Here at SOC Prime, we are constantly working to provide our customers with maximum value and a smooth experience while using Threat Detection Marketplace. To mark major milestones on the way, starting from February 2021, we launch a set of regular blog posts covering key improvements to our CaaS platform.
The latest Threat Detection Marketplace release from February 9, 2021 includes major translation updates, introduces pop-ups for user feedback collection, and provides improvements to our Help Center guides.
Translation Updates
Alternative Translations for Azure Sentinel
In February 2021, the SOC Prime team added support for Azure Sentinel alternative translations. You can now apply either the original translation format or the Microsoft Defender APT format. To get the Microsoft Defender ATP translations, select mdatp from the Config drop-down list right from the rule page.
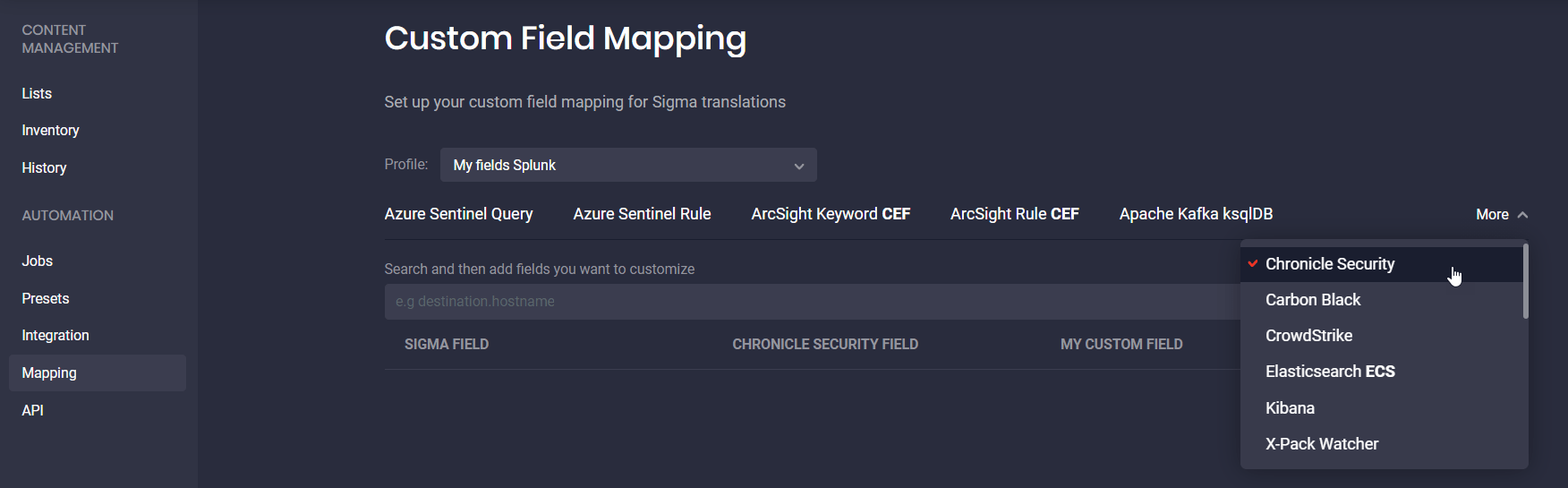
Improved Google Chronicle Security Translations
This month we’ve added updates to Google Chronicle Security translations, so you can implement Custom Field Mapping for streamlined Sigma translations in YARA-L language format. To apply the new feature, you can select Chronicle Security from More drop-down list.
To enhance the threat detection experience, we’ve also fixed the mapping issues, improved the field name display after translation, and mastered the rule structure. Additionally, we’ve moved all the information from the logsource field in the original Sigma rule code to the meta field when converting this rule to the YARA-L format, fulfilling our client’s translation enhancement request.
Platform Enhancements
Apart from adding new elements and upgrades to the Threat Detection Marketplace, the SOC Prime team is continuously working on the existing platform features.
Sigmac Upgrade
February 2021 release covers the improvements to the current sigmac version. We’ve made updates on our end and synced it with the Sigma repository on GitHub owned by Florian Roth. All the changes between the Sigma repo on GitHub and our repository on GitLab are reflected in our log file.
Gathering Feedback for Future Improvements
At SOC Prime, we are continuously looking for new ways to provide the best ever experience while using the Threat Detection Marketplace platform. With this release, we’ve added two pop-ups that encourage security performers to take a survey, which collects user feedback on the platform’s functionality.
We appreciate your time and provide rewards for your valuable input. Depending on the current subscription, you might choose among the following benefits:
- For Community users — ability to unlock two exclusive rules developed by the SOC Prime Team
- For Premium subscription users:
- Free trial access to the CCM module for 30 days
- Workshop “Ideas for detections, from hypothesis to hunt” hosted by our SOC Prime experts
- A deep-dive workshop introducing threat hunting best practices
- One-hour webinar addressing the organization’s business-specific security needs
We would summarize the feedback and fulfill your requests in the upcoming Threat Detection Marketplace releases.
Help Center Guides
To ensure a quick and easy start with Threat Detection Marketplace as well as to provide updates on the most recent platform changes, we regularly publish and enrich our Help Center guides. The latest Threat Detection Marketplace release includes updates to the following guides:
- Continuous Content Management Guide
- Content Guides
- Platform Guide
Sign-up to the Threat Detection Marketplace, an industry-first content-as-a-service (CaaS) platform that helps to reduce the burden on your SecOps team by streaming cross-platform detections directly to the SIEM, EDR, NSM, and SOAR tool of your choice. To unfold the maximum potential of Threat Detection Marketplace for your organization, you might check for the appropriate subscription type and contact SOC Prime experts for further clarifications. Have a desire to contribute to threat hunting activities and craft your own curated SOC content? Join our Threat Bounty program!