This week in our digest there are rules exclusively developed by participants of the Threat Bounty Program.
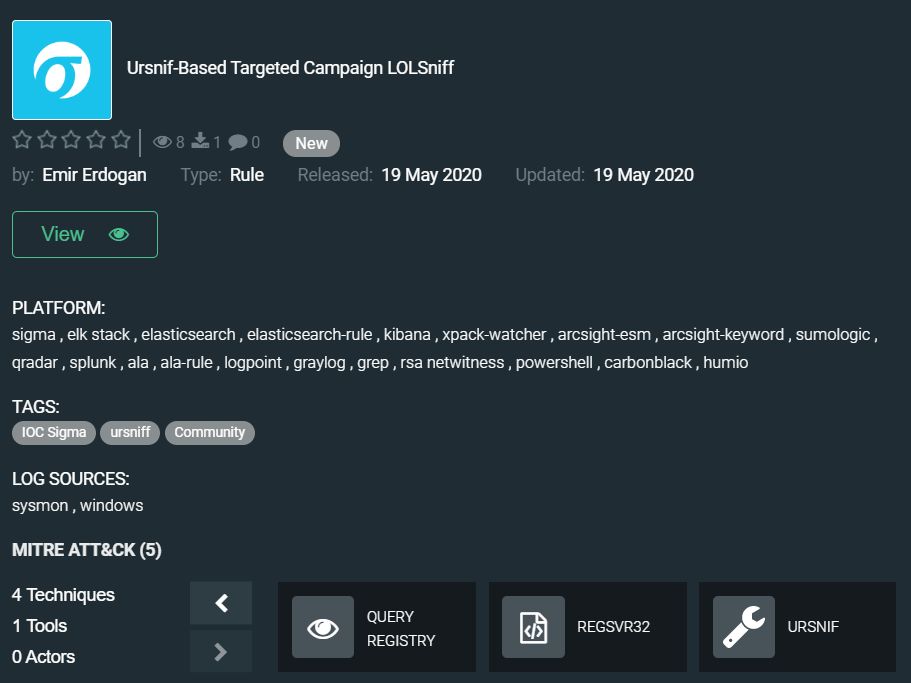
Threat actor behind the recent Ursnif variant possibly conducts targeted cybercrime operations that are still ongoing. At the heart of these campaigns is a variant of the Ursnif Trojan that was repurposed as a downloader and reconnaissance tool to meet the actor’s special needs. The techniques utilized by this actor such as LOLBins, heavy obfuscation, as well as COM interfaces and the TTPs observed by others in later stages of an attack such as utilization of post exploitation frameworks (Cobalt Strike) and VNC clients (TeamViewer) suggest that this actor is involved in targeted attacks. The attacks have been ongoing for months without much public attention. Ursnif-Based Targeted Campaign LOLSniff rule by Emir Erdogan uncovers activity of this Trojan helping to stop the attack at early stages: https://tdm.socprime.com/tdm/info/OWYy5tF4Yis6/PCE5LXIBjwDfaYjKqJBf/?p=1
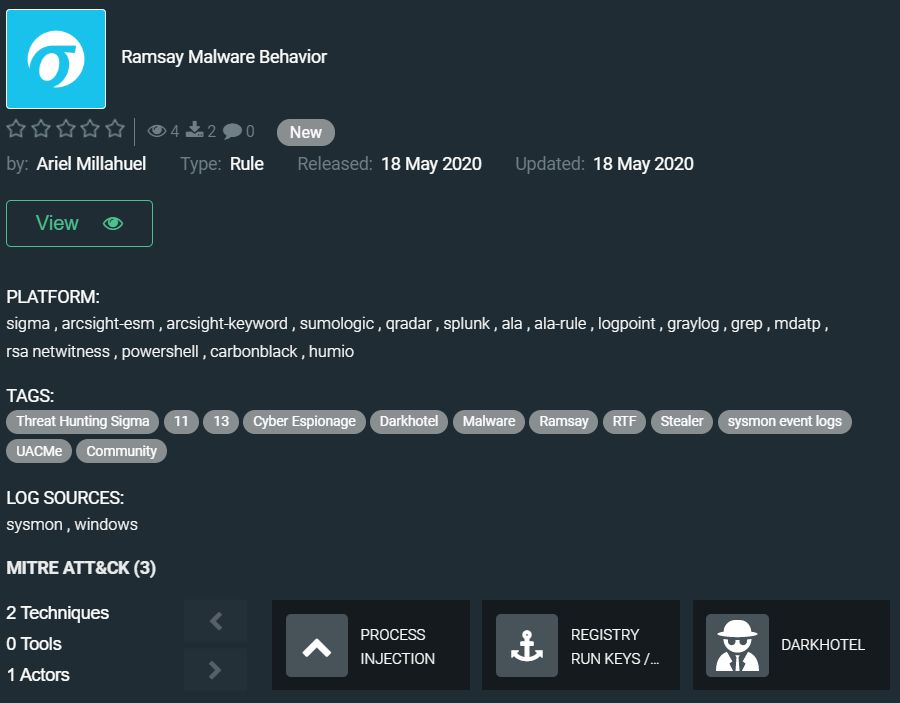
ESET researchers discovered a previously unreported cyber-espionage framework that they named Ramsay and that is tailored for collection and exfiltration of sensitive documents and is capable of operating within air‑gapped networks. Researchers tracked down three different versions of the malware, each version was different and infected victims through different methods, but at its core, the malware’s primary role was to scan an infected system and gather Word, PDF, and ZIP documents in a hidden storage folder, ready to be exfiltrated at a later date. Other versions also included a spreader module that appended copies of the Ramsay malware to all PE (portable executable) files found on removable drives and network shares. This is believed to be the mechanism the malware was employing to jump the air gap and reach isolated networks, as users would most likely move the infected executables between the company’s different network layers, and eventually end up on an isolated system. Ariel Millahuel developed community threat hunting rule to spot Ramsay Malware Behavior: https://tdm.socprime.com/tdm/info/WZnAdFuEiaVX/vyE1J3IBjwDfaYjKtYkQ/?p=1
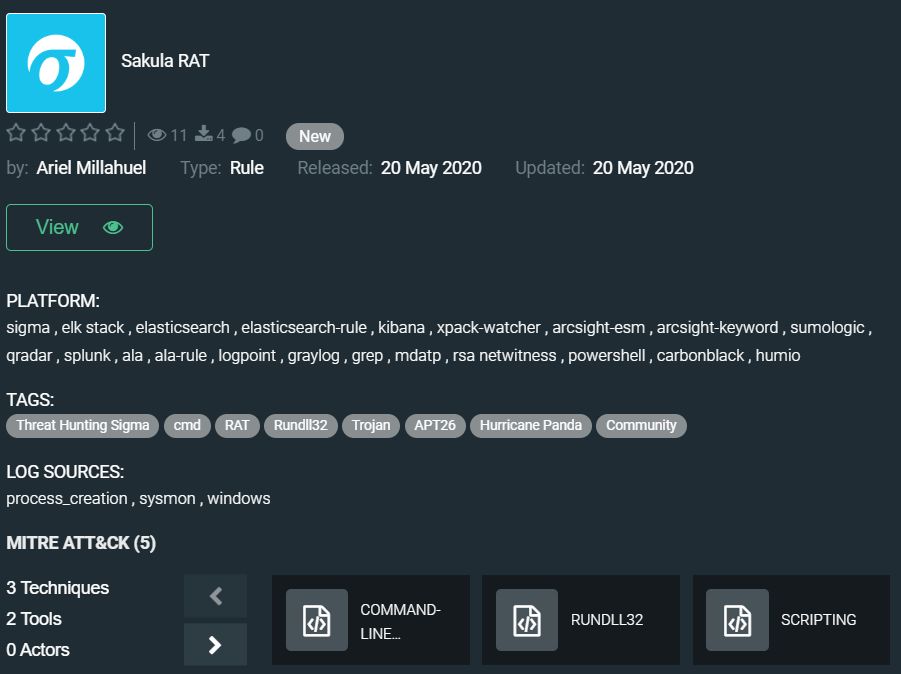
Sakula RAT is the second community threat hunting rule released by Ariel Millahuel. Sakula RAT (also known as Sakurel and VIPER) first surfaced in November 2012, it enables an adversary to run interactive commands as well as to download and execute additional components. Sakula uses HTTP GET and POST communication for command and control (C2). Network communication is obfuscated with single-byte XOR encoding. Sakula also leverages single-byte XOR encoding to obfuscate various strings and files embedded in the resource section, which are subsequently used for User Account Control (UAC) bypass on both 32 and 64-bit systems. Most samples maintain persistence through a registry Run key, although some samples configure themselves as a service. Link to the rule: https://tdm.socprime.com/tdm/info/dZ0LlEq1KcRv/1-aMMXIBv8lhbg_iM9Qo/?p=1
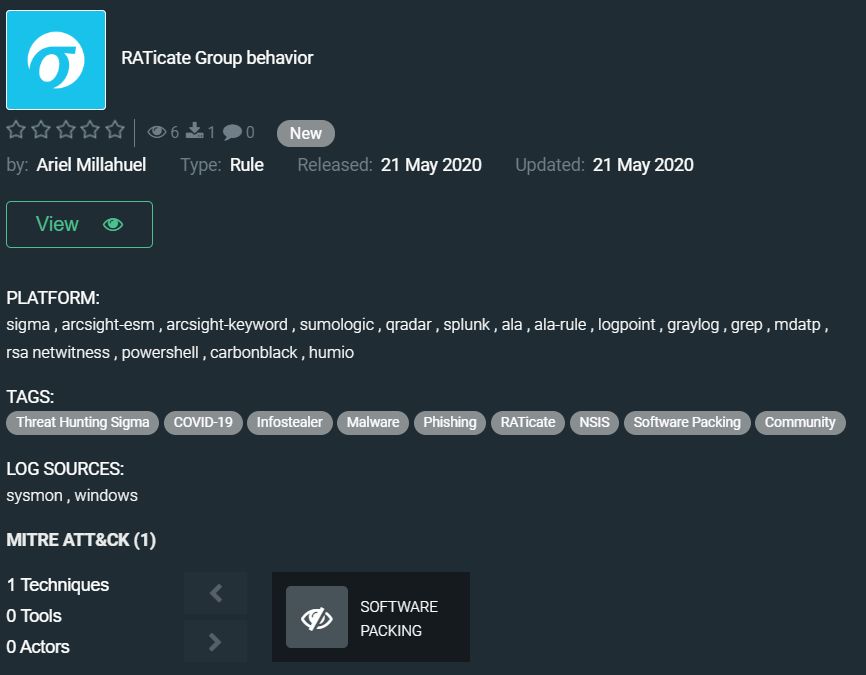
And the last rule from Ariel for today’s digest is RATicate Group behavior. Security researchers from Sophos identified a hacking group that abused NSIS installers to deploy remote access Trojans and information-stealing malware in attacks targeting industrial companies. They discovered that attacks of RATicate have been targeting industrial companies from Europe, the Middle East, and the Republic of Korea as part of five separate campaigns, although the researchers suspect that RATicate were behind other similar campaigns in the past. These campaigns targeted various types of entities of the industrial sector, ranging from companies focused on manufacturing to investment firms and internet companies. Here you can download rule RATicate Group behavior for your security solution: https://tdm.socprime.com/tdm/info/ctvl1GjnfAFH/FyHCNnIBjwDfaYjKe5fQ/?p=1
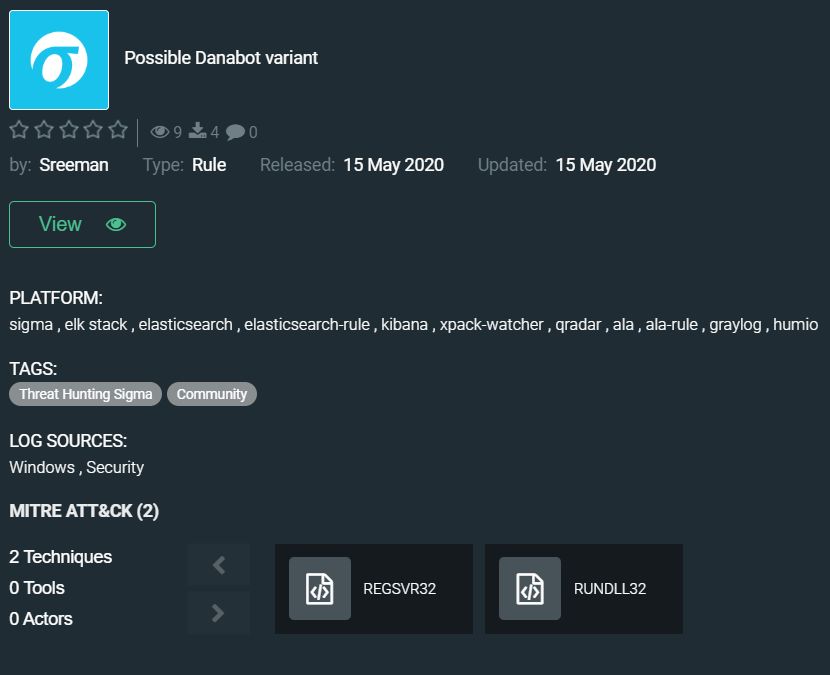
We finish our digest with the community rule from Sreeman designed to detect the recently discovered Danabot samples. First detected in May 2018, DanaBot is a powerful banking trojan that has historically focused heavily on financial services institutions in North America, Australia, and Europe. The malware has grown quickly since it was first detected, primarily due to its modularity and distribution methods. Similar to the Zeus banking trojan, DanaBot is known for its plug-and-play modules, which can drastically alter tactics and priorities. DanaBot is “overgrown” with modules and improvements providing attackers worldwide with a powerful tool for cyber attacks. Ever since this malware emerged on the banking trojan scene, it has been a heavy hitter, causing significant damage wherever it goes. Check the rule here: https://tdm.socprime.com/tdm/info/8MnRbno0JNH8/MowrGHIB1-hfOQirhDbo/
The rules from this collection have translations for the following platforms:
SIEM: Azure Sentinel, ArcSight, QRadar, Splunk, Graylog, Sumo Logic, ELK Stack, RSA NetWitness, Logpoint, Humio
EDR: Carbon Black, Elastic Endpoint
MITRE ATT&CK:
Tactics: Defense Evasion, Execution, Persistence, Privilege Escalation, Discovery
Techniques: Regsvr32 (T1117), Rundll32 (T1085), Software Packing (T1027.002), Scripting (T1064), Command-Line Interface (T1059), Registry Run Keys / Startup Folder (T1060), Process Injection (1055), Install Root Certificate (T1130), Modify Registry (T1112), Query Registry (T1012)
Link to our last digest: https://socprime.com/en/blog/rule-digest-rce-cve-oilrig-and-more/
See you in a week.