The infamous Russian state-sponsored hacking collective, Armageddon, recently involved in phishing attacks targeting Ukrainian and European state bodies, continues its malicious activity. Based on the latest CERT-UA investigations, Armageddon threat actors also identified as UAC-0010 have been observed in another cyber-attack against Ukraine distributing phishing emails and spreading malicious software dubbed GammaLoad.PS1_v2.
Armageddon APT Targeting Ukraine Through the Delivery of GammaLoad.PS1_v2 Malware: Attack Analysis
According to the report by the Security Service of Ukraine (SSU), Armageddon threat actors also tracked as Gamaredon (by Eset, PaloAlto researchers) or Primitive Bear (by CrowdStrike) are identified as an APT group, which has been created as a special unit of Russia’s Federal Security Service to conduct intelligence and subversive activities against Ukraine on the cyber front.
In the previous April’s attack, the cyber espionage group leveraged the GammaLoad.PS1 malware delivered via phishing emails and deployed through an infection chain using the malicious VBScript code. One month later, yet another phishing campaign by Armageddon APT targeting Ukraine applies the updated malware version identified as GammaLoad.PS1_v2.
Phishing remains the most preferred attack vector of the Russia-linked Armageddon APT group with the latest campaign being no exception. This time, the Armageddon group has also chosen their common adversary method applying the email subject and file names as phishing lures along with the malicious attachment triggering the infection chain. Based on the CERT-UA research, such phishing emails are delivered with an HTM attachment that, when opened, creates a RAR archive with a shortcut LNK file, which can potentially lead to executing and launching an HTA file. The latter generates and runs two files that finally drop GammaLoad.PS1_v2 on the targeted computer.
Sigma Rules to Detect Armageddon APT Cyber-Attacks
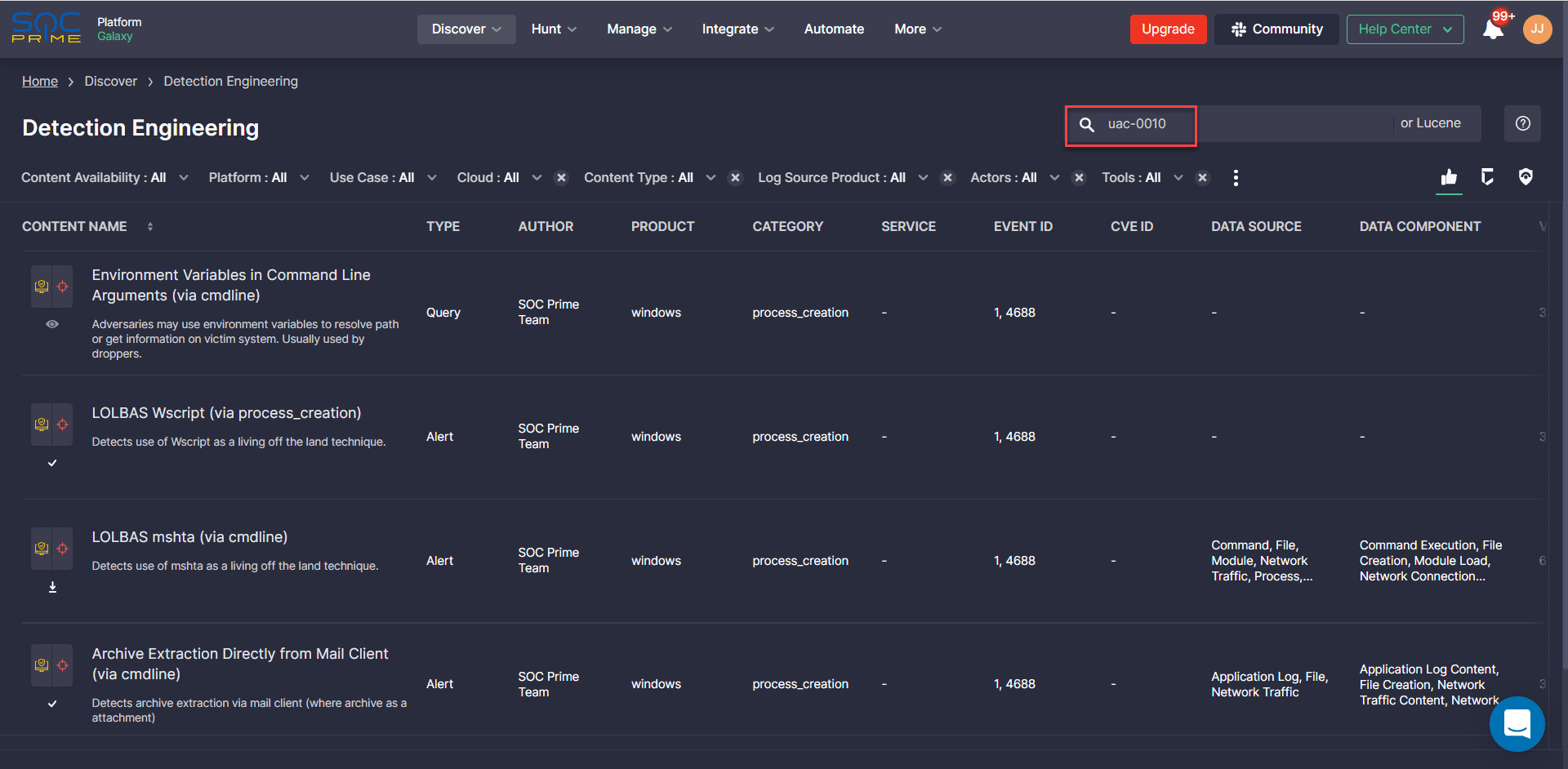
To help organizations proactively defend against phishing cyber-attacks by the Armageddon APT (UAC-0010), SOC Prime offers a unique set of dedicated Sigma rules, including alerts and queries, filtered by an appropriate custom tag #UAC-0010 to simplify the content search:
Sigma rules to detect malicious activity by Armageddon Group (UAC-0010)
Detection Engineers can reach this comprehensive list of curated content items after logging into the SOC Prime’s platform with their existing account and then choose the most relevant rules by use case, content type, log source product or category, Event ID along with other data sources tailored to their environment needs.
MITRE ATT&CK® Context
For an insightful analysis focused on the adversary behavior patterns, all Sigma rules to detect the malicious activity of the Armageddon/UAC-0010 hacking collective are aligned with MITRE ATT&CK addressing the corresponding tactics and techniques:




