On April 18, 2022, CERT-UA issued an alert warning of ongoing cyber-attacks targeting Ukrainian state bodies. According to the research, government officials were exposed to targeted phishing attacks using emails related to Azovstal that contained malicious attachments spreading Cobalt Strike Beacon malware. The detected activity reflects the behavior patterns associated with the hacking collective tracked as UAC-0098 also known as TrickBot.
Phishing Cyber-Attacks Using Cobalt Strike Malware: Overview and Analysis
Over a month ago, Ukrainian government entities faced phishing attacks spreading email lures with malicious files that sequentially downloaded one another to infect the targeted system with a set of malware strains, including Cobalt Strike Beacon, the default malware payload used to create a connection to the team server and designed to model advanced attackers.
Cobalt Strike Beacon is known to have been used earlier in malware distribution campaigns, including the cyber-attacks exploiting the CVE-2018-20250 vulnerability in the WinRAR archiver. In this cyber-attack, malicious archives were delivered via spam emails and triggered the infection chain to run harmful scripts and other payloads.
In the most recent cyber-attack by the UAC-0098 threat actors, the malicious payload has been spread via phishing emails with the lure subject related to Azovstal. The targeted emails in question contained XLS attachments and malicious macros involved in the infection chain that led to delivering Cobalt Strike Beacon and compromising the victim’s computer. Based on the applied encryption techniques, the revealed activity has been attributed to the nefarious russia-affiliated malware gang TrickBot.
Sigma Behavior-Based Content to Detect Cyber-Attacks by UAC-0098 Spreading Cobalt Strike Beacon Malware
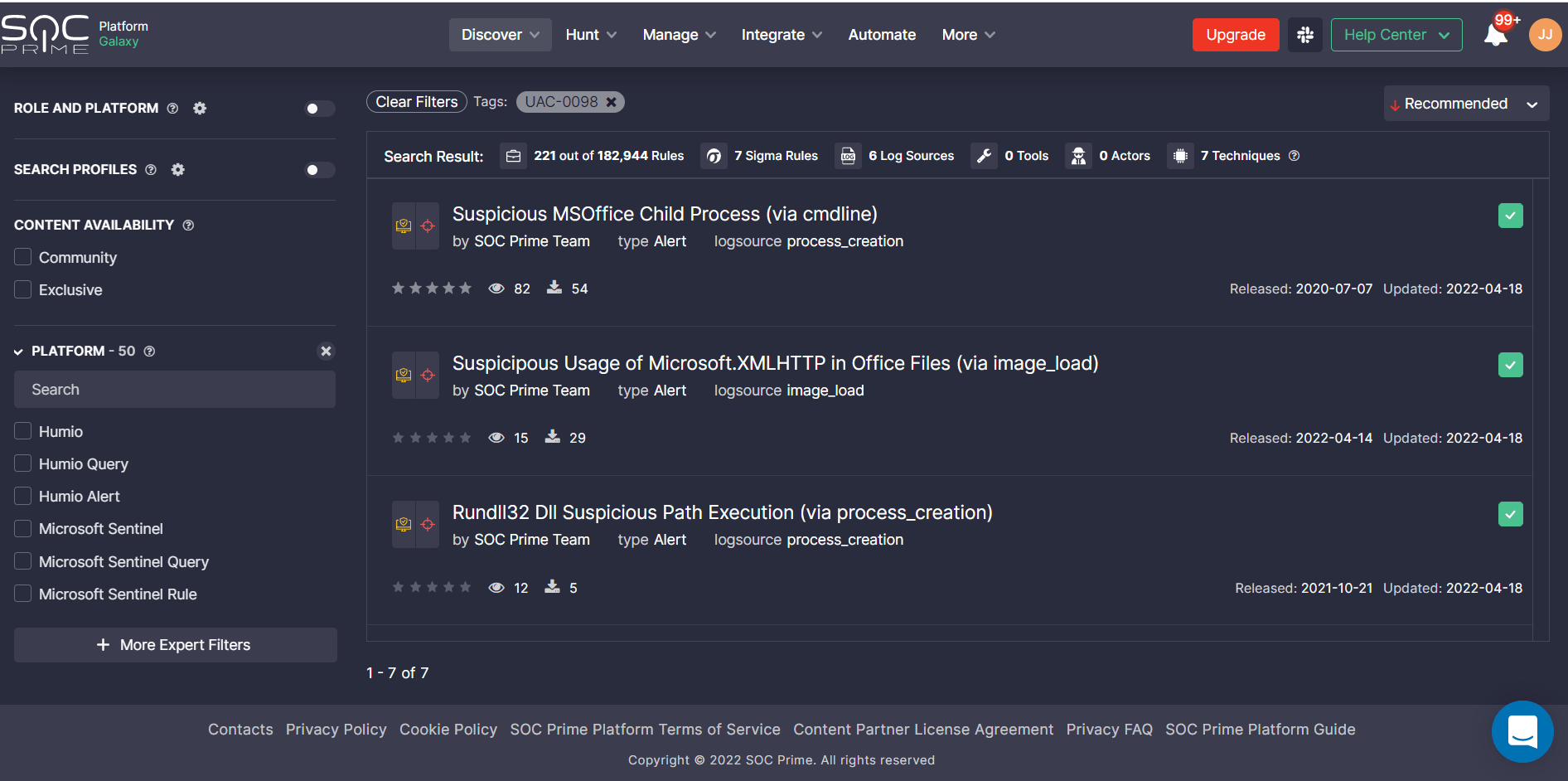
Security professionals can proactively defend against cyber-attacks involving Cobalt Strike Beacon spread by the UAC-0098 hacking group with a set of curated Sigma-based detection rules from the SOC Prime Team:
Sigma rules to detect Cobalt Strike Beacon spread by UAC-0098
The entire detection stack is tagged as #UAC-0098 for streamlined content search for related threats. Before accessing the rules, please sign up for SOC Prime’s Detection as Code platform or log in with your existing account.
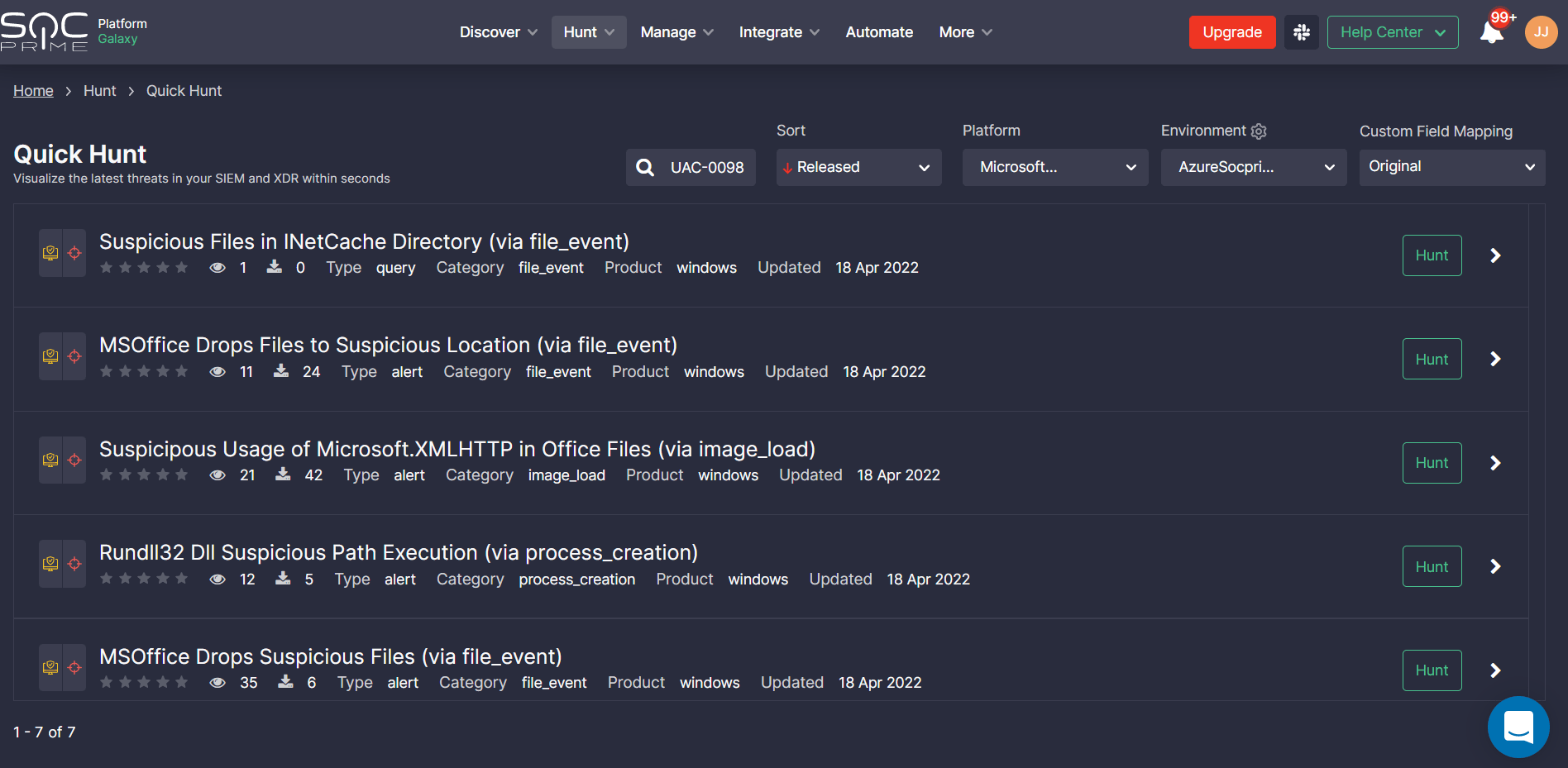
Teams can also search for threats associated with the activity of the UAC-0098 hacking group using the above-referenced hunting content with SOC Prime’s Quick Hunt module.
MITRE ATT&CK® Context
Security practitioners can dive into the context behind the latest Azovstal-related phishing attack on Ukrainian state bodies based on the MITRE ATT&CK framework. All dedicated Sigma-based content is aligned with the latest MITRE ATT&CK framework v.10 addressing the corresponding tactics and techniques:




