It’s no secret that phishing attacks are one of the most effective ways to infect the target with malware. Typically, adversaries expect to convince a user to open a malicious document and enable macros or use vulnerabilities in MS Office for deploy malware. We regularly publish rules (1, 2, 3) for detecting phishing campaigns or malware that they distribute. And today we want to show you content that can detect an attack at the moment when the deceived user clicks on the Enable Editing button: https://tdm.socprime.com/tdm/info/uNiMpOIzBWK2/sIQ4znIBPeJ4_8xcPjty/?p=1#
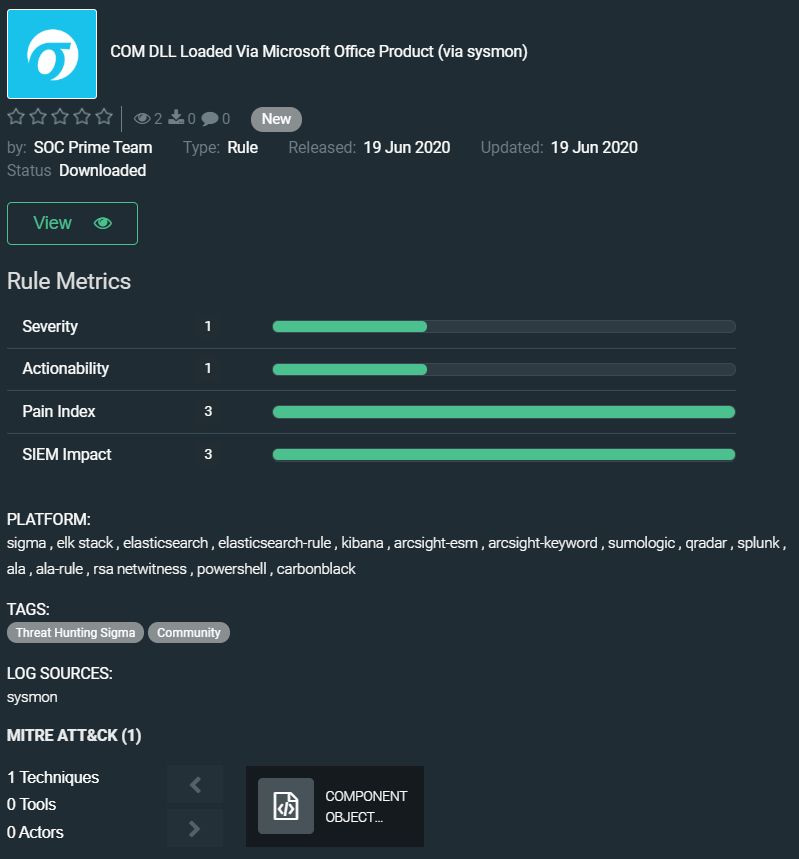
SOC Prime Team’s new rule enables the detection of COM DLLs loaded via MS Office products. This will allow you to identify a part of the attacks on the organization in which attackers misuse COM DLLs to drop malware. They can be misused by a script that uses COM to generated an Excel Macro to load Shellcode via JScript (to detect such attacks you need sysmon logs).
The rule has translations for the following platforms:
SIEM: Azure Sentinel, ArcSight, QRadar, Splunk, ELK Stack, RSA NetWitness, Sumo Logic
EDR: Carbon Black, Elastic Endpoint
MITRE ATT&CK:
Tactics: Lateral Movement, Execution
Techniques: Component Object Model and Distributed COM (T1175)