Phobos Ransomware represents the relatively new ransomware family based on Dharma (CrySis) that has been notorious since 2016. The first traces of Phobos were spotted less than two years ago, at the turn of 2019. SOC Prime Threat Detection Marketplace, the world’s largest platform for SOC content, offers Phobos ransomware detection scenarios among its library of 85,000+ content items. The EKING variant of Phobos ransomware recently emerged in October 2020 and was applied in attacks targeted at government organizations. The EKING is a file-encoding malware targeted at encrypting crucial data stored on the compromised device and deleting backup copies. Decrypting infected data poses a daunting challenge to organizations, since only the EKING developers possess valid encryption tools, for which they demand ransom.
What is Phobos Ransomware?
Malware belonging to the Phobos Ransomware family spread via hacked RDP connections. Phobos is typically distributed by compromising RDP servers, infiltrating an organization’s network, and infecting as many systems as possible to obtain a large ransom for decrypting compromised data. However, many victims who paid significant amounts of money to cybercriminals for decryption never received it.
Perhaps this is one of the reasons why EKING was in the spotlight in October 2020. There are several confirmed cases that adversaries spread EKING by means of phishing emails. This Phobos ransomware variation appeared in the form of the MS Word document with a malicious Macro code intended to spread EKING across the organizations’ networks.
How Does Phobos Ransomware Get Into Your Computer?
A fresh analysis of EKING from FortiGuard Labs reveals how a malicious binary enters the system after a victim opens a MS Word document attached to a phishing email. The ransomware not only encrypts files on the infected machine, but it also targets new attached logical drives and network sharing resources. To accelerate the encryption process, EKING creates two scan threads for each logical drive: one of them finds and encrypts files related to databases. The malware renames files and then generates ransom messages. These messages prompt compromised users to get in touch with the adversaries and expect their further instructions.
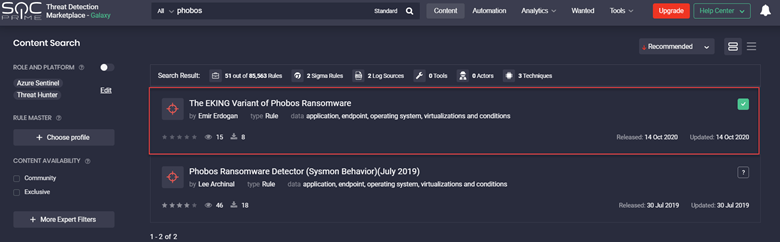
Phobos Ransomware Detection Content
One of the most active contributors to the Threat Detection Marketplace content library and developer of the Threat Bounty Program, Emir Erdogan, has recently released a new Community Sigma rule to help organizations protect against EKING ransomware attacks:
The rule has translations for the following SIEM, EDR, and other security tools:
- SIEMs: Azure Sentinel, Sumo Logic, Humio, Elastic Stack, ArcSight, QRadar, Splunk, Graylog, RSA NetWitness, LogPoint
- EDRs: Carbon Black
- Chronicle Security
- Apache Kafka ksqIDB
- Microsoft PowerShell
- Regex Grep
Support for other SIEM, EDR, and NTDR technologies is coming up soon.
The published rule is also mapped to the MITRE ATT&CK® framework and addresses the following ATT&CK Tactics and Techniques:
- Tactics: Impact, Execution
- Techniques: Data Encrypted for Impact (T1486), User Execution (1204)
Ready to strengthen your cyber defense with Threat Detection Marketplace? Sign up for free. Or join Threat Bounty Program to build your own SOC content and share it across the entire Threat Detection Marketplace community.