On July 27, 2022, Microsoft cybersecurity researchers published a notice observing the recently revealed malicious activity of the European private-sector offensive actor (PSOA) tracked as KNOTWEED, which leverages a set of Windows and Adobe zero-day exploits, including the newly patched CVE-2022-22047 vulnerability. According to the research, threat actors launch targeted cyber-attacks against organizations in Europe and Central America leveraging novel Subzero malware specifically crafted for their malicious operations.
Detect KNOTWEED Malware and Related Activity, Including Targeted Cyber-Attacks Using Vulnerability Exploitation of CVE-2022-22047
Cybersecurity professionals looking for ways to proactively defend against the adversary activity of the KNOTWEED threat actors and KNOTWEED malware samples used in their targeted malicious campaigns, are welcome to gain from SOC Prime’s platform offering a batch of dedicated Sigma rules. All behavior-based detection rules and hunting queries are available by the link below for registered SOC Prime users:
Behavior-based Sigma rules to detect the malicious KNOTWEED activity and related malware
These detection algorithms are convertible to industry-leading SIEM, EDR, and XDR formats and are aligned with the MITRE ATT&CK® framework to enable enhanced cybersecurity effectiveness. For streamlined detection content search, the above-mentioned Sigma rules are available by the corresponding tag “KNOTWEED” based on the attributed adversary activity.
Above-referenced Sigma rules can help cyber defenders identify behavior-based detection patterns:
- Associated with the malware used in targeted campaigns that are launched by the related hacking collective
- Linked to the malicious activity of the KNOTWEED threat actors
Additionally, security practitioners can instantly search for threats related to the KNOTWEED adversary activity using the verified hunting content with SOC Prime’s Quick Hunt module.
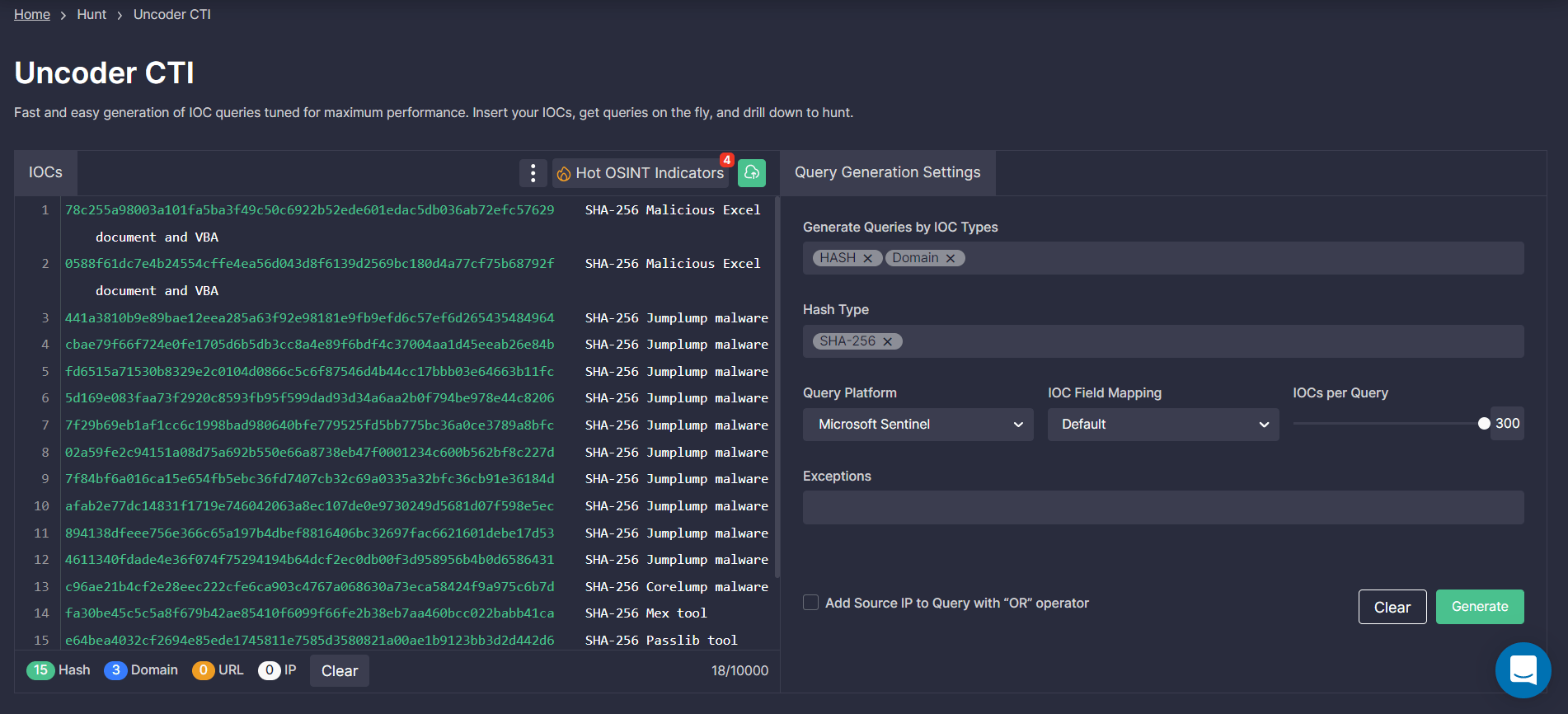
Also, SOC Prime’s Detection as Code platform enables Threat Hunters and Cyber Threat Intelligence specialists to generate custom IOC queries using Uncoder.CTI. Leveraging this SOC Prime module, it takes just a couple of clicks to generate an IOC query customized to your environment needs and ready to run in the selected SIEM or XDR instance. By following the link below, registered SOC Prime users can drill down to the entire list of indicators of compromise related to the KNOTWEED adversary activity to identify their presence in the organization’s environment and timely spot the potential traces of intrusion:
According to the annual SOC Prime’s Detection as Code Innovation report, Proactive Detection of Vulnerability Exploitation ranks as one of the top content priorities in 2021 and continues to hold the leading position in 2022 due to an increasing number of related threats and a dramatic increase in zero-day exploits. To keep abreast of emerging threats and effectively defend against zero-day attacks, obtain a comprehensive list of Sigma rules for proactive detection of zero-day exploits by clicking the Detect & Hunt button below. In addition, security experts can gain insights into the comprehensive threat context related to the KNOTWEED malicious activity by browsing SOC Prime’s cyber threats search engine and instantly reaching MITRE ATT&CK and CTI references, CVE descriptions, and more relevant metadata.
Detect & Hunt Explore Threat Context
Who is KNOTWEED? Analysis of Cyber-Attacks Exploiting CVE-2022-22047 and Other Zero-Days Attributed to This Group
The research published by Microsoft detailed the inner workings of KNOTWEED, connecting the hacking collective to DSIRF. This Austria-located business has established the facade of legitimacy by offering information research and forensics services to global organizations. However, the evidence suggests that the company also functions as a cyber mercenary group, targeting organizations in the UK, Austria, and Panama. Microsoft cybersecurity researchers revealed that DSIRF is linked to developing and distributing the Subzero malware toolset.
The newly uncovered PSOA employs two business models: access-as-a-service and hack-for-hire. KNOTWEED threat actors distribute the Subzero malware to third parties with no further engagement in malicious operations but also launch targeted cyber-attacks themselves. Threat actors have been running offensive cyber campaigns since at least 2021, actively leveraging Windows and Adobe zero-day exploits to launch spyware attacks targeting multiple industry sectors.
According to the investigation, the Subzero payload is sophisticated malware with a wide array of advanced capabilities. Its feature set involves data exfiltration, keystroke logging, screenshot capture, and a vast array of C2 capabilities.
Apart from using a zero-day Windows flaw (CVE-2022-22047) for privilege escalation, KNOTWEED exploits in 2021 included leveraging security vulnerabilities assigned CVE-2021-31199, CVE-2021-31201, CVE-2021-28550, and CVE-2021-36948.
MITRE ATT&CK® Context
To explore the MITRE ATT&CK context behind the KNOTWEED adversary activity and gain insights into the related behavior patterns, all dedicated Sigma rules are mapped to ATT&CK addressing the corresponding tactics and techniques illustrated below:
Tactics | Techniques | Sigma Rule |
Execution | Command and Scripting Interpreter (T1059) | |
Credential Access | OS Credential Dumping (T1003) | |
Modify Authentication Process (T1556) | ||
Persistence | Event Triggered Execution (T1546) | |
Join SOC Prime’s Detection as Code platform to accelerate threat detection capabilities and boost hunting velocity with near real-time access to the world’s largest collection of curated Sigma rules tailored to 25+ SIEM, EDR, and XDR solutions. Aspiring Detection Engineers and Threat Hunters can gain an opportunity for self-advancement by joining Threat Bounty Program and collaborating with brilliant cybersecurity minds to future-proof cyber defense. Write high-quality detection content, share it with industry peers, and receive recurring financial rewards for your contribution.




