Stay alert! Adversaries set eyes on Aspena Faspex, an IBM file-exchange application frequently used by large enterprises to speed up file transfer procedures. Specifically, threat actors attempt to leverage a pre-authenticated remote code execution (RCE) vulnerability (CVE-2022-47986) affecting the app to proceed with ransomware attacks. At least two ransomware collectives were spotted exploiting CVE-2022-47986, including IceFire and Buhti.
CVE-2022-47986 Detection
Throughout 2021-2023, ransomware continues to be one of the dominant trends in the cyber threat landscape, illustrated by the increasing sophistication of intrusions and a rapidly growing number of ransomware affiliates. To secure organizational infrastructure from emerging ransomware threats, cyber defenders require a reliable source of detection content helping to spot potential attacks on time. Explore curated Sigma rules from the SOC Prime Platform below to identify CVE-2022-47986 exploitation attempts:
Possible IBM Aspera CVE-2022-47986 Exploitation Attempt (via webserver)
This Sigma-based threat-hunting query can be leveraged across 16 SIEM, EDR, and XDR solutions and is benchmarked against the MITRE ATT&CK framework v12 addressing the Initial Access tactic with the corresponding Exploit Public-Facing Application (T1190) technique.
Possible IBM Aspera CVE-2022-47986 Exploitation Attempt (via keywords)
The above-referenced query is compatible with 16 SIEM, EDR, and XDR technologies, also addressing the Initial Access tactic with the corresponding Exploit Public-Facing Application (T1190) technique.
By clicking the Explore Detections button, organizations can gain instant access to even more detection algorithms aimed to help identify the malicious behavior linked to the exploitation of trending vulnerabilities. For streamlined threat investigation, teams can also drill down to relevant metadata, including ATT&CK and CTI references.
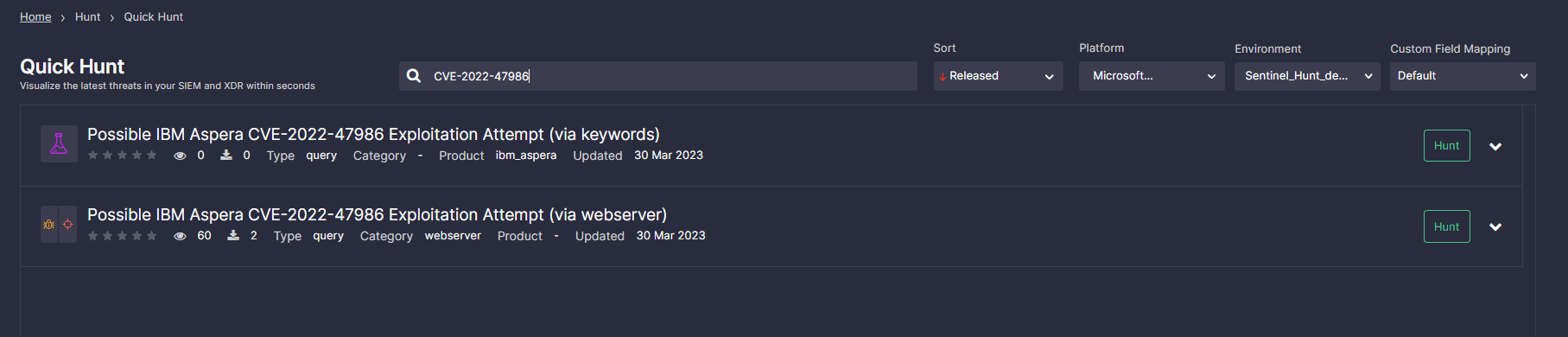
To make the most of SOC Prime’s Quick Hunt module and search for threats related to the CVE-2022-47986, apply the custom tag “CVE-2022-47986” and filter the list of verified queries based on your current needs. Then select your platform and environment, and instantly drill down to hunt, shaving seconds off your threat investigation.
CVE-2022-47986 Analysis
In early winter 2023, IBM released an advisory patching a set of security issues impacting the Aspera Faspex app. The most notorious one on the list is CVE-2022-47986, a pre-authentication YAML deserialization vulnerability stemming from Ruby on Rails code. The bug is rated critical, with a CVSS score of 9.8. According to IBM, affected products include Aspera Faspex 4.4.2 Patch Level 1 and below.
The PoC exploit has been circulating the web since at least February 2023, with multiple exploitation attempts reported by security vendors. For instance, Sentinel One inquiry details the IceFire ransomware campaign leveraging CVE-2022-47986 to push a new Linux version of the malicious strain. Also, security experts reported about Buhti group adding Aspera Faspex flaw exploits to the toolset. The most recent research by Rapid7 adds to the timeline of in-the-wild attacks highlighting the compromise of the unnamed vendor.
In view of the growing number and sophistication of malicious campaigns relying on CVE-2022-47986, in February 2023, CISA added the issue to its Known Exploited Vulnerabilities (KEV) catalog, based on evidence of active exploitation.
Looking for ways to stay ahead of any cyber threats and always have detection for related adversary TTPs at hand? Gain access to over 800 rules for current and emerging CVEs to timely identify the risks and strengthen your cybersecurity posture. Reach 140+ Sigma rules for free or explore the entire list of relevant detection algorithms via On Demand at https://my.socprime.com/pricing/




