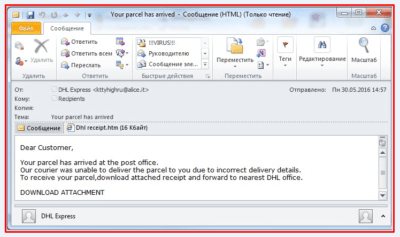
Hello everyone! Today we will focus on the fresh example of the simple phishing from the actual practice as always. Let’s analyze the following letter:
As we see on the screenshot, there is an attachment – htm page and it is offered to be opened by unsuspecting “parcel recipient”.
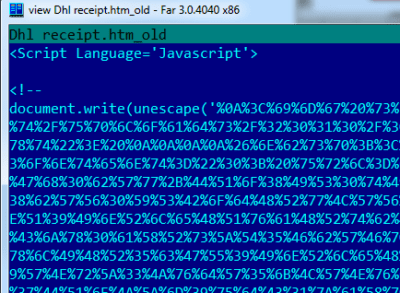
Inside this document we can see a JS code containing a Unicode string value coded with “escape” function.
Fragment
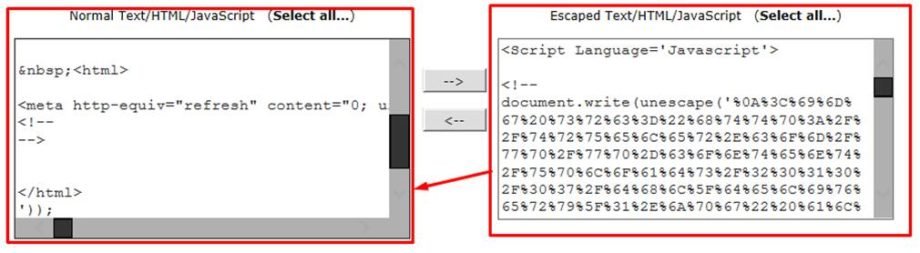
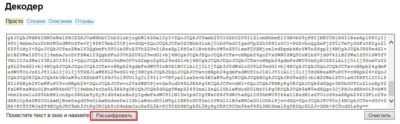
We can use the following resource for decoding this fragment:
After decoding we can see that the text is still coded base64:
Let’s decode it.
For our purposes we can use for example, http://www.artlebedev.ru/tools/decoder/:
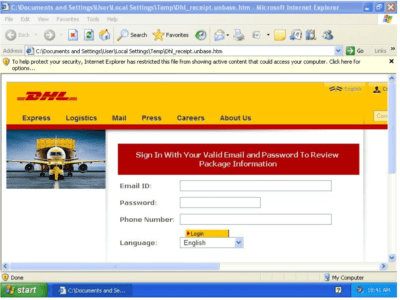
As a result, we receive code of the page that is opened locally, and it imitates the official DHL web page. So this page is a perfect source of gathering DHL accounts’ emails and passwords.
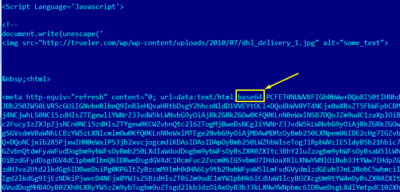
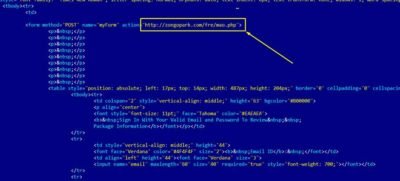
Among other things there is a link to a resource in the body of this page:
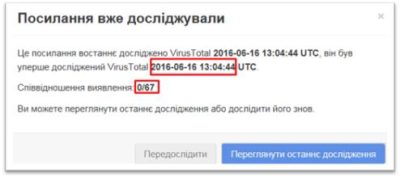
Somehow it is considered to be “clear”:
When you try to open this webpage you are redirected to the DHL website. As a result user does not suspect anything if he checks link in browser and he is made sure that he is on the DHL web page:
As we can see in the traffic, there is a post with the transmission of a provided password and email on the false page; and then there is a redirect to the DHL site as expected.
So there is a real phishing of the DHL accounts.
We can only block this link on the firewall and one more time remind the users that they should carefully check the link if they are asked for the passwords.