Security teams are no longer short on data. They are drowning in it. Cloud control plane logs, endpoint telemetry, identity events, SaaS audit trails, application logs, and network signals keep expanding, while the SOC is still expected to deliver faster detection and cleaner investigations. That is why SIEM vs log management is not just a tooling debate. It is a telemetry strategy question about what to retain as evidence, what to analyze for real-time detection, and where to do the heavy lifting.
Observability programs accelerate the flood. More telemetry can mean better visibility, but only if the SOC can trust it, normalize it, enrich it, and query it fast enough to keep pace with active threats. At scale, the cost and operational burden show up quickly across both SIEM and log management. PwC highlights how rising data volumes and cost models can push teams to limit ingestion and create blind spots, while alert overload and performance constraints make it harder to separate real threats from noise. Speed is also unforgiving. Verizon reports the median time for users to fall for phishing is less than 60 seconds, while breach lifecycles remain measured in months.
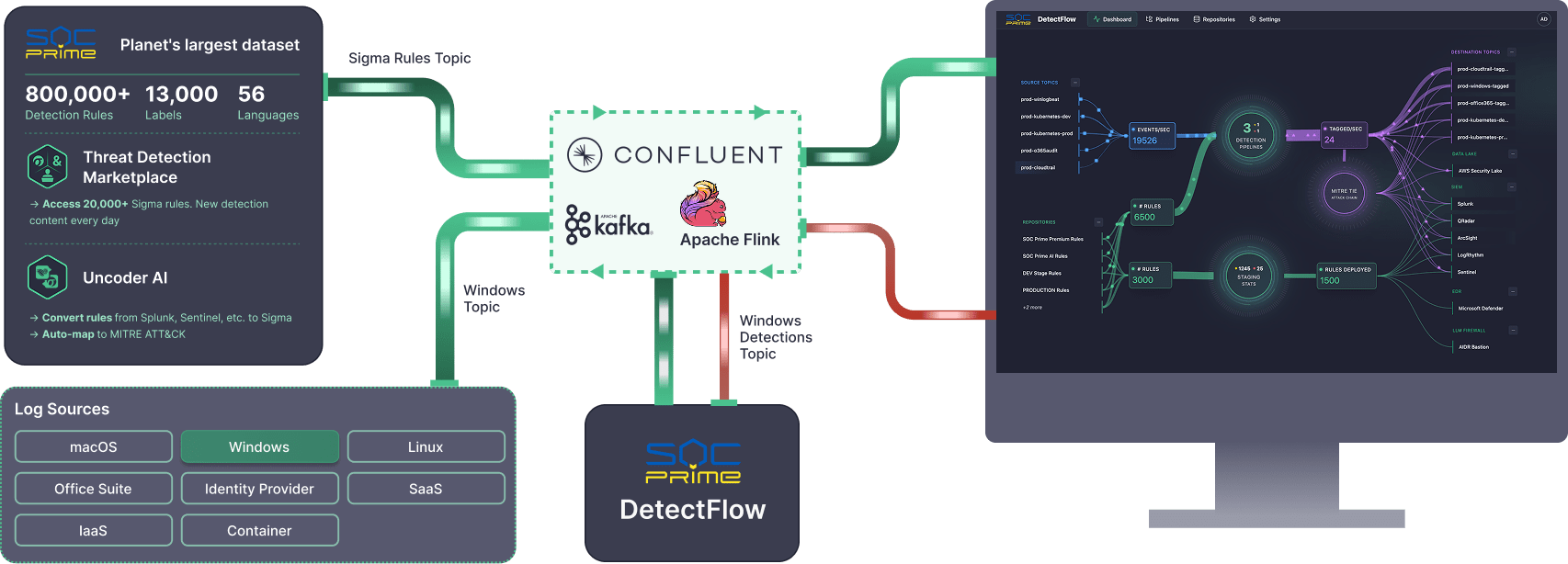
That is why many SOCs are adopting a security data pipeline mindset. It means processing telemetry before it lands in your tools, so you control what gets stored, what gets indexed, and what gets analyzed. Solutions like SOC Prime’s DetectFlow add even more value by turning a data pipeline into a detection pipeline through in-flight normalization and enrichment, running thousands of Sigma rules on streaming data, and supporting value-based routing. Low-signal noise can stay in lower-cost log storage for retention, search, and forensics, while only enriched, detection-tagged events flow into the SIEM for triage and response. The outcome is lower SIEM ingestion and alert noise costs without sacrificing investigation history.
SIEM vs Log Management: Definitions
Before comparing tools, it helps to align on what each category is designed to do, because overlapping feature checklists can hide fundamentally different objectives.
Gartner defines SIEM around a customer need to analyze event data in real time for early detection and to collect, store, investigate, and report on log data for detection, investigation, and incident response. In other words, SIEM is a security-focused system of record that expects heterogeneous data, correlates it, and supports security operations workflows.
Log management has a different center of gravity. NIST describes log management as the process and infrastructure for generating, transmitting, storing, analyzing, and disposing of log data, supported by planning and operational practices that keep logging consistent and reliable. In fact, log management is how you keep the raw evidence searchable and retained at scale, while SIEM is where you operationalize security analytics and response.
The practical difference shows up when you ask two questions:
- What is the unit of value? For log management, it is searchable records and operational visibility. For SIEM, it’s detection fidelity and incident context.
- Where does analytics happen? In log management, analytics often supports exploration and troubleshooting. In SIEM, analytics is built for threat detection, alerting, triage, and case management
What Is a Log Management System?
A log management system is the operational backbone for ingesting and organizing logs, so teams can search, retain, and use them to understand what happened.
Log management is often the first place teams see the economics of telemetry. Many organizations don’t need to run expensive correlation on every log line. Instead, they store more data cheaply and retrieve it quickly when an incident demands it. That’s why log management is frequently paired with data routing and filtering approaches that reduce noise before it reaches higher-cost analytics layers.
For security teams, log management becomes truly valuable when it produces high-integrity, well-structured telemetry that downstream detections can rely on, without forcing the SIEM to act as a catch-all storage sink.
What Is a SIEM?
A SIEM stands for Security Information and Event Management. It is designed to centralize security-relevant telemetry and turn it into detections, investigations, and reports. Normally, SIEM is described as supporting threat detection, compliance, and incident management through the collection and analysis of security events, both near real-time and historical, across a broad scope of log and contextual data sources.
But SIEMs face structural pressures as telemetry grows. Common pain points in traditional SIEM approaches include skyrocketing data volumes and cost, alert overload, and scalability and performance constraints when searching and correlating large datasets in real time. Those pressures matter because defenders already operate on unfavorable timelines. IBM’s Cost of a Data Breach report shows breach lifecycles still commonly span months, which makes efficient investigation and reliable telemetry critical.
So while SIEM remains central for security analytics and response, many teams now treat it as the destination for curated, detection-ready data, not the place where all telemetry must land first.
SIEM vs Log Management: Main Features
A useful way to compare SIEM and log management is to map them to the security data lifecycle: collect, transform, store, analyze, and respond. Log management does most of the work in collect through store, with fast search to support investigations. SIEM concentrates on analyzing through response, where correlation, enrichment, alerting, and case management are expected to work under pressure.
Log management features typically cluster around collect, transform, store, and search:
- Ingestion at scale: agents, syslog, API pulls, cloud-native integrations
- Parsing and field extraction: schema mapping, pipeline transforms, enrichment for searchability
- Retention and storage controls: tiering, compression, cost governance, access policies
- Search and exploration: fast queries for troubleshooting and forensic hunting
SIEM features concentrate on analyzing and responding:
- Security analytics and correlation: rules, detections, behavioral patterns, cross-source joins
- Context and enrichment: identity, asset inventory, threat intel, entity resolution
- Alert management: triage workflows, suppression, prioritization, reporting
- Case management: investigations, evidence tracking, compliance reporting
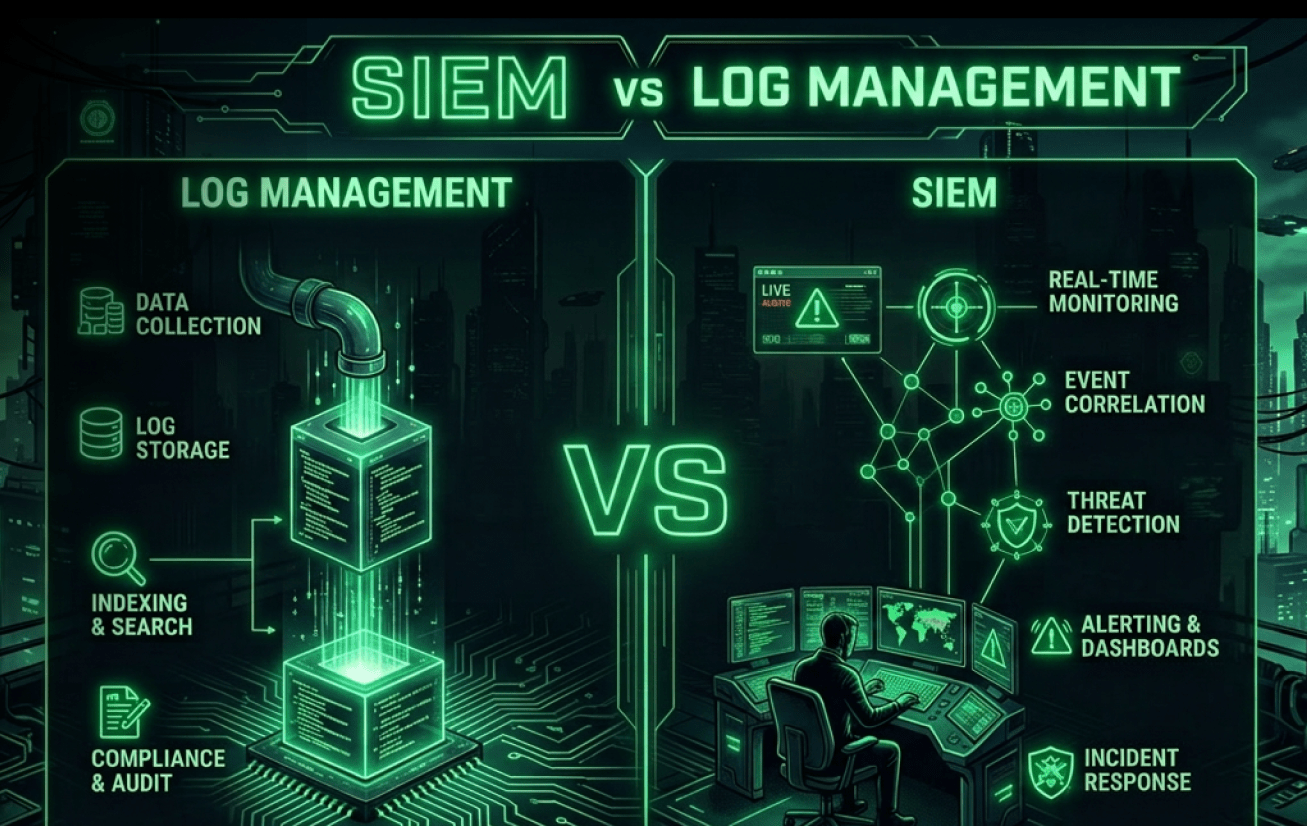
In other words, log management optimizes for retention and retrieval, and SIEM optimizes for detection and action. Yet, traditional SIEM approaches strain when the platform becomes both the telemetry lake and the correlation engine, especially under rising ingestion costs and alert noise. That is why many teams treat log management as the evidence layer, SIEM as the decision layer, and a pipeline layer as the control plane that shapes what flows into each.
Benefits of Using Log Management and SIEMs
Log management and SIEM are most effective when they’re treated as complementary layers in a single security data strategy.
Log management delivers depth and durability. It helps teams retain more raw evidence, troubleshoot operational issues that look like security incidents, and preserve the grounds needed for later forensics. This becomes essential when threat hypotheses emerge after the fact (for example, learning a new indicator days later and needing to search back in time).
SIEM delivers security outcomes: detection, prioritization, and incident workflows. A well-tuned SIEM program can reduce “needle-in-a-haystack” work by correlating events across identities, endpoints, networks, and cloud control planes.
The best security programs get three benefits from combining both:
- Cost control: store more, analyze less expensively by default, and route high-value data to SIEM.
- Better investigations: keep deep history in log platforms while SIEM tracks detections and cases.
- Higher signal quality: normalize and enrich logs so detections fire on consistent fields rather than brittle strings.
How SOC Prime Can Improve the Work of SIEM & Log Management
SOC Prime brings the SIEM and log management story together as a single end-to-end workflow.
You start with Attack Detective to audit your SOC and map gaps to MITRE ATT&CK, so you know which telemetry and techniques you are missing. Then, Threat Detection Marketplace becomes the sourcing layer where you pull context-enriched detections aligned to those gaps and the latest TTPs. Uncoder AI acts as a detection-engineering booster, making the content operational and portable to any native formats your SIEM, EDR, or Data Lake actually runs, while also helping refine and optimize the logic so it performs at scale.
DetectFlow is the final layer that turns a data pipeline into a detection pipeline and enables full detection orchestration. Running tens of thousands of Sigma rules on live Kafka streams with sub-second MTTD using Apache Flink, DetectFlow tags and enriches events in flight before they reach your security stack and routes outcomes by value. This removes the need for SIEM min-maxing around rule limits and performance tradeoffs, because detection scale shifts to the stream layer, where it grows with your infrastructure, not vendor caps. For SIEM, it delivers cleaner, enriched, detection-tagged signals for triage and response. For log management, it preserves deep retention while making searches and investigations faster through normalized fields and attached detection context.