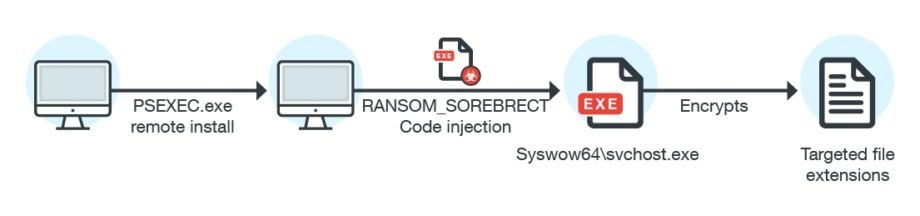
London, UK – July 4, 2017 – Researchers from Trend Micro reported a new threat created to attack large enterprises. Sorebrect is a fileless Ransomware that injects malicious code into svchost.exe process. This virus gets delivered into a system through the malicious use of the PsExec utility, which allows system administrators to run files or execute commands on remote computers. To do this, attackers need administrator credentials. Probably, they receive the necessary data with the bruteforce attack on target computers. Sorebrect uses the Tor network to hide communications with command server and is able to encrypt not only files on local computer, but also all files on network shares. After that, the virus deletes the system’s event logs using wevtutil.exe. Because of Sorebrect removes traces of its presence after malicious code injection, it is almost impossible to detect this threat by security solutions.
There are several SIEM use cases in the S.M.A. Cloud for ArcSight, QRadar and Splunk that will help your SIEM detect such viruses at different stages of the attack. Ransomware Hunter and APT Framework will notify you of the threat, using methods of statistical profiling and behavioral analysis. DetectTor will warn about hidden communications in C2 phase, and Brute Force Detection use case will detect any attempts of password guessing to accounts.

