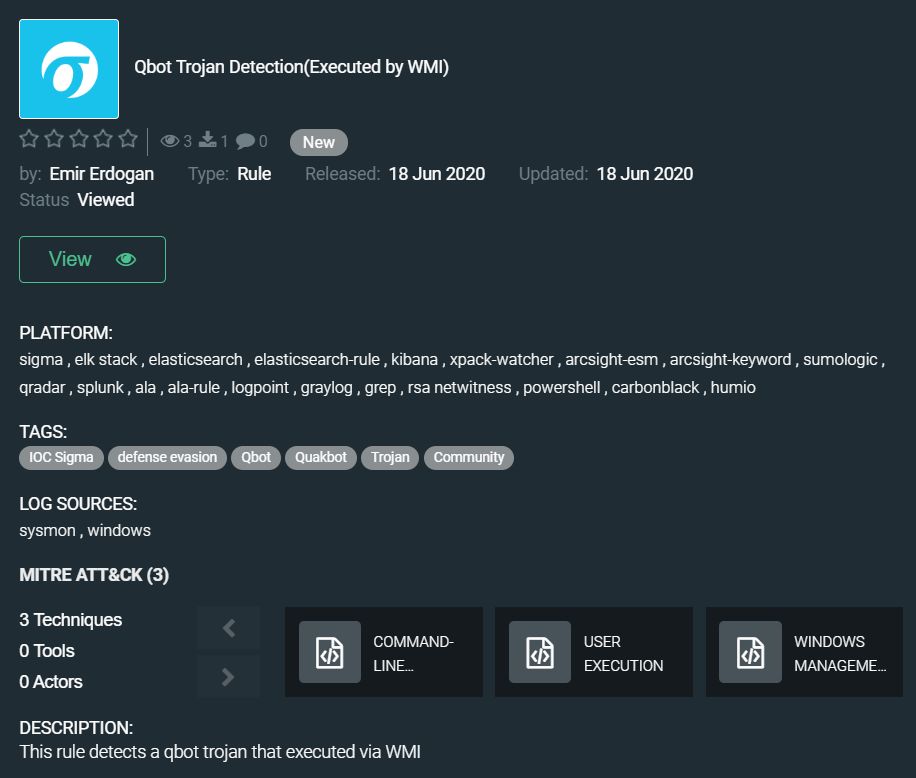
And again, we want to highlight the content for detecting QBot malware in the Rule of the Week section. About a month ago, a simple but effective rule from Emir Erdogan was already published in this section. But the twelve-year-old Trojan continues to evolve, and just a couple of days ago, fresh samples of this malware were discovered, based on which Emir created a new Threat Hunting rule that tracks changes in QBot behavior: https://tdm.socprime.com/tdm/info/8DYw876BPWAL/NFgIx3IBQAH5UgbBHY87/?p=1
The evolution of malware does not affect its basic functions, it still collects browsing activity, steals bank account credentials and other financial information. Adversaries use phishing techniques to lure victims to websites that use exploits to inject Qbot via a dropper. It does this through a combination of techniques that subvert the victim’s web sessions, including keylogging, credential theft, cookie exfiltration, and process hooking. Qbot’s latest version adds both detection and research-evasion techniques. It has a new packing layer that scrambles and hides the code from scanners and signature-based tools. It also includes anti-virtual machine techniques, which helps it resist forensic examination.
The rule has translations for the following platforms:
SIEM: Azure Sentinel, ArcSight, QRadar, Splunk, Graylog, ELK Stack, RSA NetWitness, LogPoint, Humio
EDR: Carbon Black, Elastic Endpoint
MITRE ATT&CK:
Tactics: Execution
Techniques: Command-Line Interface (T1059), User Execution (T1204), Windows Management Instrumentation (T1047)