The process of stealing data from a corporate system is also known as exfiltration. MITRE ATT&CK® has dedicated an entire tactic to illegal copying, downloading, and transferring of organizations’ internal data with significant levels of sensitivity. Data exfiltration examples can be quite obvious, like copying files to a thumb drive; and quite stealthy, like DNS over HTTPS tunneling. Let’s look at exfiltration more closely and find ways of preventing and detecting this tactic.
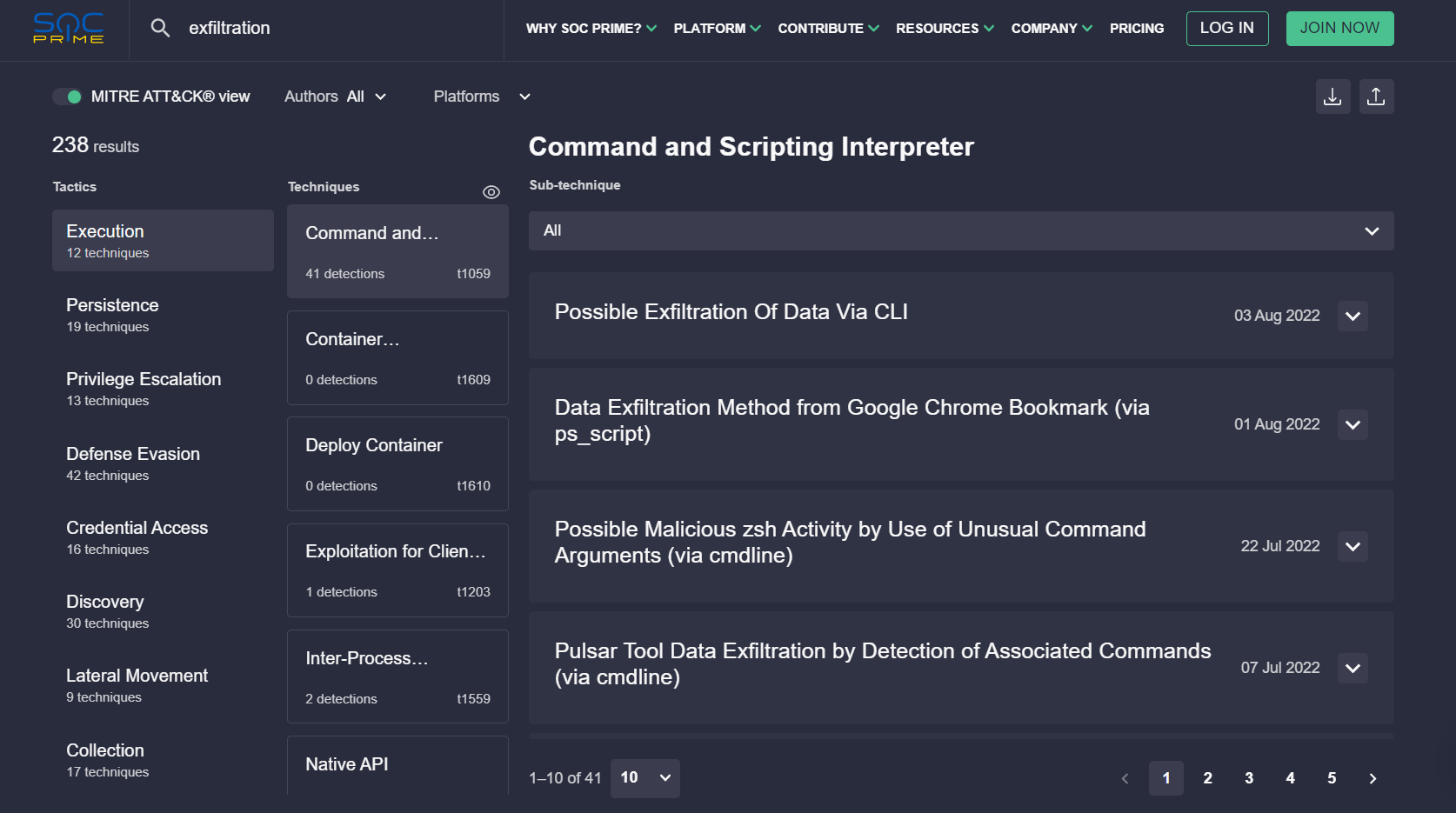
SOC Prime’s dedicated security team, together with a worldwide community of Threat Hunters and Detection Engineers, continuously works on finding new ways to detect cybersecurity threats. Our Cyber Threats Search Engine provides instant access to the CTI context, MITRE ATT&CK mapping, and relevant Sigma-based detections. Click the button below to see the entire collection of Sigma rules for detecting Exfiltration (TA0010).
Switch to the MITRE ATT&CK view to explore search results aligned with the MITRE ATT&CK framework and drill down to all available techniques of the Exfiltration tactic.
How Does Data Exfiltration Work?
One of the most widely used methods of stealing data is to transfer it by a network channel that connects an enterprise with the outer world. Internet traffic, in this case, is used in multiple different ways. Attackers typically try to obfuscate the data, compress and encrypt it before exfiltrating. Small pieces of information can be embedded in steganography images, DNS queries, packet metadata, and so on. The traffic might also be intercepted and analyzed by adversaries in real time.
Most commonly, cyber-attacks are aimed at exfiltrating the data that victims already have. However, some types of malware also record and collect new data that is not stored within the organization’s infrastructure. For example, attackers might use devices and applications that record audio and video, keystrokes, and clipboard copies. All these actions can be performed either automatically or manually through remote access tools.
Types of Data Exfiltration
Now let’s dive a little bit deeper into exploring the particular ways in which data can be exfiltrated from digital infrastructures to third-party locations without the owner’s consent or awareness.
Automated Exfiltration
Malicious data exfil rarely looks like a spy movie these days. Instead, the files might quietly download in the background and blend in with the legitimate traffic. In addition, sub-techniques like T1020.001 are used to mirror the monitored traffic, which is a native feature in some network analysis tools and devices. Below is a visualized example of a quiet exfiltration.
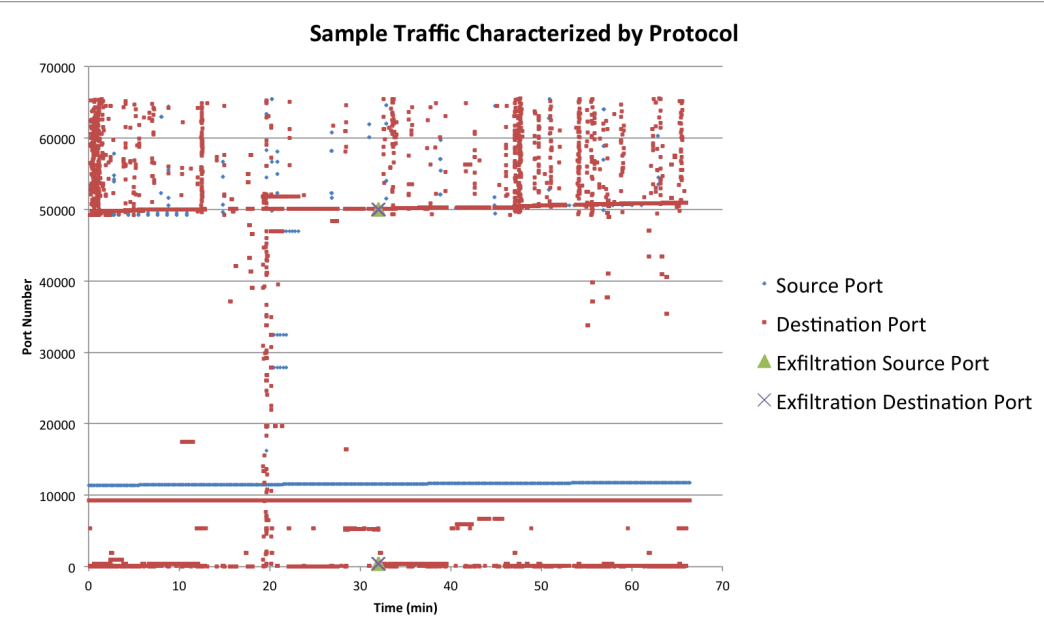
Image source: “Exfiltration Techniques: An Examination and Emulation” by Ryan C. Van Antwerp, Spring 2011
Bite-Sized Data Exfiltration
Obviously, enormous volumes of data transfers will be easily noticed by security experts. Adversaries know that; that’s why some of them attempt to divide the data into small chunks and quietly take them away (T1030). This way, attackers don’t mess with data transfer thresholds and generate no alerts. As a result, exfiltration might stay undetected for a significant period of time.
For example, Cobalt Strike first builds a beacon for low and slow communication with a C2 channel. Then, during each check-in, the beacon has a task to download a certain file. It splits the file into chunks and downloads them little by little. The chunk size depends on the current data channel. For HTTP/HTTPS, the size is 512KB. And it’s not even the smallest size. A backdoor dubbed Helminth sends data in 23-byte pieces in DNS queries.
Exfiltration Channels: C2 vs. Alternative Protocol
It’s reasonable to suggest that attackers will be trying to steal data through an already established C&C channel. However, it’s not always the case.
Here are the MITRE ATT&CK techniques to cover:
- T1041 – Exfiltration over C2 channel
- T1048 – Exfiltration over alternative protocol
During analysis, it may also occur that destination locations for exfiltrated files might vary. To hide their tracks, adversaries may use a variety of protocols (all of them will differ from the one used for a C2 channel communication), like FTP/S, SMTP, HTTP/S, DNS, Net/SMB, and more. An alternative protocol might also mean transfers within the web services like cloud storage. The traffic can be encrypted with a symmetric cryptography algorithm, as well as an asymmetric one. The data can also be obfuscated without any encryption: it is possible to do by using public encoding and compression algorithms, such as base64, or embedding data into protocol headers/fields like HTTP POST. Built-in utilities can be exploited here, too. For example, a WindTail surveillance implant abuses a macOS /usr/bin/curl.
Exfiltration Medium – Wireless and Physical
Wireless network channels are not the most widely used – MITRE ATT&CK doesn’t give any procedure examples yet. However, if an organization has a closed physical perimeter as such and they haven’t entirely transitioned to BYOD, this scenario remains possible.
The alternative medium might include:
- Bluetooth
- Wi-Fi
- Modem
- Cellular channel
- Radiofrequency channel(s)
For most of these channels, attackers must be physically close enough to make it work. Also, these connections aren’t as stealthy as the Internet channels for C2 communication. Here, adversaries don’t really have to hide their traffic because it’s not being sent through a victim’s network. As a result, this traffic won’t be visible by firewalls or any other means of data loss prevention established within the organization’s infrastructure.
When it comes to a physical medium, the first thing that pops up in mind is a USB. And yes, they are still in use by the attackers. Alternatively, it might be an external hard drive, MP3 player, mobile device – anything that has physical storage. If a target system has no connection to the Internet and other networks, then physical exfiltration is perhaps the only way to go. Spy movie scenes with persons sneaking into server rooms are applicable here.
Web Services Exploited for Exfiltration
Legitimate and not-compromised web services can unintentionally become good channels for exfiltration for a few reasons. First, the organization’s firewalls can have rules for allowing data exchange within such a service. It might be something like Google Drive, which is heavily used by employees (APT28 used this channel for exfiltration). Second, the data exchange on web services is most likely encrypted with SSL/TLS, so attackers can download it and stay unnoticed.
Code repositories might be another channel for exfiltration. Data can be dumped through API and over HTTPS.
Scheduled Exfiltration
Data exfiltration can happen on a certain schedule to evade detection. Adversaries want to blend in with normal traffic or operate when no one is watching. Options may vary. A schedule might be predetermined or custom. Among others, here’s what patterns were observed in the wild:
- ADVSTORESHELL – every 10 minutes
- Cobalt Strike – arbitrary and random intervals
- LightNeuron – at night or business hours
- ShimRat – sleep mode upon instruction
Scheduled exfiltration might use a C2 or alternative connection. It might also use a mix of different routes to stay undetected.
Exfiltration Within the Cloud
Network traffic monitoring can potentially detect scheduled connections with the C2 server. To avoid that, attackers might try to transfer the data to a rogue account within the same address space of a cloud provider. Malicious cloud backups were observed by the researchers which then were sent through API connections.
How to Detect Data Exfiltration?
The lion’s share of patterns can be detected by collecting and analyzing SIEM logs. However, it might be difficult when it comes to network traffic. Data retention periods for DNS monitoring are not that long, and additionally, the exfiltration itself can happen within minutes. Attackers rely on the difficulty of network traffic monitoring that’s why they want to exfiltrate fast. Let’s look at some of the ways to detect exfiltration in both traffic flow and SIEM logs.
Network Traffic Flow
Some security specialists would overlook exfiltration through DNS tunneling because the nature of this channel is very noisy. Here they might want to analyze patterns of traffic in search of anomalous activity. This could be:
- Abnormal features in queries, such as unusual record types or long character strings
- Duration, frequency, and sizes of data transmitted through certain request/response channels
- Abnormal hosts and devices in new network connections
- Packet outliers that don’t belong to established flows
- Fixed-sized data packets sent at suspiciously regular intervals
- Unusual patterns in encrypted application-layer channels (such as SSL/TLS) – you can’t look at what’s inside, but you can analyze the behavior
- Suspicious usage of common and uncommon ports
DNS over HTTPS (DoH) channel encrypts the traffic for privacy, which is often abused by attackers. If detecting the probability of DoH tunneling is crucial for the organization’s safety, consider studying the latest scientific research findings. For instance, it’s possible to analyze TLS fingerprints of DoH clients and build classifiers with flow-based features, which is demonstrated experimentally.
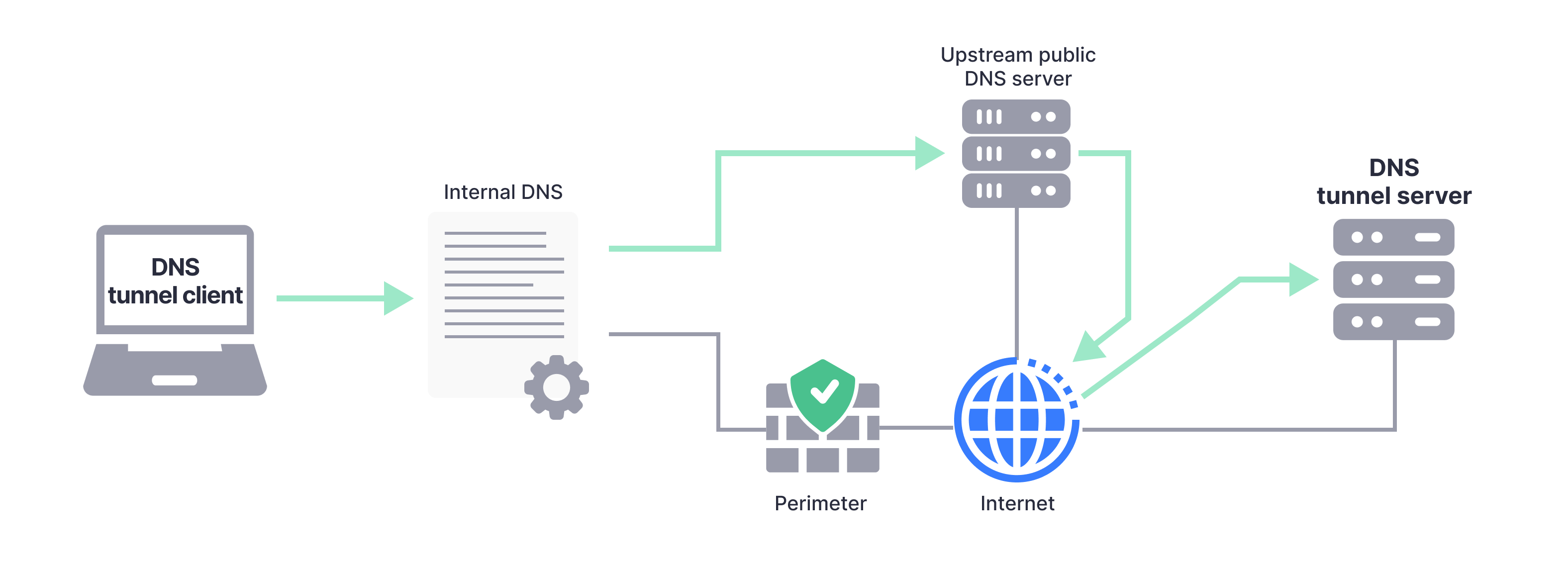
Image idea: Al-kasassbeh Mouhammd, & Khairallah, T. (2019). Winning tactics with DNS tunneling. Network Security, 2019(12), 12–19. doi:10.1016/s1353-4858(19)30144-8
Snort rules for IDS also help detect DNS tunneling. Research shows that the following rules generate accurate alerts:
- The rule which counts the frequency of DNS requests within five seconds
- The rule based on specific byte content, which can be found in packet flows
- The rule targeting the IP packet encapsulated in the DNS response (looking for the IP header starting with 0x4510 based on the discovered port number and destination of a tunneled packet)
The traffic for this experiment was captured via an SSH connection. The analysts exported packet bytes through Wireshark into a binary file and examined its contents.
Logs
Naturally, the process of exfiltration can be initiated from earlier stages in a kill chain. Like, for example, from an executable file placed in a strange location or a PowerShell script. The data can also be previously collected and packed to be exfiltrated later. Files can be shared or copied. And since there might be millions of such events happening on the network daily, it’s pretty hard to notice suspicious behavior early in an attack lifecycle.
Monitoring the possible exfiltration of data in bulk is possible by using special automation tools for SIEM. For instance, there are a bunch of extensions in IBM QRadar and a Microsoft Sentinel playbook from SOC Prime for the isolation of worms in AWS EC2 instances that attempt to exfiltrate data.
Some other detection tips from MITRE ATT&CK include:
- Checking files, especially ones with suspicious extensions and in unusual locations, that attempt to initiate a connection via network protocols
- Checking mount points to storage devices and newly assigned drive letters
- Monitoring access and new process creations for removable media
- Monitoring local network metadata (such as MAC addressing) and network management protocols (such as DHCP) for unusual hardware connections
Finally, let’s not forget that different attackers might use exactly the same malware sample across different victims. That’s why Indicators of Compromise (IOC) are also worth considering. Like in the case of HYPERSCRAPE, described by Google Threat Analysis Group (TAG) – this malware shows quite a complex behavior, but the files that it uses are pretty much detectable.
How to Prevent Data Exfiltration?
Security teams work hard to provide multiple levels of data protection like encryption, VPN and proxy, secrets rotation, and more. Unfortunately, attackers can abuse precisely those controls by exfiltrating data through secure connections. So, how to achieve the best prevention of data exfiltration?
Data Loss Prevention (DLP)
DLP is a complex strategic approach to preventing data leakage, destruction, and unauthorized use. It can include multiple pieces of technology, specific processes, and security personnel involvement.
It usually starts with creating risk management policies. Data classification and governing principles, retention requirements, business continuity plans, disaster recovery – all the boring but essential documentation is crafted at this stage. The technology part includes hardware, firmware, and software, from repeaters and all the way to SIEM. It’s good to know that some software vendors like Microsoft already offer DLP as a native set of features. And finally, security is impossible (yet) without human supervision, so qualified professionals and regular training will help to maintain the DLP strategy. To extend it beyond the limitations of an in-house team, organizations leverage collaborative cyber defense. Check out the benefits of our Threat Bounty program to see how independent Security Researchers monetize their professional experience.
Identity & Access Management
To exfiltrate data, attackers want to make unauthorized changes. Although quite often, it’s easier for them to hijack legitimate users’ sessions and accounts and act from there. While there are many ways to impersonate insiders, the management of access can be handled with the help of a few conceptually simple methods.
It’s all about the traditional stuff: least privilege, need-to-know, separation of duties. All those are useful because it’s easier to establish baselines of legitimate user behavior. Security experts also say that separation of duties requires collusion. It’s not like administrators want people to collude, but it’s a smart move. Let’s say a chain of actions like reading a sensitive file AND communicating via outbound connection is impossible to do within the scope of one account. This prompts a rogue user to collude and leave tracks. Such actions would be easier to detect.
Technology-wise authorization controls like Kerberos tickets, Amazon IAM, etc., have been showing a bunch of flaws in the wild that were happily exploited by adversaries. In this case, a SOC team might face difficult questions like whether they should continue using this security control or not. Truth be told, it’s impossible to fully eliminate risks, so it’s often a matter of securing the infrastructure with the best technology that’s available and then continuously monitoring the situation. Plus, things like hybrid encryption and multi-factor authentication should be implemented anyway, “just in case.”
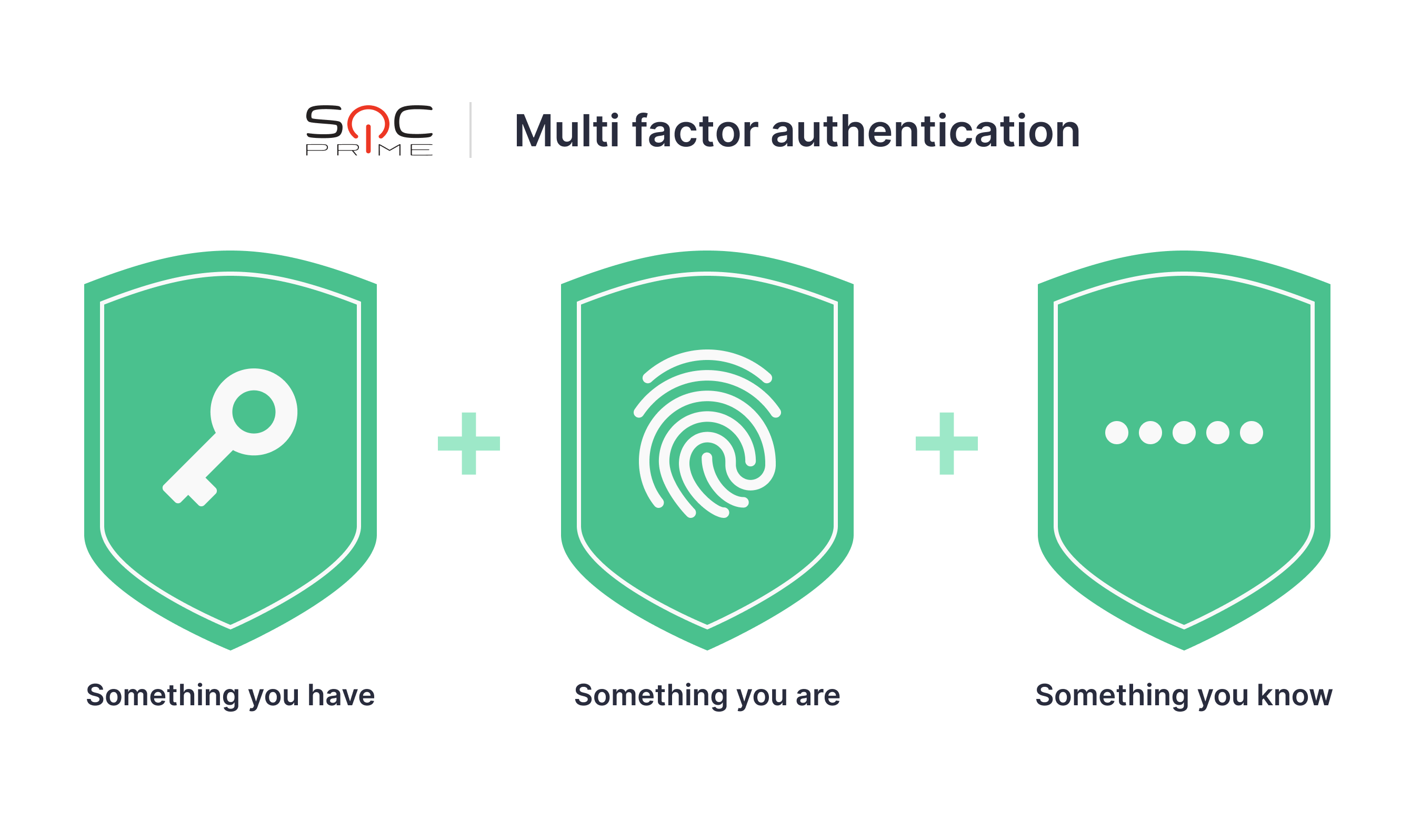
Image idea: Shutterstock
Software-Defined Networking (SDN)
Security devices for monitoring and filtering network traffic help prevent exfiltration, and many vendors do an excellent job in manufacturing those. But if the SOC team buys these devices, are they bound to vendor lock-in? Are they limited by the availability of patches? Is it only as good as it gets, and there’s a complete dependency on a particular version?
Turns out, there’s a way to avoid undesired dependencies. SDN employs software-based controllers and APIs for managing different security levels, gaining visibility and granular control of traffic, files, applications, and assets. However, since the control plane is software-based, it’s fair to suggest that it requires a great deal of security monitoring for itself, too.
Microsegmentation
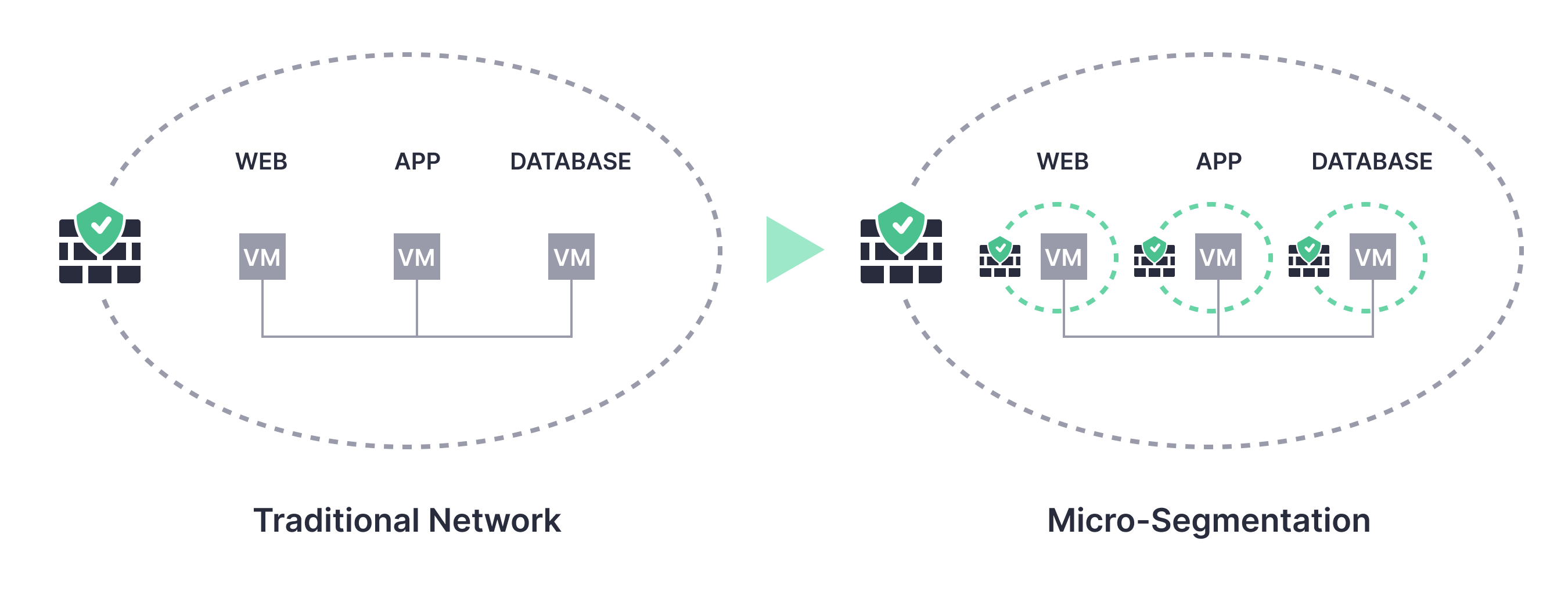
Image idea: Vembu
One of the practical ways of achieving things like least privilege and zero trust is microsegmentation. As the name suggests, this approach requires dividing networks into smaller segments (often defined by workloads) and securing each one separately. This allows configuring multiple access control lists (ACL) and isolating assets, thus reducing the attack surface. Needless to say, a single monolithic structure of a network is a recipe for disaster, so microsegmentation could be a viable solution. Additionally, it might be reasonable to implement defense-in-depth when security layers enforce restrictions in series and not in parallel.
The “Art of War” author Sun Tzu once said: “when we are near, we must make the enemy believe we are far away.” Perhaps, he was the master of what is now called data hiding. Put simply, it should be extremely difficult to discover the placement as well as even the fact of the existence of highly confidential data on a certain network.
When all the preventive measures are in place, streamline your threat detection routine by leveraging a collaborative cyber defense approach. Discover SOC Prime’s Cyber Threats Search Engine for an instant search of more than 236 Sigma detections for the Exfiltration tactic. Translations to 26+ formats make these rules applicable across a multitude of vendor-specific solutions for log management and monitoring. Get 41 rules for free and full coverage starting from $5,500 with an On-Demand subscription plan.