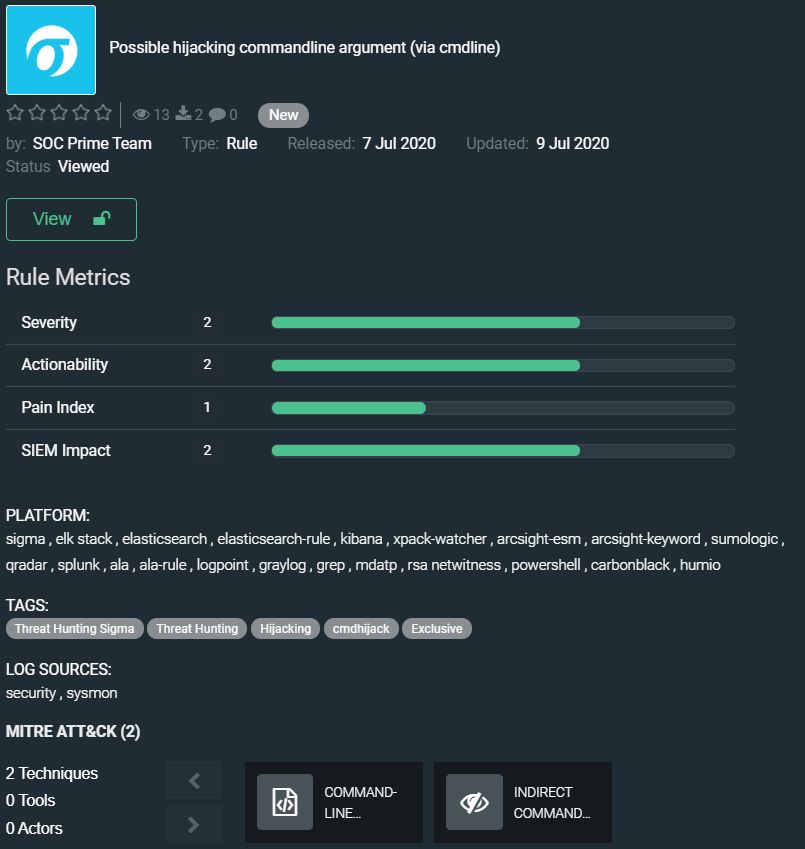
And the last rule in today’s digest is also developed by the SOC Prime Team, it is called “Possible hijacking commandline argument (via cmdline)” and its usefulness can already be understood from the name. But let’s add a few words about the rule. Adversaries may use a flaw in cmd or conhost execution to hijack commandline argument. The flaw enables cybercriminals to trick cmd.exe into running the executable of their choice. The potential impact of this includes Denial of Service, Information Disclosure, Arbitrary Code Execution (depending on the target application and system). The exclusive rule to uncover such malicious behavior is here: https://tdm.socprime.com/tdm/info/TDPHWYnqiYAq/8k91vHIBSh4W_EKGsw1R/?p=1
The rules have translations for the following platforms:
SIEM: Azure Sentinel, ArcSight, QRadar, Splunk, Graylog, Sumo Logic, ELK Stack, RSA NetWitness, LogPoint, Humio,
EDR: Microsoft Defender ATP, Carbon Black, Elastic Endpoint
MITRE ATT&CK:
Tactics: Execution, Persistence, Privilege Escalation, Defense Evasion, Discovery, Collection, Credential Access
Techniques: Command-Line Interface (T1059), Modify Registry (T1112), Scripting (T1064), DLL Search Order Hijacking (T1038), Account Discovery (T1087), Automated Collection (T1119), Credential Dumping (T1003), Query Registry (T1012), Progress Injection (T1055), Trusted Developer Utilities (T1127)
Wait for the next digest in a week.
Stay safe!