How It Works
Uncoder AI reads a Sigma rule designed to detect DNS queries to malicious infrastructure used by Katz Stealer malware, and instantly translates it into native Palo Alto Cortex XSIAM syntax.
Left Panel – Sigma Detection:
- Targets DNS queries to specific Katz Stealer domains (e.g.,
katz-panel.com,katzstealer.com) - Uses Sigma’s abstract detection model with:
logsourceset todnsquery|containsfor domain indicators
Tagged with MITRE ATT&CK technique T1071.004 (Command and Control over DNS)
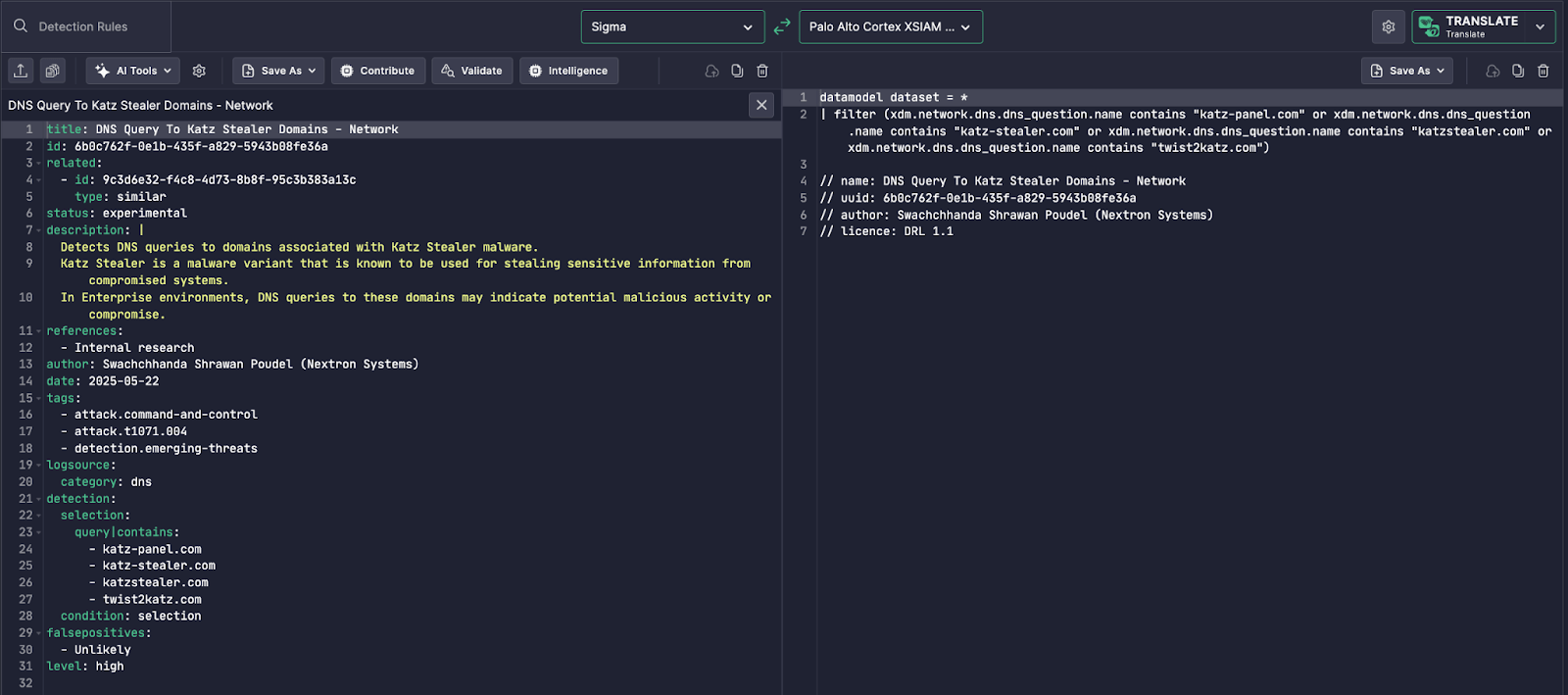
Right Panel – XSIAM Translation:
Uncoder AI produces a Cortex XSIAM-compatible rule:
filter (xdm.network.dns.dns_question.name contains "katz-panel.com" or ...)
It:
- Maps
query|containsto Cortex’sxdm.network.dns.dns_question.name - Preserves detection fidelity and context
- Adds metadata and documentation inline (name, author, license)
Why It’s Innovative
Writing detection logic for XSIAM manually can be:
- Time-consuming due to Palo Alto’s complex data model
(xdm.*) - Error-prone without full documentation of field mappings
- Inaccessible for analysts unfamiliar with Cortex XQL (XSIAM Query Language)
Uncoder AI eliminates these challenges by:
- Automating field translation from Sigma to XSIAM
- Maintaining query intent and IOC coverage
- Adding inline documentation and licensing metadata automatically
This turns platform-specific engineering into a one-click task.
Operational Value
For detection engineers and SOC teams:
- Accelerates multi-platform coverage using open Sigma content
- Reduces reliance on vendor-specific query knowledge
- Improves fidelity of DNS-based detections in Cortex XSIAM
- Operationalizes threat intel faster, e.g., for emerging malware like Katz Stealer
Uncoder AI bridges the gap between abstract detection content and the complex, structured reality of Cortex XSIAM datasets.