This digest includes rules from both members of the Threat Bounty Program and the SOC Prime Team.
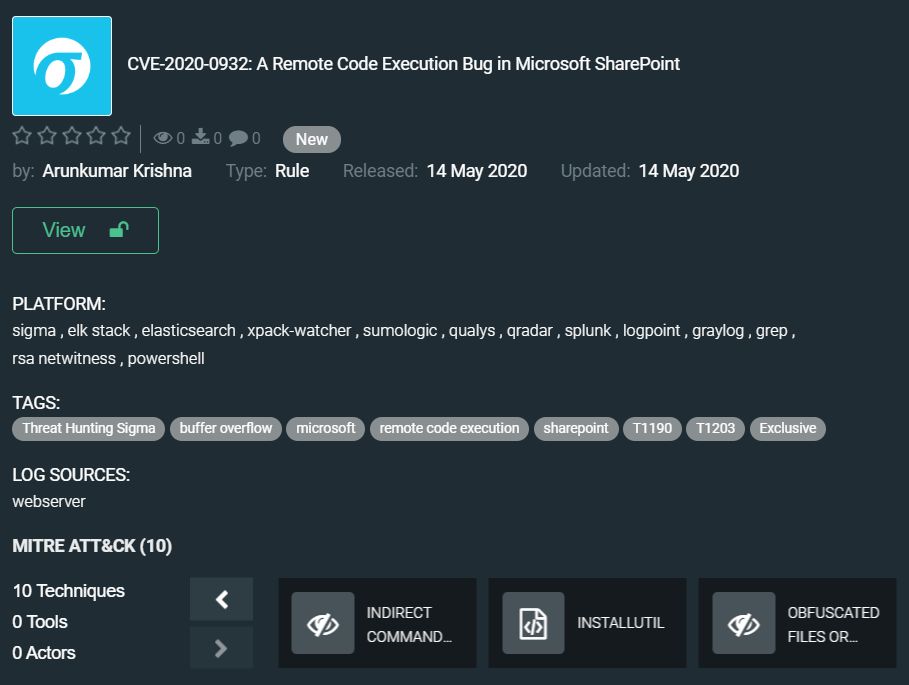
Let’s start with rules by Arunkumar Krishna which will debut in our Rule Digest with CVE-2020-0932: A Remote Code Execution Bug in Microsoft SharePoint.
CVE-2020-0932 was patched in April, it allows authenticated users to execute arbitrary code on a SharePoint server. The default configuration of SharePoint allows any authenticated user to exploit this vulnerability. Such bugs were popular with attackers in time past, so it would be helpful to have a rule that discovers exploitation attempts: https://tdm.socprime.com/tdm/info/zzrJT94vXLN2/4iG6EnIBjwDfaYjKDnwP/
Arunkumar also posted YARA rules to track exploitation of this vulnerability: https://tdm.socprime.com/tdm/info/vMZFVxJCHsrf/2uapEnIBv8lhbg_iH76X/
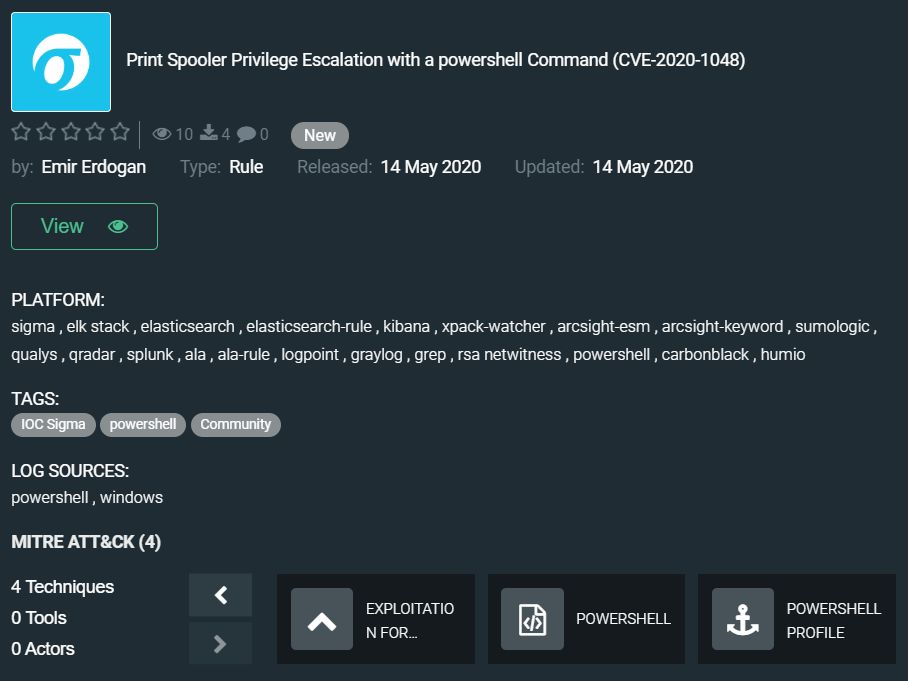
Emir Erdogan published a rule for a very fresh vulnerability patched this week – Print Spooler Privilege Escalation with a powershell Command (CVE-2020-1048). Attackers can exploit this vulnerability and run arbitrary code with elevated system privileges to install malware, modify data, or create new accounts with full user rights. They also can use it to elevate privileges, bypass EDR rules, gain persistence, and more. PoC exploit is also available for this security flaw.
Rule by Emir Erdogan is a Community one and is available to all registered TDM users, check it: https://tdm.socprime.com/tdm/info/durVnL5VeTW2/d4y1EnIB1-hfOQirFzA6/
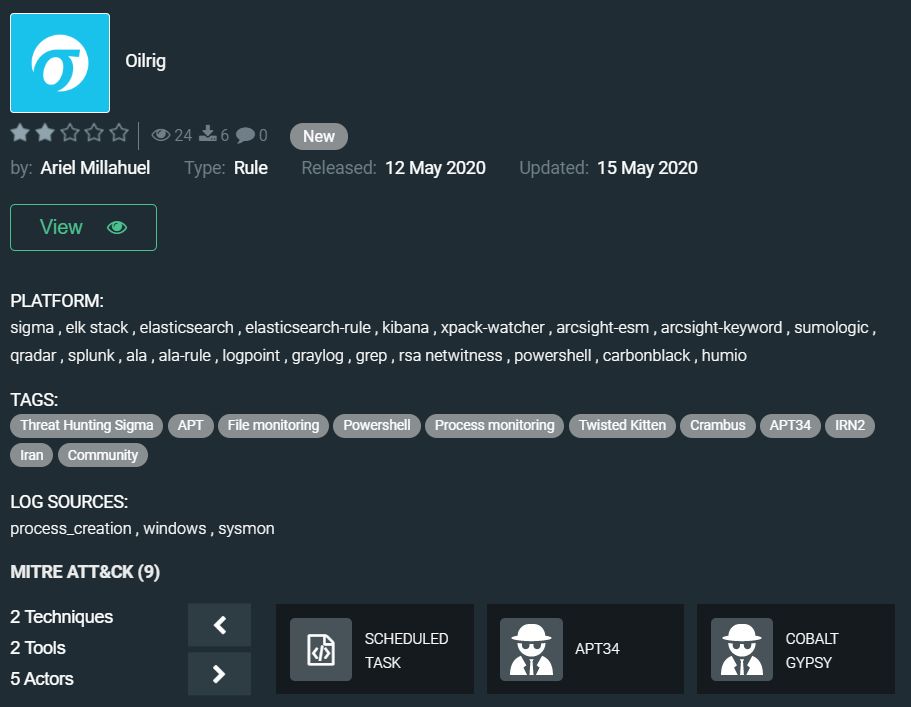
The next rule in our digest is submitted by one of our most active Threat Bounty Program members whose rules appear on the blog every week, and you can read his interview here. New Community rule by Ariel Millahuel discovers Oilrig cyberespionage activity.
Oilrig group also known as APT34 and Helix Kitten has performed cyberattacks in the interests of the Iranian government since 2014. They are most active in the Middle East, but this year they updated their arsenal to attack the US government entities. Security researchers are regularly finding new tools related to this APT group. The rule published by Ariel is based on recent findings and can detect Oilrig group activity on your organization network: https://tdm.socprime.com/tdm/info/Nvw0NkZgaA6d/JCEsoXEBjwDfaYjK9SI6/
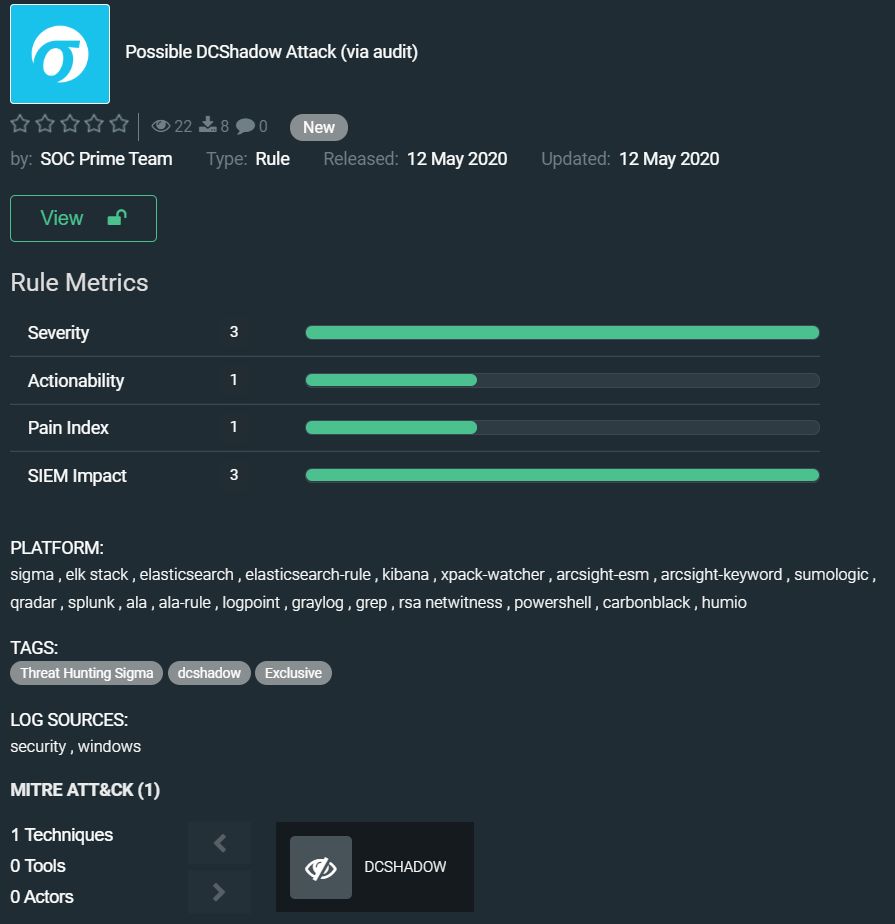
The rule by SOC Prime Team detects DCShadow attack on Domain Controller (DC). Adversaries can use Mimikatz features to create a fake Active Directory DC and make changes to a legitimate DC through replication. You can read more about this attack here: https://attack.stealthbits.com/how-dcshadow-persistence-attack-works
Link for downloading Possible DCShadow Attack (via audit) exclusive rule here: https://tdm.socprime.com/tdm/info/i7cPkU1ko5H7/ATk-0G0BLQqskxffBI6L/
The last rule in today’s digest is Possible REG.EXE usage for persistence (via cmdline) by SOC Prime Team. Modern advanced malware often uses the Windows registry for persistence and even fileless execution. The rule detects attempts to establish a foothold on compromised host: https://tdm.socprime.com/tdm/info/eri0Ie3zVuoB/hSGzwXEBjwDfaYjKpEI5/?p=1
The rules from this collection have translations for the following platforms:
SIEM: Azure Sentinel, ArcSight, QRadar, Splunk, Graylog, Sumo Logic, ELK Stack, RSA NetWitness, Logpoint, Humio, RSA NetWitness
EDR: Windows Defender ATP, Carbon Black, CrowdStrike, Elastic Endpoint
NTA: Corelight
MITRE ATT&CK:
Tactics: Defense Evasion, Lateral Movement, Command and Control, Initial Access, Credential Access, Privilege Escalation, Execution
Techniques: Application Access Token (T1527) Data Obfuscation (T1001), Exploit Public-Facing Application (T1190), Exploitation for Credential Access (T1212), Exploitation for Privilege Escalation (T1068), Exploitation of Remote Services (T1210), File and Directory Permissions Modification (T1222), Indirect Command Execution (T1202), InstallUtil (T1118), Obfuscated Files or Information (T1027)