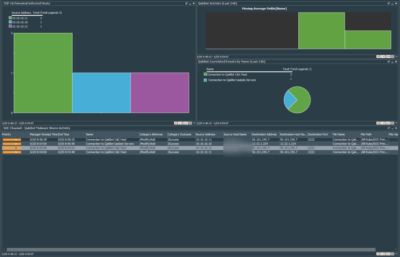
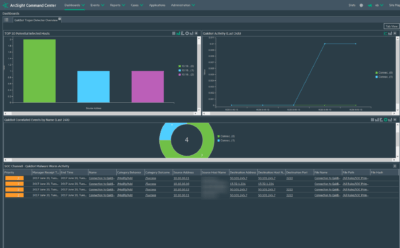
London, UK – June 20, 2017 – Our team created a threat-centric turn-key SIEM use case for QakBot / Pinkslipbot Trojan detection. It is one of SOC Prime’s free use cases targeted at immediately uncovering the most recent threats, such as Industroyer, EternalRocks or WannaCry. You can download QakBot Trojan Detector after logging or registering in the S.M.A. Cloud. Installation will take only a few minutes, and then your SIEM tool will be able to alert you while it detects the QakBot Trojan activity. For now, this use case is available only for HPE ArcSight. To accelerate development of Use Cases for IBM QRadar and Splunk, please vote for Use Case you need in the S.M.A. Cloud.
We recently wrote about the extreme danger of a new QakBot Trojan modification. Since then, researchers from McAfee Labs have found that this virus exploits infected devices even after it is removed by a security product. QakBot currently controls a botnet from more than 500,000 devices, and this number continues to grow. The virus uses infected devices as HTTPS-based proxies to hide its real control servers. Malware creates port-forwarding rules, leaving your computer vulnerable to attacks from the Internet due to open ports.